Session Vs Token Based Authentication
Comparing Token Based Authentication And Session Based Authentication The session and token based authentication methods are used to make a server trust any request sent by an authenticated user over the internet. in this way, a user can interact with their account without continually specifying their credentials. these methods are usually used for different purposes. Two common approaches dominate this space: token based authentication and session based authentication. while both verify user identity, they differ significantly in how they operate,.
Comparing Token Based Authentication And Session Based Authentication Session vs token authentication: which should you choose? understand session based vs token based authentication, cookies vs jwt, pros cons, csrf xss trade offs, and when to use each—plus examples. I would need a very compelling reason as to why session storage is unwanted before recommending using cryptographic tokens. always remember the no.1 rule of cryptographic security: never design your own single use cryptographic measures. 👉 “how do we know this request is coming from the right user?” two of the most common solutions are: sessions (stateful authentication) tokens (stateless authentication) understanding both deeply will help you design secure, scalable backend architectures. Session based authentication has been around since the early days of the web. it is battle tested and works well for traditional server rendered applications. token based authentication emerged later, driven by the rise of single page applications, mobile apps, and microservices.
Token Based Authentication Vs Session Based Authentication 👉 “how do we know this request is coming from the right user?” two of the most common solutions are: sessions (stateful authentication) tokens (stateless authentication) understanding both deeply will help you design secure, scalable backend architectures. Session based authentication has been around since the early days of the web. it is battle tested and works well for traditional server rendered applications. token based authentication emerged later, driven by the rise of single page applications, mobile apps, and microservices. Understanding the difference between session vs token authentication is vital for creating secure and efficient applications. session based methods suit traditional web apps, while token based authentication provides scalability, flexibility, and cross domain support for modern systems. In general, token based authentication is more typical, especially using frameworks such as oauth2 or openid connect. this means that third party clients will find it easier to interact with us, as they can use tooling that already understands these concepts. Detailed comparison of session based and token based authentication for enterprise sso. learn about scalability, security, and ciam best practices. I’m going to show you how sessions and tokens actually work on the wire, what they’re each good at, the failure modes i see most often, and the patterns i recommend for modern web apps and apis.
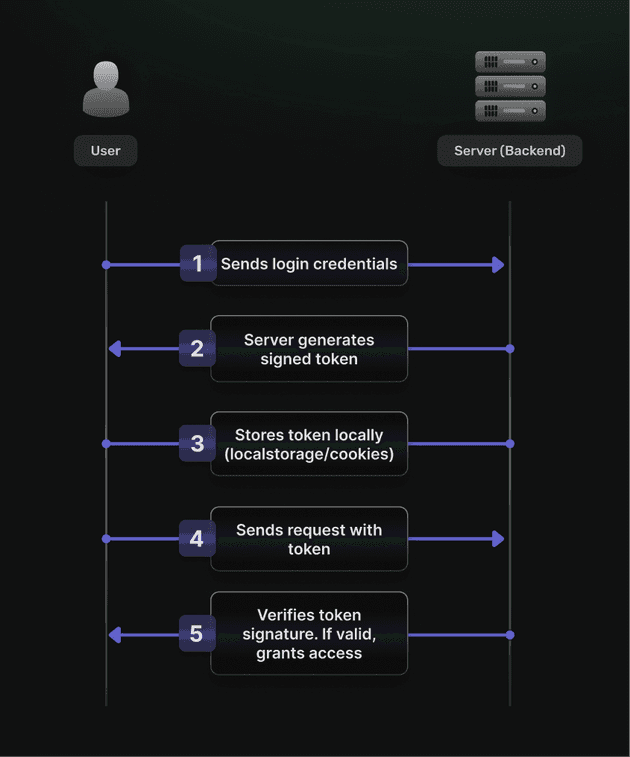
Token Based Authentication Vs Session Based Authentication Understanding the difference between session vs token authentication is vital for creating secure and efficient applications. session based methods suit traditional web apps, while token based authentication provides scalability, flexibility, and cross domain support for modern systems. In general, token based authentication is more typical, especially using frameworks such as oauth2 or openid connect. this means that third party clients will find it easier to interact with us, as they can use tooling that already understands these concepts. Detailed comparison of session based and token based authentication for enterprise sso. learn about scalability, security, and ciam best practices. I’m going to show you how sessions and tokens actually work on the wire, what they’re each good at, the failure modes i see most often, and the patterns i recommend for modern web apps and apis.
Comments are closed.