Side Channel Attack In Cyber Security

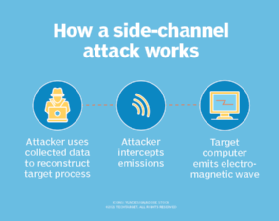
A Tutorial On Physical Security And Side Channel Attacks Pdf A side channel attack is a cybersecurity exploit that aims to gather information from or influence a system's program execution. it does this by measuring or exploiting indirect effects of the system or its hardware rather than directly targeting the program or its code. In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information.

What Is A Side Channel Attack In Cybersecurity Bestcybersecuritynews Uncover the hidden world of side channel attacks: learn how hackers exploit system vulnerabilities, real world examples, and cutting edge defense strategies. Side channel attacks don't target cryptographic systems, but their implementations instead. find out how they can compromise secure algorithms. you can have the best cryptographic systems in the world in place, but your setup may still be vulnerable to side channel attacks. Discover what side channel attacks are, how they operate, their examples, potential risks, and effective protection strategies in this comprehensive guide. In this article, we will delve deeply into what side channel attacks are, the methods hackers use to exploit them, their implications in real world scenarios, and the advanced strategies required to mitigate their risks.

Side Channel Attack Junior Cybersecurity Olympiad Discover what side channel attacks are, how they operate, their examples, potential risks, and effective protection strategies in this comprehensive guide. In this article, we will delve deeply into what side channel attacks are, the methods hackers use to exploit them, their implications in real world scenarios, and the advanced strategies required to mitigate their risks. Explore side channel attacks, including power and timing analysis, how they exploit cryptographic systems, and effective countermeasures to secure hardware implementations. Side channel attacks exploit timing, power consumption, and electromagnetic leakage to extract cryptographic keys and sensitive data. covers attack types, dpa, profiling methods, tools, and mitigation strategies. Explore how side channel attacks secretly exploit hardware signals to steal data and key cybersecurity defenses explained. A side channel attack is a type of cyberattack that involves exploiting various side channels to gain unauthorized access to sensitive information. in computing and cryptography, side channels refer to unintended channels of communication that leak information about the system’s internal state.

Side Channel Attack How Steal Encryption Keys By Touching Pcs Explore side channel attacks, including power and timing analysis, how they exploit cryptographic systems, and effective countermeasures to secure hardware implementations. Side channel attacks exploit timing, power consumption, and electromagnetic leakage to extract cryptographic keys and sensitive data. covers attack types, dpa, profiling methods, tools, and mitigation strategies. Explore how side channel attacks secretly exploit hardware signals to steal data and key cybersecurity defenses explained. A side channel attack is a type of cyberattack that involves exploiting various side channels to gain unauthorized access to sensitive information. in computing and cryptography, side channels refer to unintended channels of communication that leak information about the system’s internal state.

Understanding Side Channel Attacks Power Timing Analysis Cyber Snowden Explore how side channel attacks secretly exploit hardware signals to steal data and key cybersecurity defenses explained. A side channel attack is a type of cyberattack that involves exploiting various side channels to gain unauthorized access to sensitive information. in computing and cryptography, side channels refer to unintended channels of communication that leak information about the system’s internal state.
What Is A Side Channel Attack
Comments are closed.