Shadow Saas Assessment
Shadow Saas Assessment Gain a complete view of saas usage across your enterprise, including shadow saas you don't see and rogue cloud accounts that leave your organization vulnerable. We walk you through the discovery, assessment, and governance strategies that enterprise buyers are using to reclaim control of shadow saas while transforming it into legitimate, negotiated volume.

Eliminate The Risk Of Shadow Saas Identify and control unapproved saas apps and ai tools before they expose sensitive data or create compliance gaps across your organization. Learn what shadow saas is, the risks it brings, and how organizations can identify and secure unmanaged saas apps effectively. Use this shadow it assessment checklist to uncover hidden saas apps, reduce security risk, improve compliance, and regain it visibility. Uncover your full saas landscape. automatically discover shadow saas, cloud accounts, and oauth access to reduce identity risk and maintain continuous, audit ready governance. detect and govern unauthorized saas accounts and identities with the world's best grc cybersecurity software.
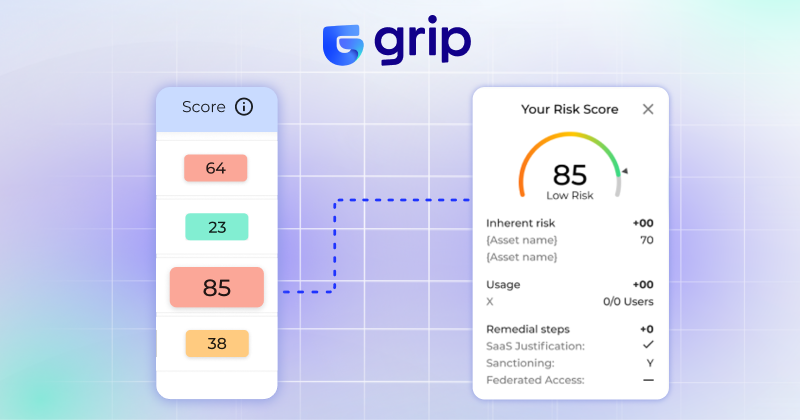
Shadow Saas Management Suridata Use this shadow it assessment checklist to uncover hidden saas apps, reduce security risk, improve compliance, and regain it visibility. Uncover your full saas landscape. automatically discover shadow saas, cloud accounts, and oauth access to reduce identity risk and maintain continuous, audit ready governance. detect and govern unauthorized saas accounts and identities with the world's best grc cybersecurity software. Explore how shadow saas bypasses traditional vendor oversight, and how organizations can detect and govern this growing risk. By conducting a comprehensive discovery process, organizations can identify all saas applications in use—including shadow saas that may have been purchased or set up without it oversight. Saas discovery is the process of identifying and cataloging all cloud based software applications used within an organization. this includes apps that are procured and sanctioned by it as well as “shadow saas”—the long tail of apps that your employees experiment with and adopt without going through a formal it process. This article outlines a step by step playbook to assess shadow saas at your organization and guides you on how to move towards a user centric risk management strategy.
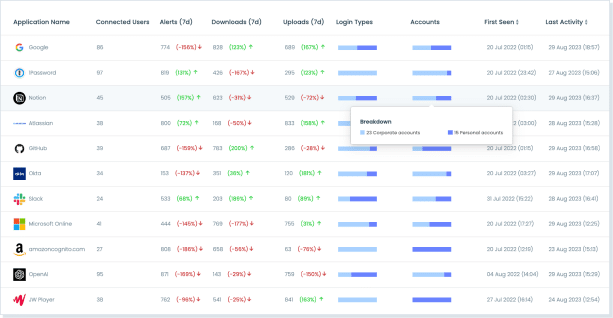
Shadow Saas Saas Security Layerx Explore how shadow saas bypasses traditional vendor oversight, and how organizations can detect and govern this growing risk. By conducting a comprehensive discovery process, organizations can identify all saas applications in use—including shadow saas that may have been purchased or set up without it oversight. Saas discovery is the process of identifying and cataloging all cloud based software applications used within an organization. this includes apps that are procured and sanctioned by it as well as “shadow saas”—the long tail of apps that your employees experiment with and adopt without going through a formal it process. This article outlines a step by step playbook to assess shadow saas at your organization and guides you on how to move towards a user centric risk management strategy.

Saas Pulse Free Risk Assessment Wing Security Saas discovery is the process of identifying and cataloging all cloud based software applications used within an organization. this includes apps that are procured and sanctioned by it as well as “shadow saas”—the long tail of apps that your employees experiment with and adopt without going through a formal it process. This article outlines a step by step playbook to assess shadow saas at your organization and guides you on how to move towards a user centric risk management strategy.
Comments are closed.