Session Hijacking Explained In Less Than 90 Seconds Sessionhijacking Cybersecurity Ethicalhacking
Session Hijacking Explained All About Testing The most common method of session hijacking is called ip spoofing, when an attacker uses source routed ip packets to insert commands into an active communication between two nodes on a network and disguise itself as one of the authenticated users. This cybersecurity threat is more dangerous than you thinkyour phone is now required to spy on you.

Session Hijacking Explained Shieldrize Your Cybersecurity Partner What is session hijacking and how does it work? learn what session hijacking is, how it works, and the best defenses against it. discover real world examples, prevention strategies, and essential security tips to protect user sessions. Session hijacking is a type of cyber attack where a malicious actor takes over an existing user session to gain unauthorized access to a targeted system or network. the attacker exploits vulnerabilities in network protocols and web applications to hijack sessions and impersonate legitimate users. Session hijacking is a cyberattack where attackers steal session tokens to bypass mfa and impersonate users. learn how it works and how to prevent it. Session hijacking is a cyberattack where a threat actor steals a valid "session token" (a digital temporary key) to take over a user's web session. this allows the attacker to impersonate the user without needing their password or mfa code.
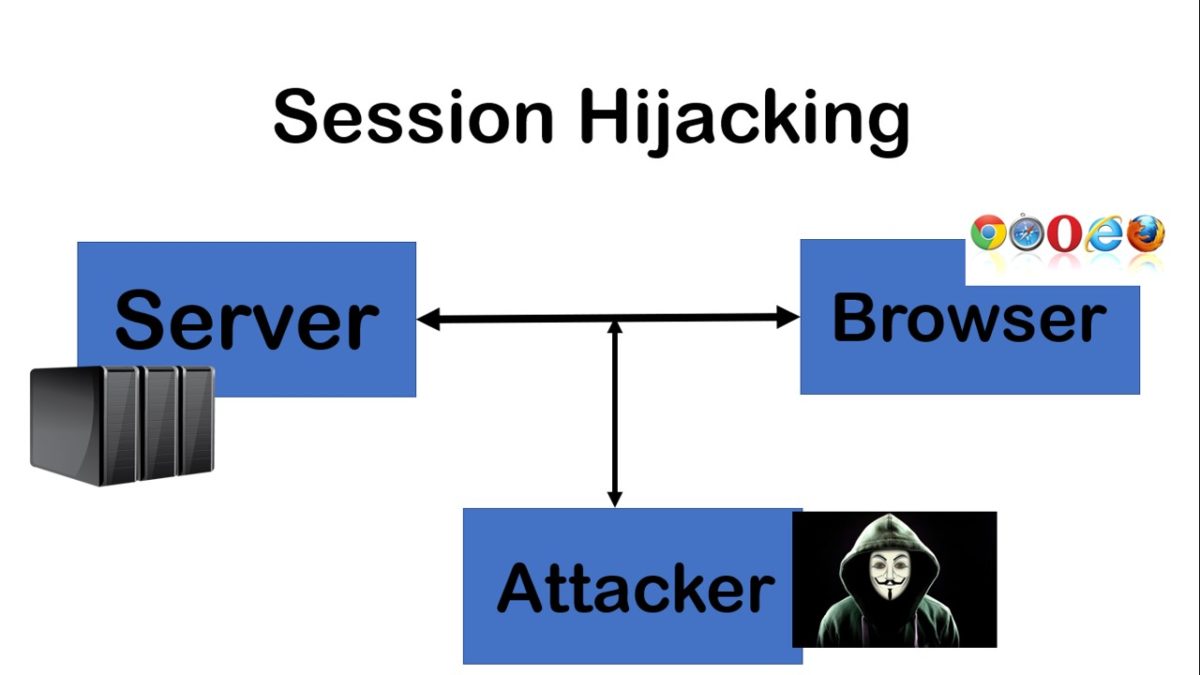
Session Hijacking Explained All About Testing Session hijacking is a cyberattack where attackers steal session tokens to bypass mfa and impersonate users. learn how it works and how to prevent it. Session hijacking is a cyberattack where a threat actor steals a valid "session token" (a digital temporary key) to take over a user's web session. this allows the attacker to impersonate the user without needing their password or mfa code. Session hijacking is a cyberattack where a hacker takes control of a user’s active session by stealing or guessing their session id. once they have the valid id, they can impersonate the user and access sensitive data or perform actions on their behalf. In the first installment of our technical blog series on session security, i’ll explain the implications of session hijacking, how to detect it, and why identifying potential session hijacking threats is critical to protecting your saas users. Session hijacking refers to the malicious act of taking control of a user’s web session. a session, in the context of web browsing, is a series of interactions between two communication endpoints, sharing a unique session token to ensure continuity and security. What is session hijacking and how it works? session hijacking is a security attack where an attacker takes control of a user's active session on a web application or network.
Comments are closed.