Sim Swap Scams

Sim Card Swap Scams National Cybersecurity Alliance Learn what sim swapping is, how it works, and how you can protect yourself from sim swap scams. Sim swapping is when a scammer takes control of your phone number. the sim can then be used to intercept text based account verification for your bank or social media accounts. warning signs include sudden loss of service or login lockouts. you can stay protected with carrier pins and stronger 2fa.

Sim Card Swap Scams National Cybersecurity Alliance In south korea, various alleged incidents of sim swapping attacks have been documented since the beginning of 2022. the common pattern includes victims facing abrupt disruptions in their mobile services, coupled with a notification suggesting a change. Sim swapping fraud occurs when criminals gain control of a victim's mobile phone number by tricking the network provider into transferring it to a device controlled by the fraudster. this. Sim swapping lets scammers take over your phone number to intercept calls, texts and security codes. criminals use stolen personal data to convince carriers to transfer your number to their device. warning signs include sudden loss of service, account lockouts and unauthorized financial activity. Sim swapping, also known as sim splitting, simjacking, or sim hijacking, is a technique used by fraudsters to get control of your phone number. with your phone number, hackers can take advantage of two factor authentication to gain access to your bank accounts, social media accounts, and more.

Sim Card Swap Scams National Cybersecurity Alliance Sim swapping lets scammers take over your phone number to intercept calls, texts and security codes. criminals use stolen personal data to convince carriers to transfer your number to their device. warning signs include sudden loss of service, account lockouts and unauthorized financial activity. Sim swapping, also known as sim splitting, simjacking, or sim hijacking, is a technique used by fraudsters to get control of your phone number. with your phone number, hackers can take advantage of two factor authentication to gain access to your bank accounts, social media accounts, and more. Learn how sim swap attacks hijack phone numbers, signs to watch for, and the carrier and account steps to prevent takeovers and report fraud. Learn about sim swap fraud, where scammers hijack phone numbers to gain control of personal accounts. discover tactics used, warning signs, and tips to protect yourself. So how do scammers pull off a sim card swap like this? they may call your cell phone service provider and say your phone was lost or damaged. then they ask the provider to activate a new sim card connected to your phone number on a new phone — a phone they own. First, a criminal must scam your wireless carrier into transferring your number to a sim card under their control. once they control your phone number, the scammer uses it to help crack into your sensitive accounts, like banking, that use multi factor authentication through sms text message.

Sim Card Swap Scams National Cybersecurity Alliance Learn how sim swap attacks hijack phone numbers, signs to watch for, and the carrier and account steps to prevent takeovers and report fraud. Learn about sim swap fraud, where scammers hijack phone numbers to gain control of personal accounts. discover tactics used, warning signs, and tips to protect yourself. So how do scammers pull off a sim card swap like this? they may call your cell phone service provider and say your phone was lost or damaged. then they ask the provider to activate a new sim card connected to your phone number on a new phone — a phone they own. First, a criminal must scam your wireless carrier into transferring your number to a sim card under their control. once they control your phone number, the scammer uses it to help crack into your sensitive accounts, like banking, that use multi factor authentication through sms text message.
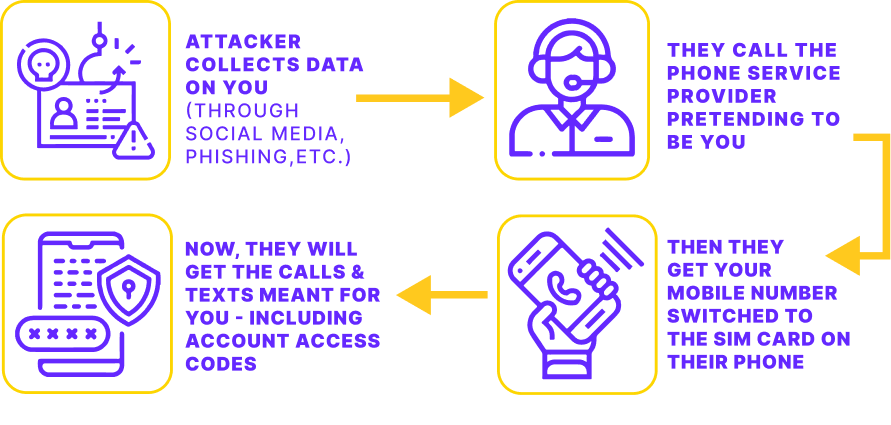
Sim Swap Scams So how do scammers pull off a sim card swap like this? they may call your cell phone service provider and say your phone was lost or damaged. then they ask the provider to activate a new sim card connected to your phone number on a new phone — a phone they own. First, a criminal must scam your wireless carrier into transferring your number to a sim card under their control. once they control your phone number, the scammer uses it to help crack into your sensitive accounts, like banking, that use multi factor authentication through sms text message.
Comments are closed.