Settings Knowledge Base Article Threatconnect
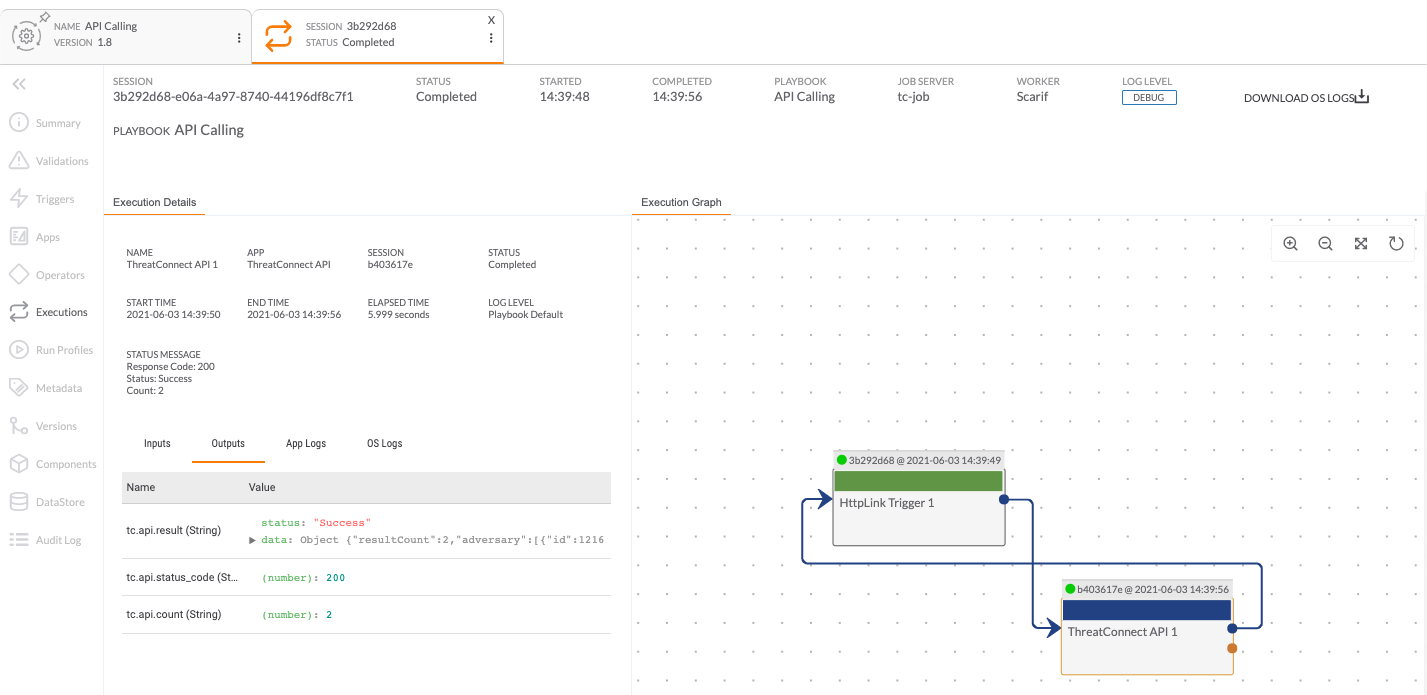
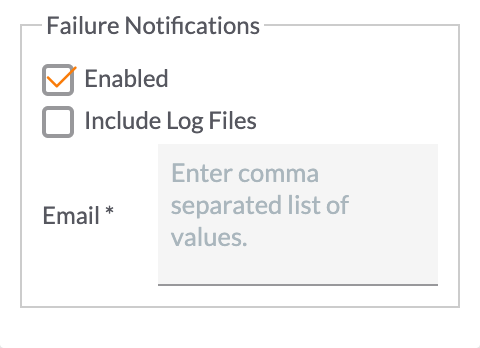
Settings Knowledge Base Article Threatconnect This article describes the options available via the settings menu in the upper right corner of the playbook designer. With more than 100 transforms to query and pivot through threatconnect’s data, investigators can easily model threat and the relationships between malware, domains, ips, and other indicators to the incidents they were observed in, threats they are associated to, or adversary personas.
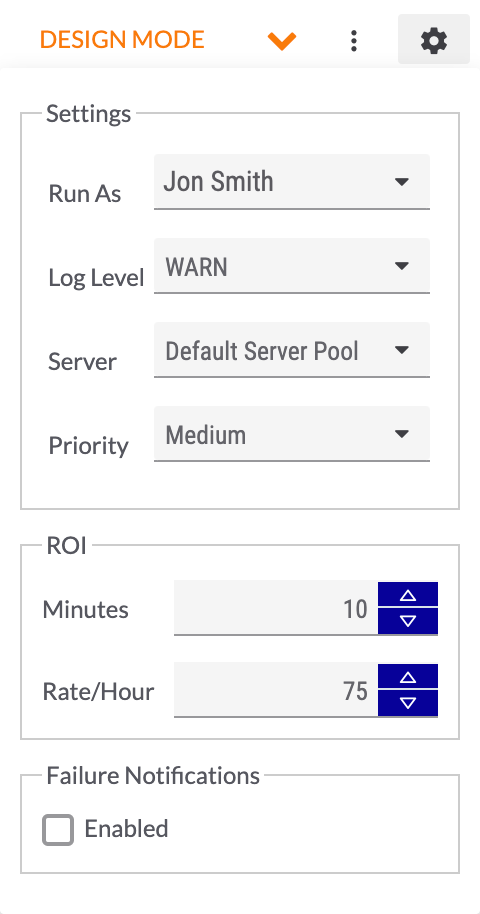
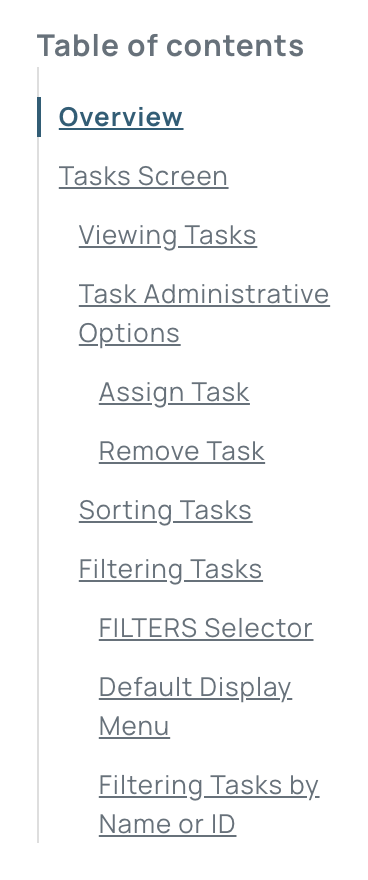
Settings Knowledge Base Article Threatconnect Browse our collection of step by step instructions for using threatconnect and guides for configuring its integrations. This article explains the functionalities available on all of the tabs of the my profile screen in threatconnect. This article highlights key features in the threatconnect knowledge base and provides helpful tips for finding and viewing knowledge base articles. This article provides definitions of important and commonly used terms in threatconnect.
Settings Knowledge Base Article Threatconnect This article highlights key features in the threatconnect knowledge base and provides helpful tips for finding and viewing knowledge base articles. This article provides definitions of important and commonly used terms in threatconnect. © 2012–2024 threatconnect, inc. all rights reserved. Any time a new feature is introduced, we add an article to the knowledge base explaining how to set up or use the new feature. and, we’ve recently added a button in the platform that gives you instant access to the knowledge base from anywhere in the platform. Find something missing or unclear in the documentation? feel free to raise an issue in the threatconnect developer documentation repository. can’t find ‘ main ’ module in ‘.’. Case management and the workflow feature in threatconnect enables analysts and their teams to define and operationalize consistent, standardized processes for managing threat intelligence and performing security operations.

Threatconnect Knowledge Base © 2012–2024 threatconnect, inc. all rights reserved. Any time a new feature is introduced, we add an article to the knowledge base explaining how to set up or use the new feature. and, we’ve recently added a button in the platform that gives you instant access to the knowledge base from anywhere in the platform. Find something missing or unclear in the documentation? feel free to raise an issue in the threatconnect developer documentation repository. can’t find ‘ main ’ module in ‘.’. Case management and the workflow feature in threatconnect enables analysts and their teams to define and operationalize consistent, standardized processes for managing threat intelligence and performing security operations.
Threatconnect Knowledge Base Find something missing or unclear in the documentation? feel free to raise an issue in the threatconnect developer documentation repository. can’t find ‘ main ’ module in ‘.’. Case management and the workflow feature in threatconnect enables analysts and their teams to define and operationalize consistent, standardized processes for managing threat intelligence and performing security operations.
Getting Started With The Threatconnect Knowledge Base
Comments are closed.