Sim Swap Identity Theft 8 Steps To Protect Your Phone Number

Sim Swapping Identity Theft And How To Protect Your Accounts Learn about sim swap fraud, where scammers hijack phone numbers to gain control of personal accounts. discover tactics used, warning signs, and tips to protect yourself. Getting swamped with spam texts because scammers know your number is bad enough. but if a scammer gains control of your phone number by hacking your sim, the consequences could be far more serious. here are eight tips for what to do if a scammer has your phone number.

Protect Your Account Sim Swap Hack Smart Contract Audits With a sim swapping attack, scammers hijack your phone number to gain access to apps on your phone—including banking apps. these tips can help you safeguard your most private information. Learn how to prevent sim swap attacks and protect your mobile number from cybercriminals. discover practical tips, warning signs, and steps to secure your accounts and avoid identity theft. Learn what is sim cloning, how it works & how to protect yourself. complete guide to prevent sim cloning attacks with security tips, 2fa, strong pins & device protection. Protect your phone from sim swapping attacks. learn how to lock your sim, enable 2fa, and use your carrier tools to stop hackers.

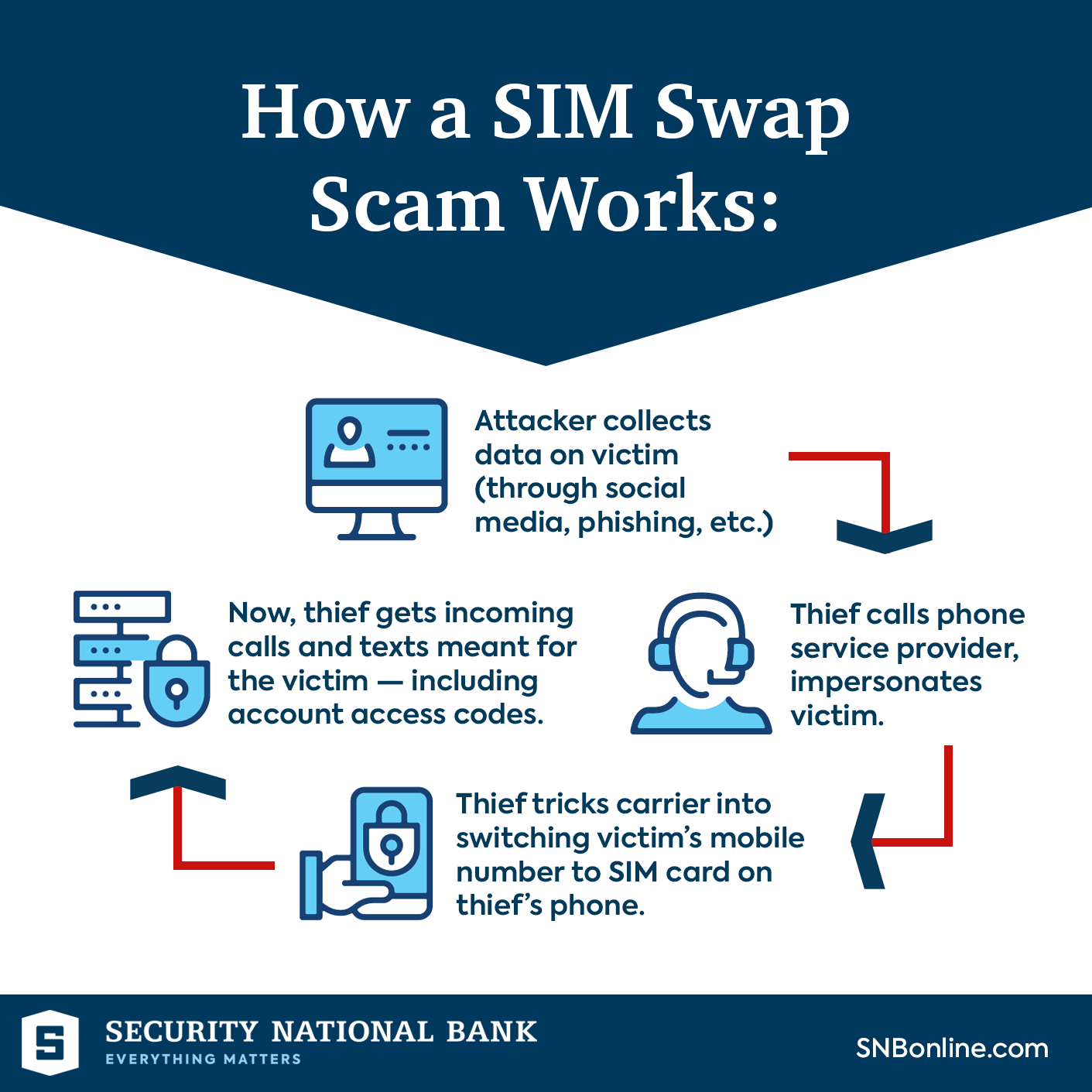
How To Protect Your Customers From Sim Card Attacks The New Identity Learn what is sim cloning, how it works & how to protect yourself. complete guide to prevent sim cloning attacks with security tips, 2fa, strong pins & device protection. Protect your phone from sim swapping attacks. learn how to lock your sim, enable 2fa, and use your carrier tools to stop hackers. Even the best laid security plans can go awry if you fall victim to a sim swapping attack. here's how to protect yourself. Sim swapping lets scammers take over your phone number to intercept security codes and access your accounts. learn the warning signs and simple steps to protect yourself. Sim swap attacks—sim hijacking or sim splitting—occur when a malicious actor fraudulently transfers your mobile phone number to a new sim card they control. Limit sharing your phone number. your phone number is the key to a sim swap. the fewer people who have it, the harder it is for scammers to target you. enable multi factor authentication (mfa) whenever possible. authenticator apps create one time passcodes that are hard to intercept — even if a scammer has your phone number.

Protect Your Mobile And Prevent Sim Swap Scams Telecom Review Africa Even the best laid security plans can go awry if you fall victim to a sim swapping attack. here's how to protect yourself. Sim swapping lets scammers take over your phone number to intercept security codes and access your accounts. learn the warning signs and simple steps to protect yourself. Sim swap attacks—sim hijacking or sim splitting—occur when a malicious actor fraudulently transfers your mobile phone number to a new sim card they control. Limit sharing your phone number. your phone number is the key to a sim swap. the fewer people who have it, the harder it is for scammers to target you. enable multi factor authentication (mfa) whenever possible. authenticator apps create one time passcodes that are hard to intercept — even if a scammer has your phone number.
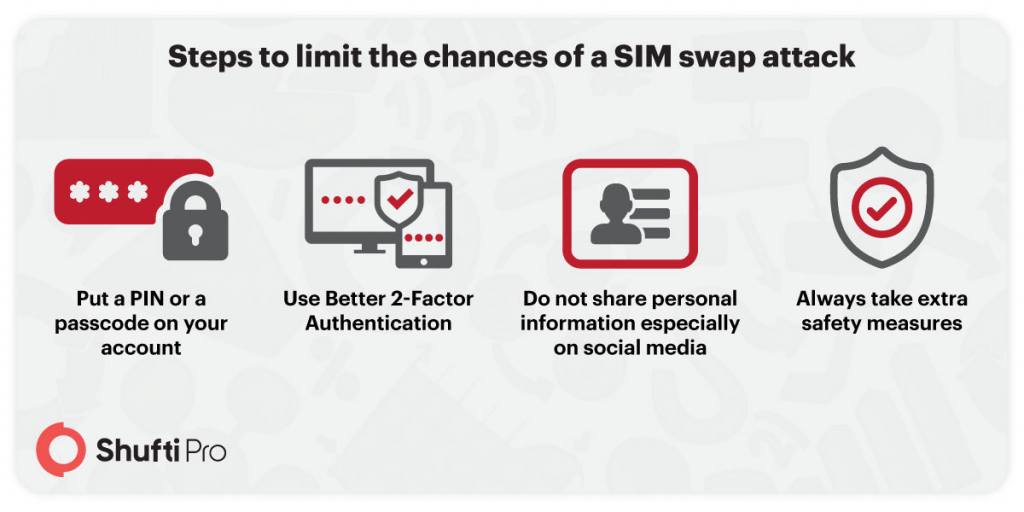
Sim Swap Fraud A New Battle In The War Of Your Identity Sim swap attacks—sim hijacking or sim splitting—occur when a malicious actor fraudulently transfers your mobile phone number to a new sim card they control. Limit sharing your phone number. your phone number is the key to a sim swap. the fewer people who have it, the harder it is for scammers to target you. enable multi factor authentication (mfa) whenever possible. authenticator apps create one time passcodes that are hard to intercept — even if a scammer has your phone number.
Sim Swap Fraud How To Protect Yourself
Comments are closed.