Sim Swap Attacks More Common How To Protect Yourself
Sim Swap Attacks Certik Quest Even the best laid security plans can go awry if you fall victim to a sim swapping attack. here's how to protect yourself. Your phone number is tied to many valuable accounts, and a breach could be devastating. here's how you can protect yourself from a sim swap.
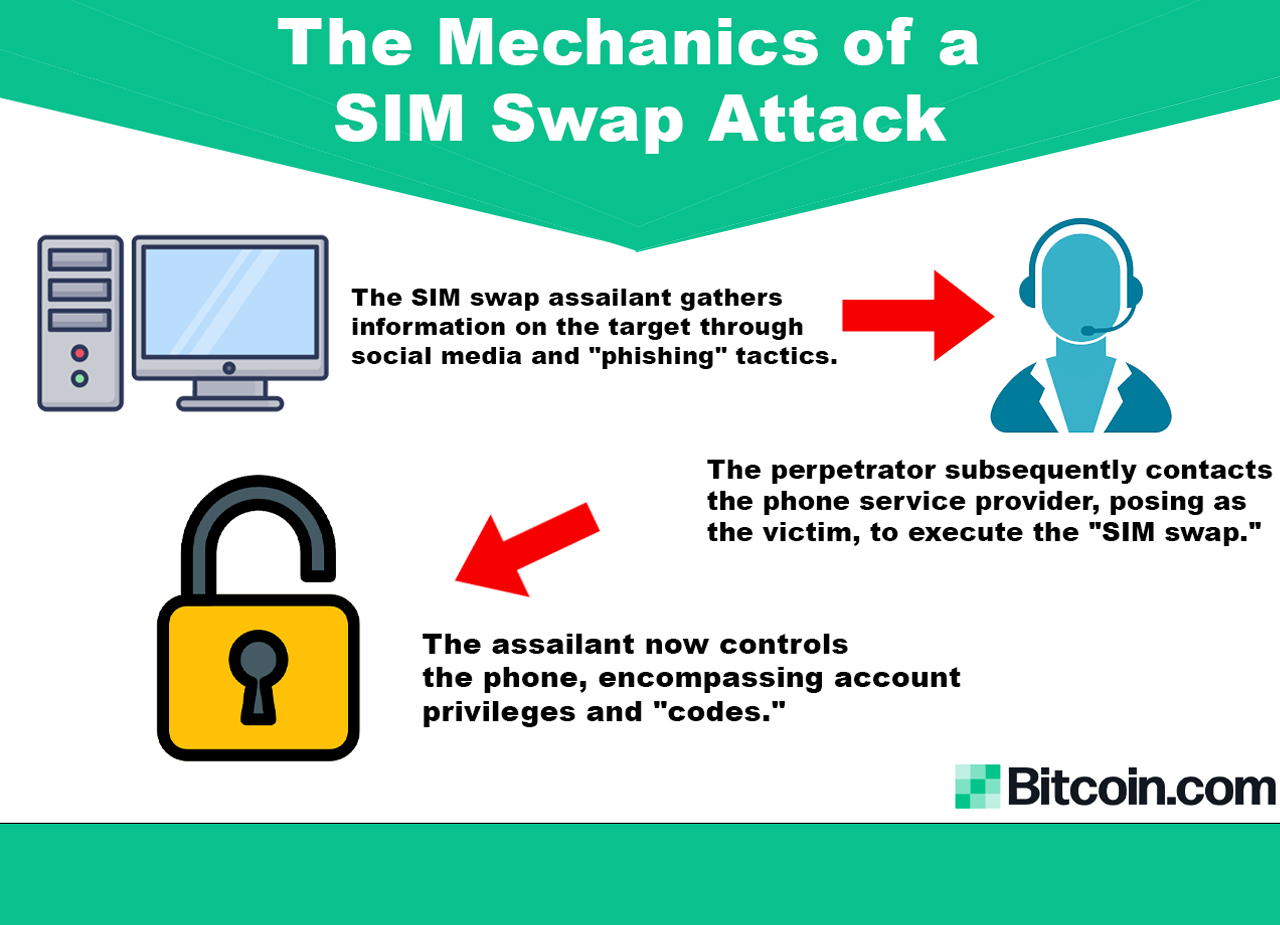
Shielding Your Digital Realm How To Protect Yourself And Crypto From Protect your phone from sim swapping attacks. learn how to lock your sim, enable 2fa, and use your carrier tools to stop hackers. In this comprehensive guide, i’ll break down what sim swapping is, real world attack examples, why it’s so easy for criminals, and most importantly – what you can do to protect yourself. If you're serious about avoiding a sim swap attack, you need a plan. this isn't just about setting up 2fa once it's about rebuilding your digital identity architecture to assume attackers are watching. Learn what sim swapping is, how sim swap fraud works, signs of an attack, and key steps individuals and businesses can take to prevent it.

Protecting Yourself From Sim Swap Attacks Unlockbase If you're serious about avoiding a sim swap attack, you need a plan. this isn't just about setting up 2fa once it's about rebuilding your digital identity architecture to assume attackers are watching. Learn what sim swapping is, how sim swap fraud works, signs of an attack, and key steps individuals and businesses can take to prevent it. This guide explores sim swapping in depth, including how it works, real world incidents, what makes people vulnerable, legal implications, and how users and businesses can protect themselves. In this article, we’ll dive deep into how sim swap attacks work, the risks associated with them, and, most importantly, how you can protect yourself from falling victim to this increasingly common form of hacking. Learn about sim swap fraud, where scammers hijack phone numbers to gain control of personal accounts. discover tactics used, warning signs, and tips to protect yourself. Sim swaps are a serious security threat: find out how to protect yourself and what to do if you get targeted.

Protecting Yourself From Sim Swap Attacks Unlockbase This guide explores sim swapping in depth, including how it works, real world incidents, what makes people vulnerable, legal implications, and how users and businesses can protect themselves. In this article, we’ll dive deep into how sim swap attacks work, the risks associated with them, and, most importantly, how you can protect yourself from falling victim to this increasingly common form of hacking. Learn about sim swap fraud, where scammers hijack phone numbers to gain control of personal accounts. discover tactics used, warning signs, and tips to protect yourself. Sim swaps are a serious security threat: find out how to protect yourself and what to do if you get targeted.

Protecting Yourself From Sim Swap Attacks Unlockbase Learn about sim swap fraud, where scammers hijack phone numbers to gain control of personal accounts. discover tactics used, warning signs, and tips to protect yourself. Sim swaps are a serious security threat: find out how to protect yourself and what to do if you get targeted.
Comments are closed.