Side Channel Security Transient Execution And Fault Attacks

Hardware Vulnerability In Intel Processors Kaspersky Official Blog In this paper, we systematically examine risc v microarchitecture security issues and put forward a combined side channel and transient execution attack scheme. Ability to find software and hardware design patterns that may expose secrets via transient execution. understand risks associated with transient execution attacks and how these can be mitigated.
Current Projects Secure Intelligent And Efficient Systems Lab Explore advanced side channel security, including transient execution and fault attacks. gain hands on experience implementing attacks, understanding microarchitecture, and learning mitigation strategies. Pmp provides a trusted execution environment (tee) that isolates secure and insecure applications. in this study, we propose a side channel assisted fault injection attack to bypass. This series equips you with the skills and mindset to detect, understand, and mitigate side channels and fault attacks, preparing you to secure modern computing systems at all levels. How to apply security principles and industry best practices to help protect your code and systems from potential transient execution attacks.
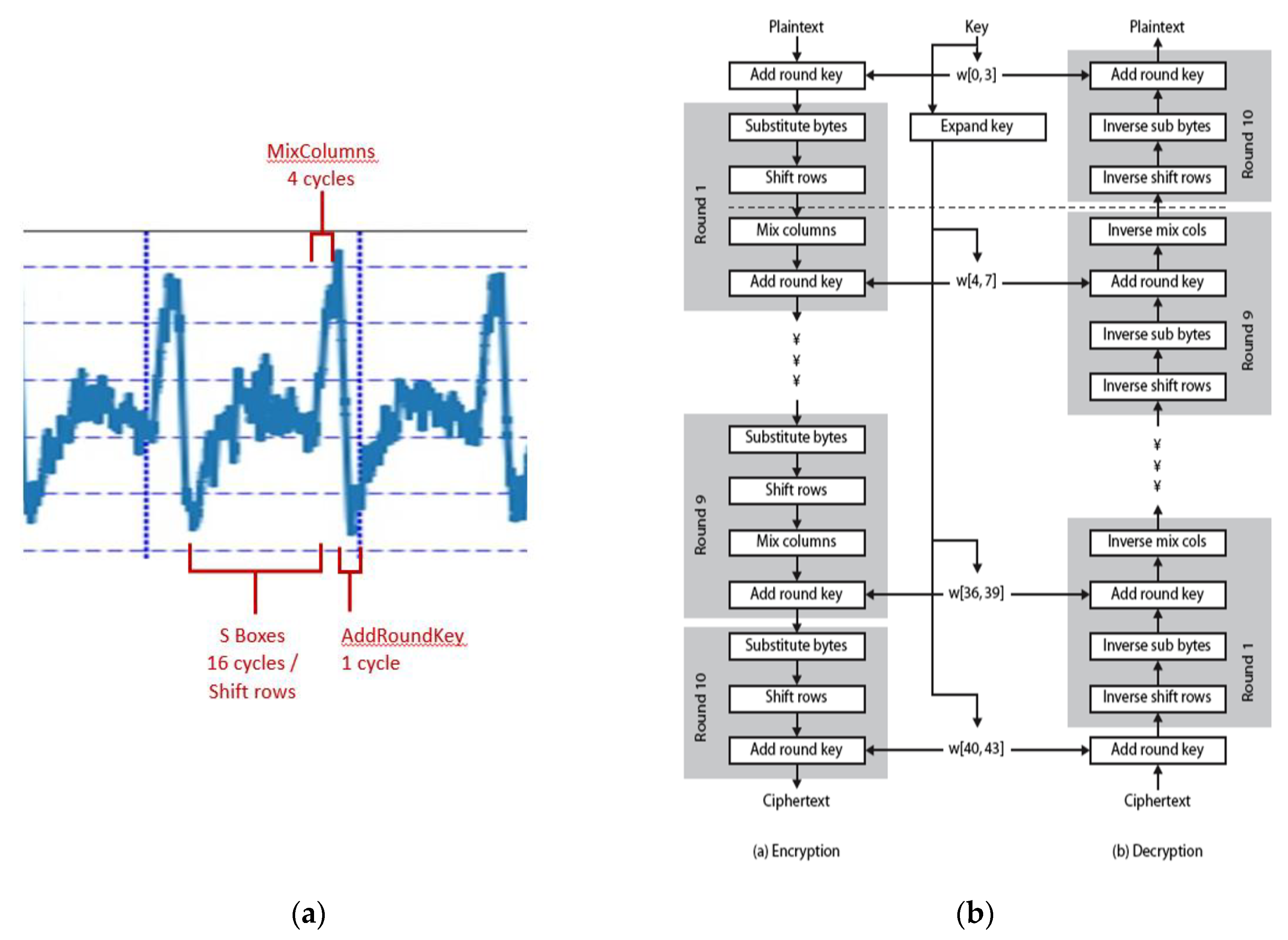
Power Side Channel Attack Analysis A Review Of 20 Years Of Study For This series equips you with the skills and mindset to detect, understand, and mitigate side channels and fault attacks, preparing you to secure modern computing systems at all levels. How to apply security principles and industry best practices to help protect your code and systems from potential transient execution attacks. Based on this vulnerability, we propose the pmu spill attack, a new kind of side channel attack that enables attackers to maliciously leak secret data in transient executions. During the delay, if transient microarchitectural state (e.g. cache) has been created for unauthorized value, it can be leaked using existing side channel attacks. In section ii, we introduce the background knowledge of side channel attacks and transient execution attacks. in section iii, we present the details of the attack. Noise is just someone else’s data. fill buffers may retain stale data from prior memory requests until a new memory request overwrites the fill buffer. under certain conditions, the fill buffer may speculatively forward data, including stale data, to a load operation that will cause a fault assist. io instructions, syscall, . . .
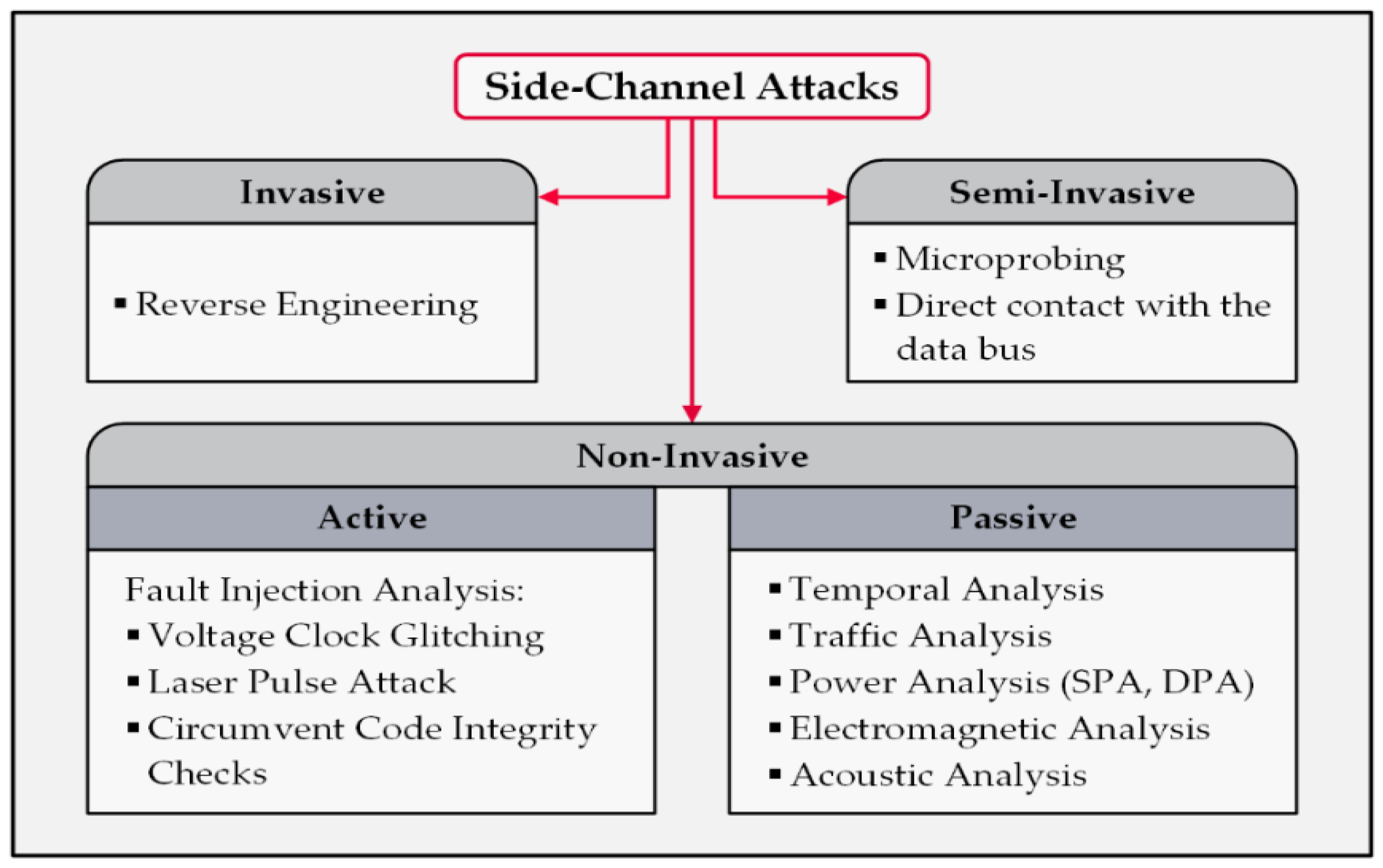
Smart Home Privacy Protection Methods Against A Passive Wireless Based on this vulnerability, we propose the pmu spill attack, a new kind of side channel attack that enables attackers to maliciously leak secret data in transient executions. During the delay, if transient microarchitectural state (e.g. cache) has been created for unauthorized value, it can be leaked using existing side channel attacks. In section ii, we introduce the background knowledge of side channel attacks and transient execution attacks. in section iii, we present the details of the attack. Noise is just someone else’s data. fill buffers may retain stale data from prior memory requests until a new memory request overwrites the fill buffer. under certain conditions, the fill buffer may speculatively forward data, including stale data, to a load operation that will cause a fault assist. io instructions, syscall, . . .
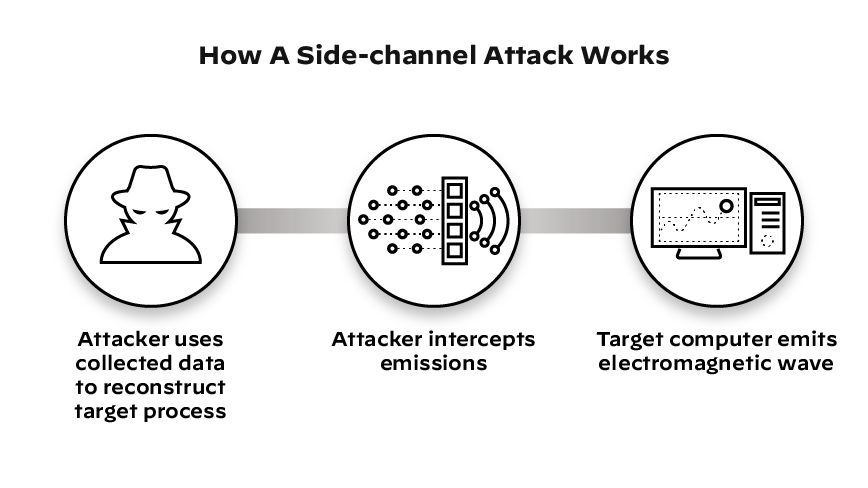
What Is 5g Security Palo Alto Networks In section ii, we introduce the background knowledge of side channel attacks and transient execution attacks. in section iii, we present the details of the attack. Noise is just someone else’s data. fill buffers may retain stale data from prior memory requests until a new memory request overwrites the fill buffer. under certain conditions, the fill buffer may speculatively forward data, including stale data, to a load operation that will cause a fault assist. io instructions, syscall, . . .

Online Course Side Channel Security Transient Execution And Fault
Comments are closed.