Sliver C2 Framework Tutorial Complete Guide From Installation To Post Exploitation
Hackers Using Sliver Framework Instead Of Cobalt Strike Metasploit Learn how to use sliver the open source c2 framework by bishop fox for red team operations and penetration testing. this complete tutorial covers everything from installation to. We’ll cover the fundamentals of setting up sliver c2, exploring its advanced features, and providing a detailed walkthrough of a simulated attack scenario.

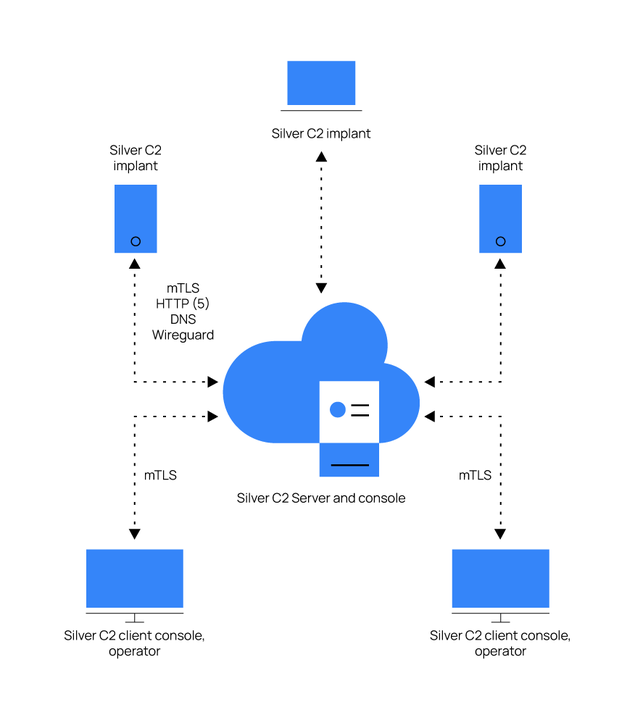
Roguesliver Disrupt Campaigns Using The Sliver C2 Framework This guide documents how to use the sliver c2 framework both containerized and direct installation. it covers docker builds across architectures, server deployment, implant generation, and operational commands for effective penetration testing. Welcome to the sliver wiki!. A command and control (c2) framework is a crucial component in cybersecurity, often used by both ethical hackers and malicious attackers. Sliver's implants support c2 over mutual tls (mtls), wireguard, http (s), and dns and are dynamically compiled with per binary asymmetric encryption keys. the server and client support macos, windows, and linux.
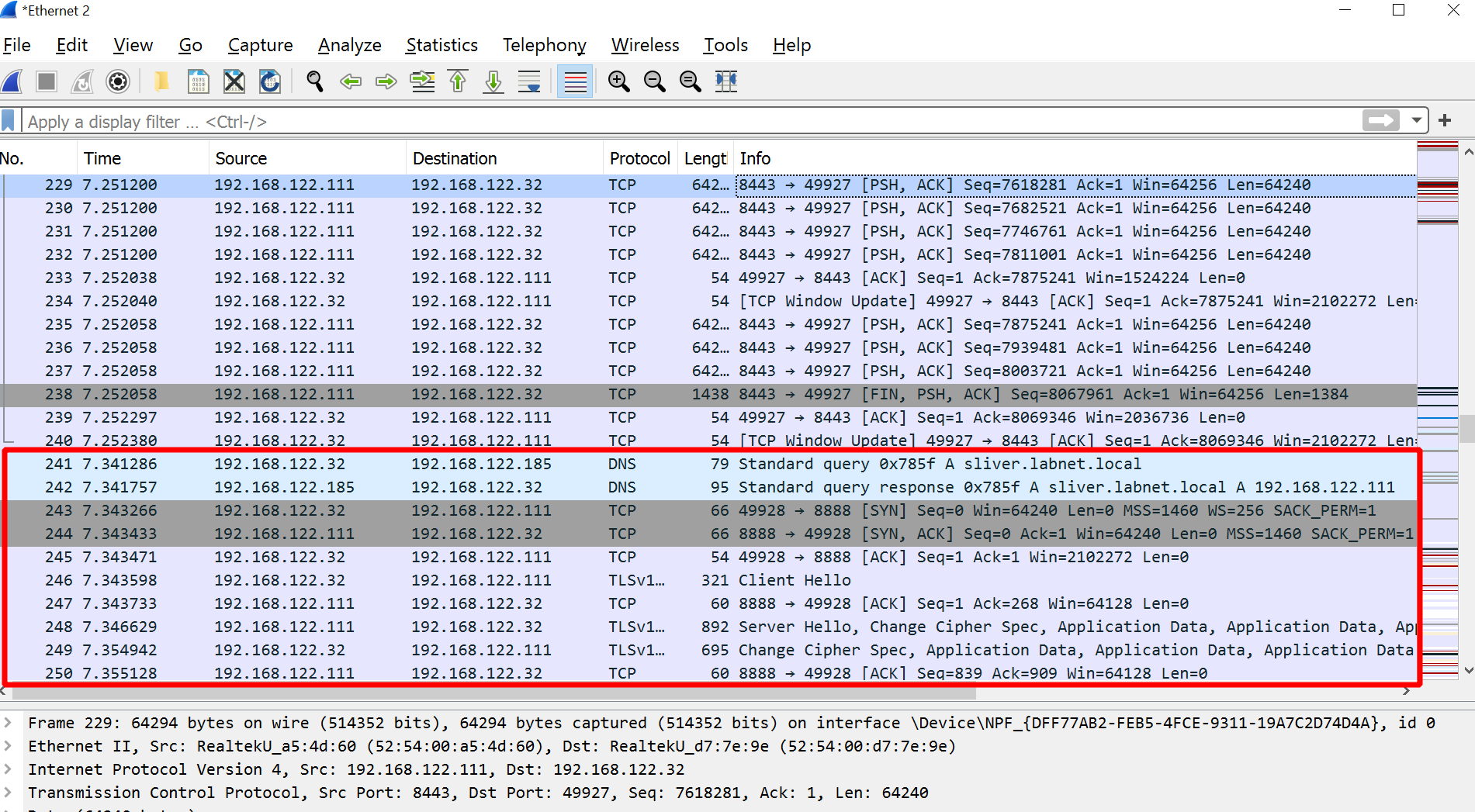
Detecting Sliver C2 Framework With Wazuh A command and control (c2) framework is a crucial component in cybersecurity, often used by both ethical hackers and malicious attackers. Sliver's implants support c2 over mutual tls (mtls), wireguard, http (s), and dns and are dynamically compiled with per binary asymmetric encryption keys. the server and client support macos, windows, and linux. This post is a technical walkthrough of sliver c2, with a focus on building from source, configuring an mtls listener, staging shellcode payloads, and performing a basic remote process injection. Now we can run the sliver server and it will drop us in a console where we can do basically everything we expect from a c2, like generating payloads, beacons, start listeners, interact with our beacons, etc…. Learn essential sliver commands for implant generation, session management, and post exploitation. explore evasion techniques and integration with metasploit’s msfvenom. A comprehensive guide to installing, configuring, and using sliver c2 framework for command and control operations in penetration testing engagements.
Detecting Sliver C2 Framework With Wazuh This post is a technical walkthrough of sliver c2, with a focus on building from source, configuring an mtls listener, staging shellcode payloads, and performing a basic remote process injection. Now we can run the sliver server and it will drop us in a console where we can do basically everything we expect from a c2, like generating payloads, beacons, start listeners, interact with our beacons, etc…. Learn essential sliver commands for implant generation, session management, and post exploitation. explore evasion techniques and integration with metasploit’s msfvenom. A comprehensive guide to installing, configuring, and using sliver c2 framework for command and control operations in penetration testing engagements.
Learning Sliver C2 06 Stagers Basics Text Plain Learn essential sliver commands for implant generation, session management, and post exploitation. explore evasion techniques and integration with metasploit’s msfvenom. A comprehensive guide to installing, configuring, and using sliver c2 framework for command and control operations in penetration testing engagements.
Comments are closed.