Sign Your Container Images With Cosign Github Actions And Github Container Registry How To

Sign Your Container Images With Cosign Github Actions And Github Sign a container image with cosign and github actions alright, now that we have our keys set up, let’s see how we can sign our images from within a github actions workflow. That’s all you have to do to sign your container image in github actions and store it in github packages (or any of the other container registries cosign supports as well).
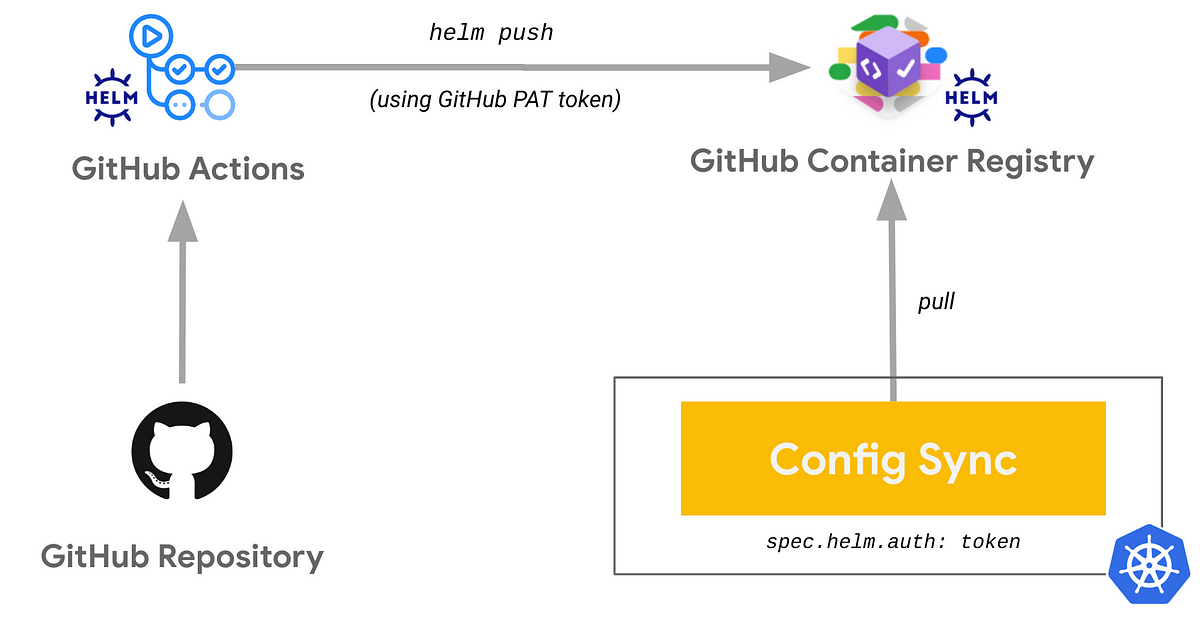
Ci Gitops With Helm Github Actions Github Container Registry And Cosign will then store the signature and certificate in the rekor transparency log, and upload the signature to the oci registry alongside the image you're signing. First we will look at how to setup a github workflow using github actions to build multi architecture container images with buildah and push them to a registry with podman. then we will sign those images with cosign (sigstore) and detail what is needed to configure signature validation on the host. Learn to sign, verify, and secure docker images in ci cd using cosign and github actions. practical, production grade walkthrough. In this post, we’ll explore how to sign container images using cosign from the sigstore project and verify them using github’s oidc token. cosign is a tool designed to make signatures an invisible part of the infrastructure.

Continuous Deployment For Azure Container Apps Using Github Actions Learn to sign, verify, and secure docker images in ci cd using cosign and github actions. practical, production grade walkthrough. In this post, we’ll explore how to sign container images using cosign from the sigstore project and verify them using github’s oidc token. cosign is a tool designed to make signatures an invisible part of the infrastructure. Learn how to sign and verify container images with cosign to establish trust in your software supply chain and prevent unauthorized image deployment. Cosign is a free open source project that provides keyless signatures for container images. it enables users to sign container images without requiring access to any keys or certificates. this guide will walk you through the steps to use cosign keyless signatures with github actions. In this demonstration, we’ll be using github actions to perform keyless signing on a sample container. in this example, we’ll use a django container that displays a generic “hello, world” style landing page. This post walks through signing a container image with keyless signing using oidc, verifying the signature locally, and wiring signature verification into a github actions pipeline so that only signed images can reach your deployment stage.

Sign Your Container Images With Cosign Github Actions And Github Learn how to sign and verify container images with cosign to establish trust in your software supply chain and prevent unauthorized image deployment. Cosign is a free open source project that provides keyless signatures for container images. it enables users to sign container images without requiring access to any keys or certificates. this guide will walk you through the steps to use cosign keyless signatures with github actions. In this demonstration, we’ll be using github actions to perform keyless signing on a sample container. in this example, we’ll use a django container that displays a generic “hello, world” style landing page. This post walks through signing a container image with keyless signing using oidc, verifying the signature locally, and wiring signature verification into a github actions pipeline so that only signed images can reach your deployment stage.

Sign Your Container Images With Cosign Github Actions And Github In this demonstration, we’ll be using github actions to perform keyless signing on a sample container. in this example, we’ll use a django container that displays a generic “hello, world” style landing page. This post walks through signing a container image with keyless signing using oidc, verifying the signature locally, and wiring signature verification into a github actions pipeline so that only signed images can reach your deployment stage.
Comments are closed.