Setting Up Your Api Hacking Home Lab Cybershaykh

Create Hacking Lab Pdf In this article, i’m going to be showing you how you can set up your api (application programming interface) hacking home lab to practice api hacking and uncovering vulnerabilities in api applications. Introduction in this article, i’m going to be showing you how you can set up your api (application programming interface) hacking home lab to practice api hacking and uncovering vulnerabilities.
Setting Up Your Api Hacking Home Lab Cybershaykh A blog dedicated to writing about cybersecurity, delving into topics like ethical hacking, security research and aplication security. One of the best ways to gain practical skills is by setting up a home lab. this controlled environment allows you to practice ethical hacking, network defense, and more, all without the risk of causing harm to real world systems. A blog dedicated to writing about cybersecurity, delving into topics like ethical hacking, security research and aplication security. Having a lab setup handy can help you a lot in your learning. a lab lets you practice your skills in a controlled environment, reducing the risks that arise from practicing on real systems.
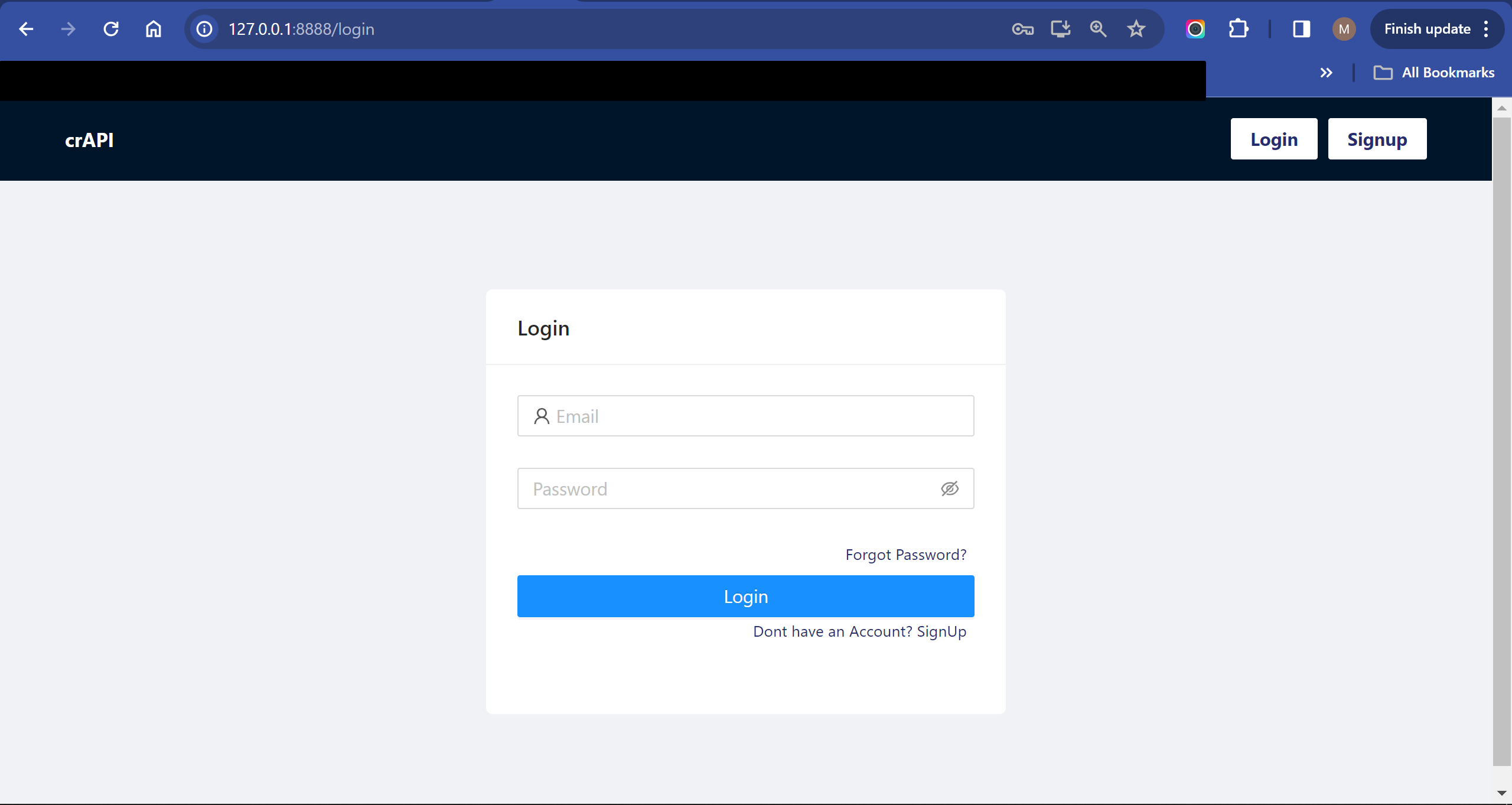
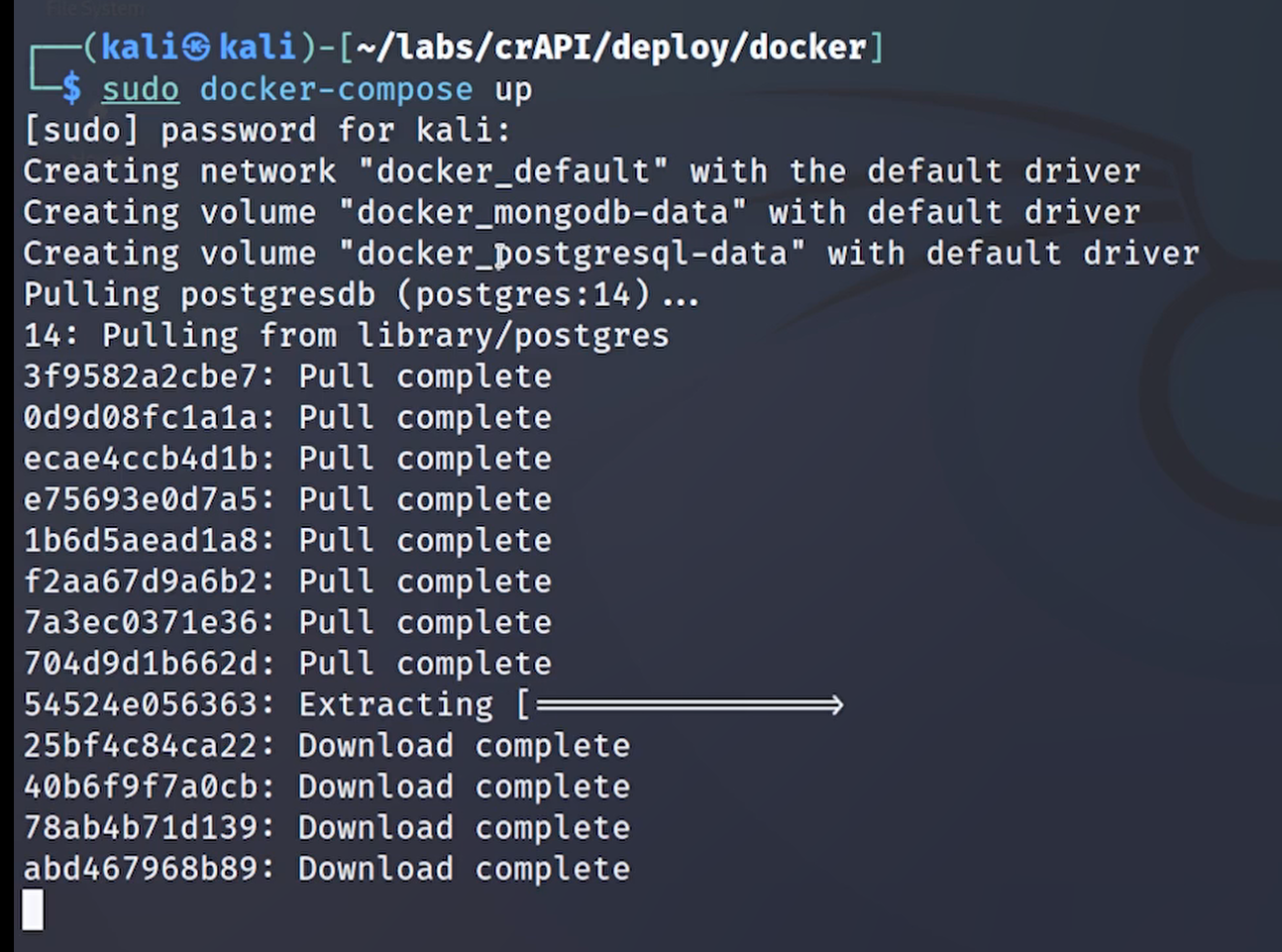
Setting Up Your Api Hacking Home Lab Cybershaykh A blog dedicated to writing about cybersecurity, delving into topics like ethical hacking, security research and aplication security. Having a lab setup handy can help you a lot in your learning. a lab lets you practice your skills in a controlled environment, reducing the risks that arise from practicing on real systems. In this guide, we will walk you through the essential components, setups, and best practices to create an efficient home lab tailored for hacking and pentesting. Creating a personal hacking lab is essential for anyone serious about learning ethical hacking and penetration testing. this guide will walk you through the process of setting up a comprehensive hacking lab using the latest technologies and tools available in 2024 2025. An all in one automation project to help students of apisec university's api penetration testing course quickly set up a ready to use lab environment on kali linux. In this guide, we will walk you through the technical aspects of setting up a home cybersecurity lab, including hardware requirements, software tools, network configurations, and practical use cases.
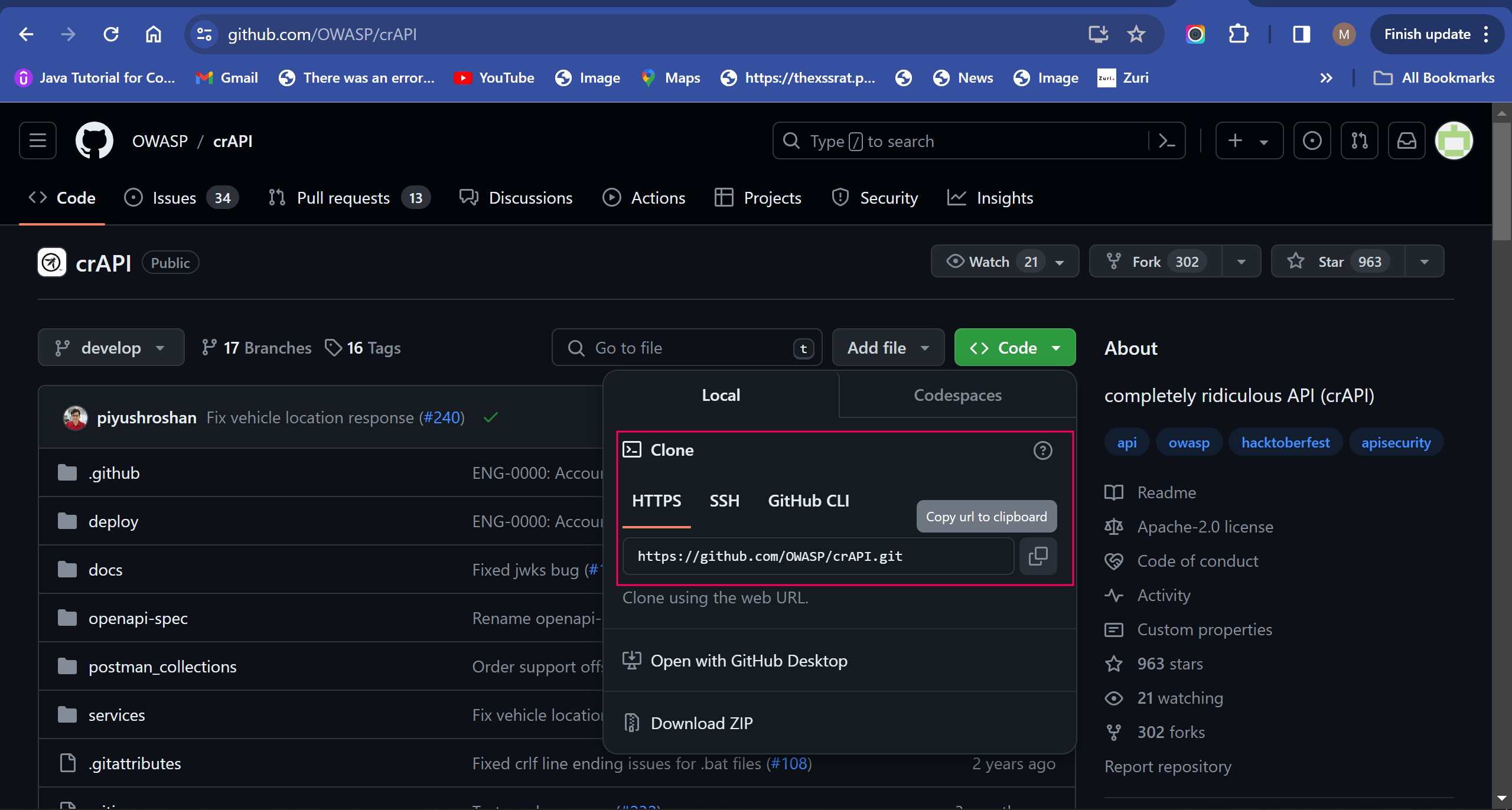
Setting Up Your Api Hacking Home Lab Cybershaykh In this guide, we will walk you through the essential components, setups, and best practices to create an efficient home lab tailored for hacking and pentesting. Creating a personal hacking lab is essential for anyone serious about learning ethical hacking and penetration testing. this guide will walk you through the process of setting up a comprehensive hacking lab using the latest technologies and tools available in 2024 2025. An all in one automation project to help students of apisec university's api penetration testing course quickly set up a ready to use lab environment on kali linux. In this guide, we will walk you through the technical aspects of setting up a home cybersecurity lab, including hardware requirements, software tools, network configurations, and practical use cases.
Setting Up Your Api Hacking Home Lab Cybershaykh An all in one automation project to help students of apisec university's api penetration testing course quickly set up a ready to use lab environment on kali linux. In this guide, we will walk you through the technical aspects of setting up a home cybersecurity lab, including hardware requirements, software tools, network configurations, and practical use cases.
Comments are closed.