Soc Mdr Edr Ndr And Xdr Pdf Computer Security Security

Soc Mdr Edr Ndr And Xdr Pdf Computer Security Security Soc, mdr, edr, ndr and xdr free download as pdf file (.pdf), text file (.txt) or read online for free. Edr, mdr, and xdr can alleviate challenges most small business cybersecurity teams face, such as alert fatigue and limited resources. although detection and response tools share similar purposes, they are not all equal.

Edr Vs Xdr Vs Siem Vs Mdr Vs Soar Pdf Security Computer Security Xdr combines the concepts of edr and siem to provide a more holistic solution that adds the capability of direct response actions. where siem focuses on log collection and data analysis, xdr offers greater insight into threats and adds the ability to automate response actions directly. Most msps encounter three cybersecurity solutions: endpoint detection and response (edr), managed detection and response (mdr), and extended detection and response (xdr). let’s examine each solution to determine which is the best fit. Navigating xdr, edr, ndr, and siem requires understanding the specific roles of each technology. these platforms offer unique advantages, addressing different aspects of security. With complex titles like edr, siem, xdr, mdr, and mxdr—it can be confusing to determine what capabilities each provides and when to leverage them for your organisation.
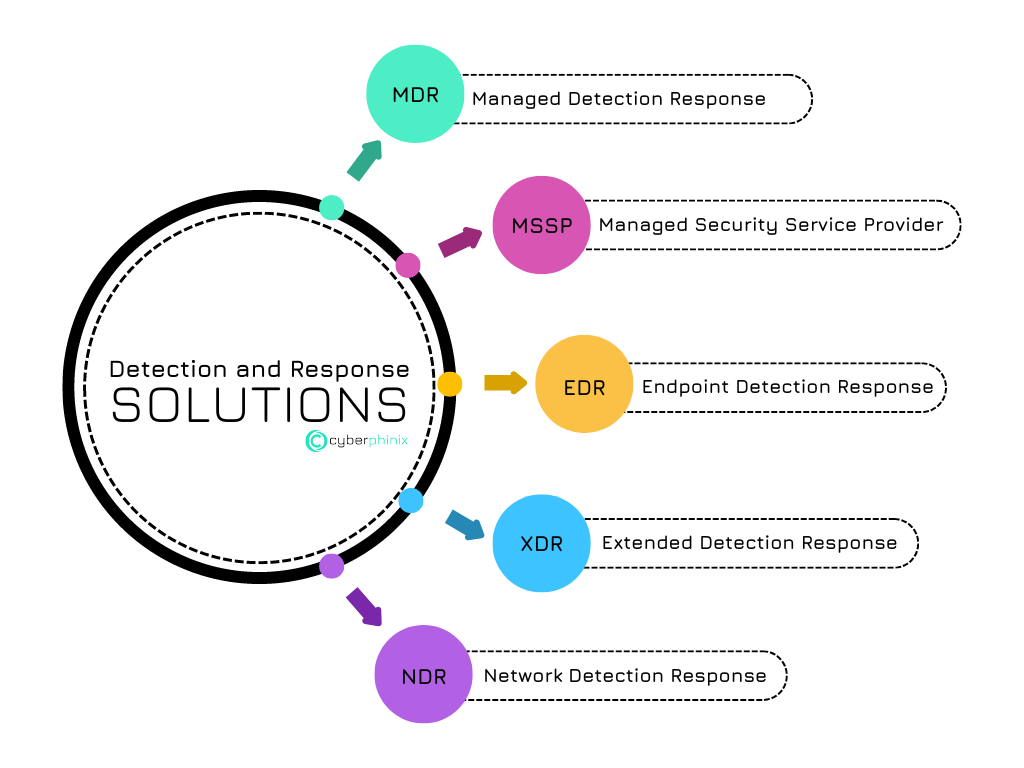
Mdr Mssp Edr Xdr Ndr Explained рџ ї Navigating xdr, edr, ndr, and siem requires understanding the specific roles of each technology. these platforms offer unique advantages, addressing different aspects of security. With complex titles like edr, siem, xdr, mdr, and mxdr—it can be confusing to determine what capabilities each provides and when to leverage them for your organisation. In this white paper, we review three modern approaches to threat detection and response — endpoint detection and response (edr), network detection and response (ndr), and extended detection and response (xdr) — and discuss the benefits and challenges of each. Edr vs. itdr vs. mdr vs. xdr detection response tools can be acronym overload. think of edr as the “core” ofering, with various additional layers adding their own benefits. The majority of small to medium organizations prefer to outsource complex security operations and services such as endpoint detection and response (edr), managed detection and response (mdr), or extended detection and response (xdr). Siem, soar, xdr, edr, and mdr are all cybersecurity solutions that aim to provide advanced threat detection, analytics, and response capabilities to organizations.

Balanced A Complete Guide To Xdr Soc Mdr And Edr In this white paper, we review three modern approaches to threat detection and response — endpoint detection and response (edr), network detection and response (ndr), and extended detection and response (xdr) — and discuss the benefits and challenges of each. Edr vs. itdr vs. mdr vs. xdr detection response tools can be acronym overload. think of edr as the “core” ofering, with various additional layers adding their own benefits. The majority of small to medium organizations prefer to outsource complex security operations and services such as endpoint detection and response (edr), managed detection and response (mdr), or extended detection and response (xdr). Siem, soar, xdr, edr, and mdr are all cybersecurity solutions that aim to provide advanced threat detection, analytics, and response capabilities to organizations.

Understanding Ndr Mdr Xdr Edr Siem And Soar In Cybersecurity The majority of small to medium organizations prefer to outsource complex security operations and services such as endpoint detection and response (edr), managed detection and response (mdr), or extended detection and response (xdr). Siem, soar, xdr, edr, and mdr are all cybersecurity solutions that aim to provide advanced threat detection, analytics, and response capabilities to organizations.

Mdr Vs Xdr Vs Siem Vs Soc Armorpoint
Comments are closed.