Simplifying Zero Trust For User Based Security

Zero Trust Security Models Overview Pdf Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. The upgraded suite is designed to provide comprehensive workplace security and help organizations implement zero trust access. this ensures security for the hybrid work force and delivers seamless and secure access to applications and data from anywhere, on any device.

Embracing A Zero Trust Security Model Pdf Computer Security Security The zero trust model significantly enhances overall security by continuously verifying every user and device, which greatly reduces risk. access is granted strictly on a need to know basis. This research article examines the concept of zero trust architecture and its effectiveness in protecting against insider threats and advanced persistent threats (apts) in modern network. Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization. Zero trust is a modern security model that requires continuous authentication and validation of all users and devices before granting access. it eliminates implicit trust in network security, using segmentation, threat prevention, and granular access control to protect systems.

Implementing Zero Trust Security A Guide For Modern Businesses Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization. Zero trust is a modern security model that requires continuous authentication and validation of all users and devices before granting access. it eliminates implicit trust in network security, using segmentation, threat prevention, and granular access control to protect systems. Tl;dr this guide goes over the advantages of using a zero trust architecture and how it may assist you in developing a safe framework. a zero trust architecture is necessary to secure data and provide users access to the resources they require to fulfill their tasks. Organizations must adopt a zero trust security model, one that assumes no user or device is inherently trustworthy, even inside the network. in this guide, we break down the key principles of zero trust, steps to implement it, and how swimlane helps automate and scale zero trust strategies. Traditional security models that trust users inside the network perimeter have failed spectacularly. the zero trust security model basics flip this assumption on its head: trust no one, verify everything. this approach assumes every user, device, and network component could be compromised. Rather than presuming that internal entities are safe while external ones are suspect, zero trust mandates rigorous identity verification for every user and device before granting access to critical resources.
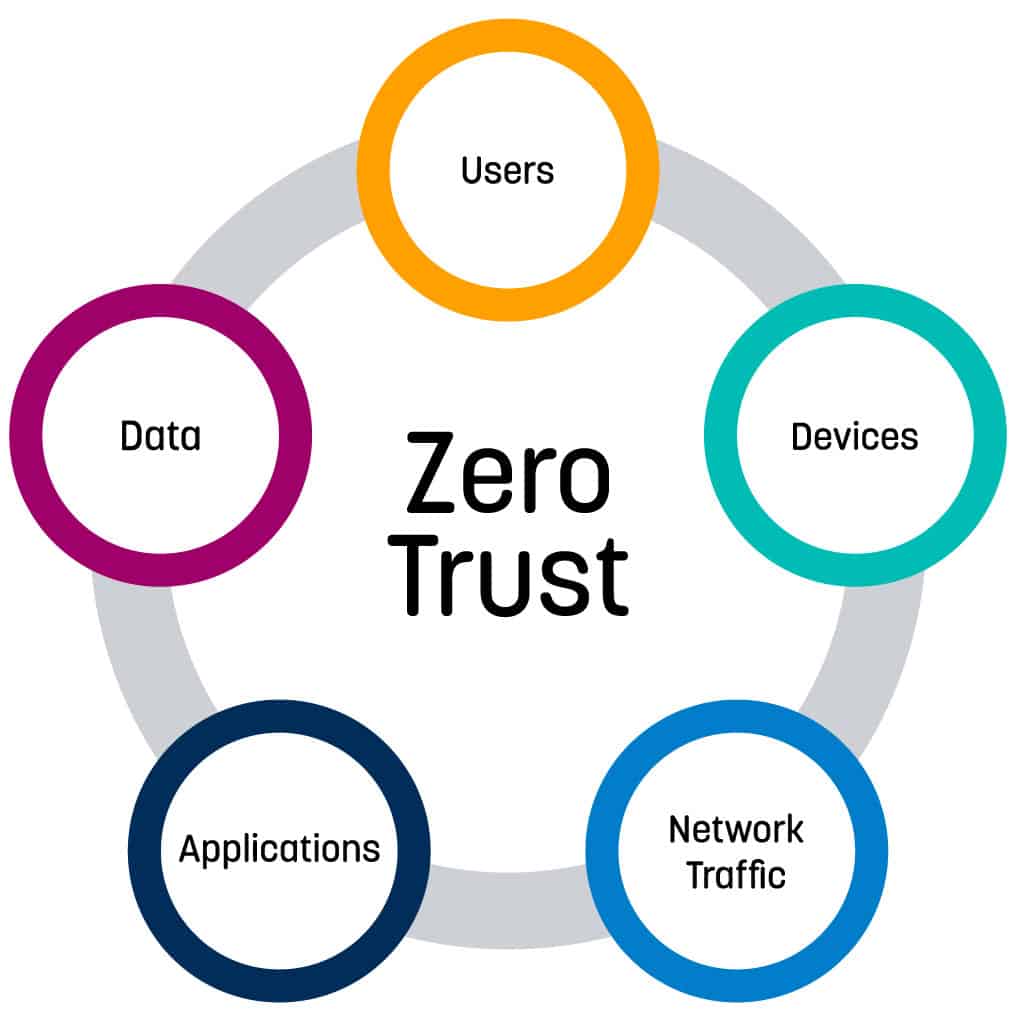
Embracing A Zero Trust Security Model Logrhythm Tl;dr this guide goes over the advantages of using a zero trust architecture and how it may assist you in developing a safe framework. a zero trust architecture is necessary to secure data and provide users access to the resources they require to fulfill their tasks. Organizations must adopt a zero trust security model, one that assumes no user or device is inherently trustworthy, even inside the network. in this guide, we break down the key principles of zero trust, steps to implement it, and how swimlane helps automate and scale zero trust strategies. Traditional security models that trust users inside the network perimeter have failed spectacularly. the zero trust security model basics flip this assumption on its head: trust no one, verify everything. this approach assumes every user, device, and network component could be compromised. Rather than presuming that internal entities are safe while external ones are suspect, zero trust mandates rigorous identity verification for every user and device before granting access to critical resources.

Principles Of Zero Trust Security Cwsi Traditional security models that trust users inside the network perimeter have failed spectacularly. the zero trust security model basics flip this assumption on its head: trust no one, verify everything. this approach assumes every user, device, and network component could be compromised. Rather than presuming that internal entities are safe while external ones are suspect, zero trust mandates rigorous identity verification for every user and device before granting access to critical resources.
Comments are closed.