Sim Swap Attacks Certik Quest
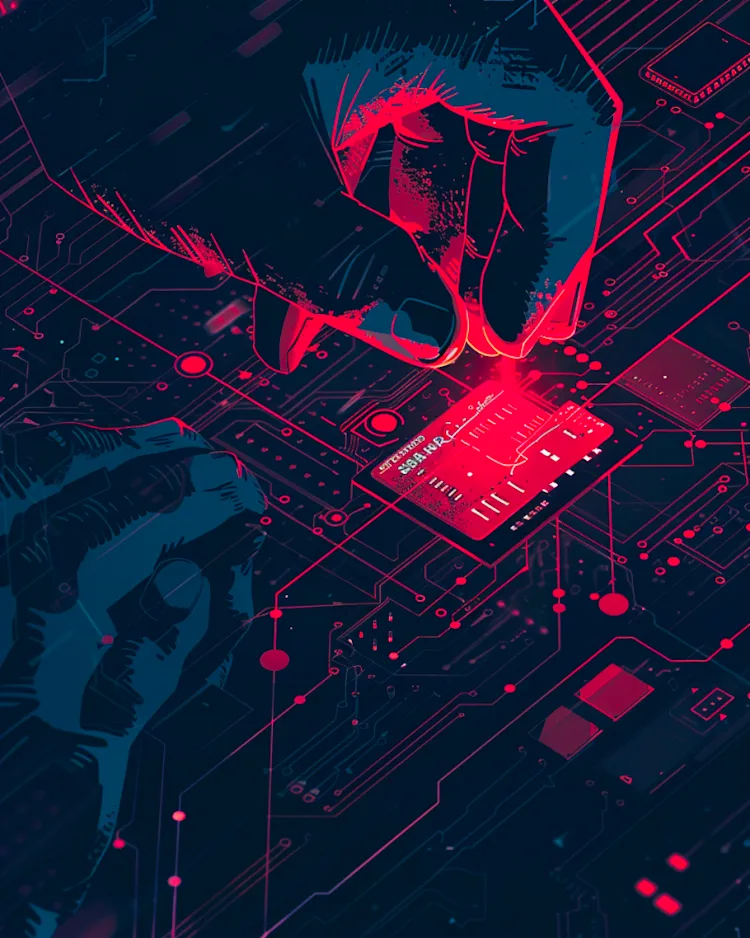
Sim Swap Attacks Certik Quest This quest explains sim swapping, a method used by attackers, especially in the web3 space, to steal from their victims. learn what a sim swap attack is, how it's carried out, and how to protect yourself from it. Learn what sim swapping is, how sim swap fraud works, signs of an attack, and key steps individuals and businesses can take to prevent it.
Sim Swap Attacks Certik Quest Sim 스왑 공격 이 퀘스트에서는 특히 웹 3.0 공간에서 공격자가 피해자의 정보를 훔치기 위해 사용하는 방법인 sim 스와핑에 대해 설명합니다. sim 스왑 공격이 무엇인지, 어떻게 수행되는지, 어떻게 자신을 보호할 수 있는지 알아보세요. Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . Learn how a sim swap attack, a type of identity fraud in which a user's phone number is transferred to a different sim card, works and how to prevent it. In south korea, various alleged incidents of sim swapping attacks have been documented since the beginning of 2022. the common pattern includes victims facing abrupt disruptions in their mobile services, coupled with a notification suggesting a change.

Understanding And Preventing Sybil Attacks Certik Quest Learn how a sim swap attack, a type of identity fraud in which a user's phone number is transferred to a different sim card, works and how to prevent it. In south korea, various alleged incidents of sim swapping attacks have been documented since the beginning of 2022. the common pattern includes victims facing abrupt disruptions in their mobile services, coupled with a notification suggesting a change. How can you prevent sim swapping? to avoid a sim jacking, phone owners can implement simple security measures like setting up pins and security questions with their phone companies or using standalone authentication apps instead of two factor authentication linked to a phone number. Quiz : sim swap attacks. answer 1 : searching the dark web to find your previously leaked information, browsing through your public social media accounts. answer 2 : use authentication apps like okta or authy. quiz : protecting yourself from discord scams. quiz : hackers infiltrating crypto job boards. quiz : setting up a security war room. How hard is it to perform a sim swap hack? according to certik’s exec, sim swap hacking can often be done with information that is publicly available or that can be obtained through social engineering. Sim swap attacks compromise your phone number. discover what sim jacking is, how it works, and how to prevent sim swaps.
Understanding And Preventing Sybil Attacks Certik Quest How can you prevent sim swapping? to avoid a sim jacking, phone owners can implement simple security measures like setting up pins and security questions with their phone companies or using standalone authentication apps instead of two factor authentication linked to a phone number. Quiz : sim swap attacks. answer 1 : searching the dark web to find your previously leaked information, browsing through your public social media accounts. answer 2 : use authentication apps like okta or authy. quiz : protecting yourself from discord scams. quiz : hackers infiltrating crypto job boards. quiz : setting up a security war room. How hard is it to perform a sim swap hack? according to certik’s exec, sim swap hacking can often be done with information that is publicly available or that can be obtained through social engineering. Sim swap attacks compromise your phone number. discover what sim jacking is, how it works, and how to prevent sim swaps.
Comments are closed.