Shelby Malware Is Stealing Data Abusing Github
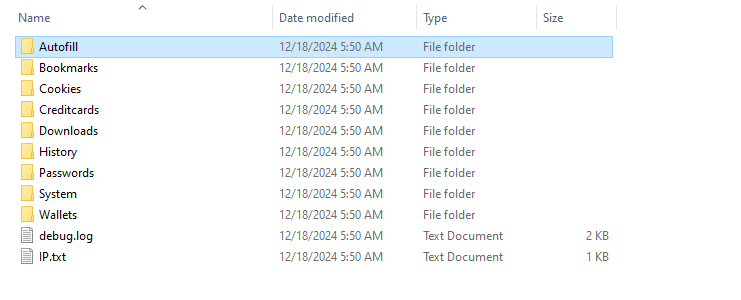
Kaspersky Exposes Hidden Malware On Github Stealing Personal Data And What makes shelby particularly notable is its abuse of github’s infrastructure for command and control (c2) operations. the malware creates and accesses private repositories on github where its operators store commands in encoded base64 strings within seemingly innocuous text files. In recent months, cybersecurity experts have observed the emergence of a sophisticated malware strain named “shelby.” designed specifically to steal sensitive data, shelby malware poses a serious threat to financial institutions and healthcare organizations across north america and europe.
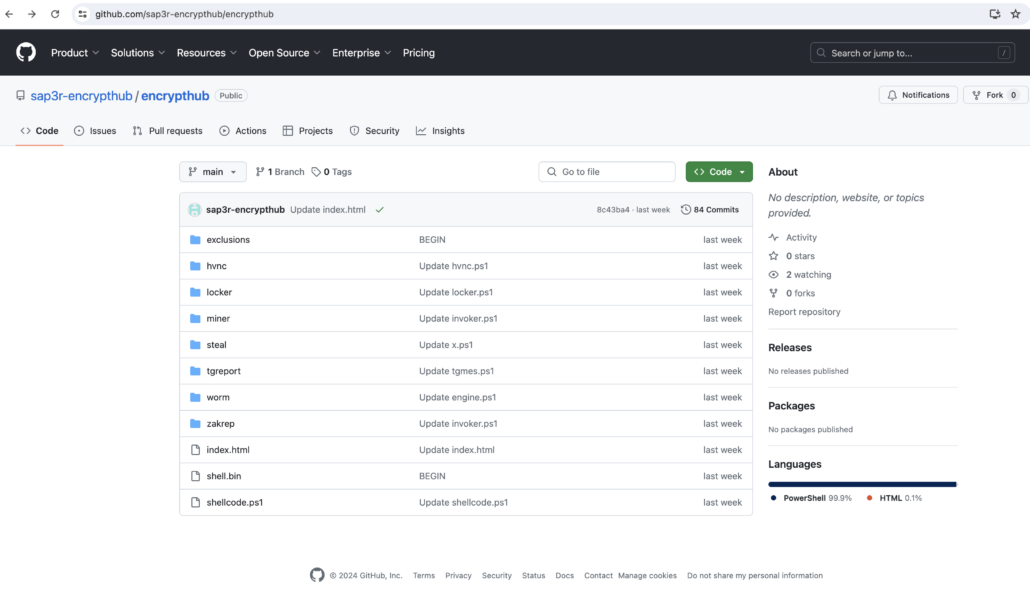
Beware Of Fake Winrar Websites Malware Hosted On Github Elastic security labs has uncovered a sophisticated malware family dubbed shelby that leverages github repositories for command and control (c2) operations. the malware, consisting of two components shelbyloader and shelbyc2 was discovered during an investigation into the ref8685 intrusion campaign targeting organizations in iraq and the united. The github accounts (arthurshellby and johnshelllby) used for the ref8685 malware were malicious and have been shut down by github. of note, arthur and john shelby are characters in the british crime drama television series peaky blinders. One of the most alarming aspects of shelby is its use of github’s infrastructure for command and control (c2) operations. the malware accesses private github repositories where encoded. Elastic security labs has uncovered a sophisticated malware family—dubbed shelby—that combines github based c2 infrastructure, anti analysis techniques, and stealthy persistence to compromise enterprise systems.

Github Users Targeted With Dangerous Malware Attacks Here S What We One of the most alarming aspects of shelby is its use of github’s infrastructure for command and control (c2) operations. the malware accesses private github repositories where encoded. Elastic security labs has uncovered a sophisticated malware family—dubbed shelby—that combines github based c2 infrastructure, anti analysis techniques, and stealthy persistence to compromise enterprise systems. Elastic security labs has uncovered a sophisticated malware campaign targeting iraq’s telecommunications sector, utilizing a new malware family called shelby that abuses github for command and control (c2) operations. Elastic security labs has uncovered a sophisticated malware family—dubbed shelby—that combines github based c2 infrastructure, anti analysis techniques, and stealthy. A new breed of malware exploiting github for command and control cybersecurity researchers at elastic security labs have uncovered a sophisticated malware strain named shelby, which leverages github repositories for its command and control (c2) operations. Elastic security labs has uncovered a sophisticated malware campaign, dubbed ref8685, targeting the iraqi telecommunications sector. the campaign utilizes a novel malware family called shelby, which abuses github for command and control (c2) operations, data exfiltration, and command retrieval.
How Threat Actors Can Use Github Repositories To Deploy Malware Elastic security labs has uncovered a sophisticated malware campaign targeting iraq’s telecommunications sector, utilizing a new malware family called shelby that abuses github for command and control (c2) operations. Elastic security labs has uncovered a sophisticated malware family—dubbed shelby—that combines github based c2 infrastructure, anti analysis techniques, and stealthy. A new breed of malware exploiting github for command and control cybersecurity researchers at elastic security labs have uncovered a sophisticated malware strain named shelby, which leverages github repositories for its command and control (c2) operations. Elastic security labs has uncovered a sophisticated malware campaign, dubbed ref8685, targeting the iraqi telecommunications sector. the campaign utilizes a novel malware family called shelby, which abuses github for command and control (c2) operations, data exfiltration, and command retrieval.

Mods On Github Come With Infostealers Cybernews A new breed of malware exploiting github for command and control cybersecurity researchers at elastic security labs have uncovered a sophisticated malware strain named shelby, which leverages github repositories for its command and control (c2) operations. Elastic security labs has uncovered a sophisticated malware campaign, dubbed ref8685, targeting the iraqi telecommunications sector. the campaign utilizes a novel malware family called shelby, which abuses github for command and control (c2) operations, data exfiltration, and command retrieval.
Comments are closed.