Session Hijacking Cookie Zsecurity
Session Hijacking Session hijacking occurs when an attacker intercepts or steals a valid session token to gain unauthorized access to a web application or network service. this can lead to impersonation and data theft. Session hijacking is a cyberattack technique where adversaries take control of a legitimate user's active web session by stealing the session identifier: typically an oauth token, session cookie, or refresh token stored in the browser.
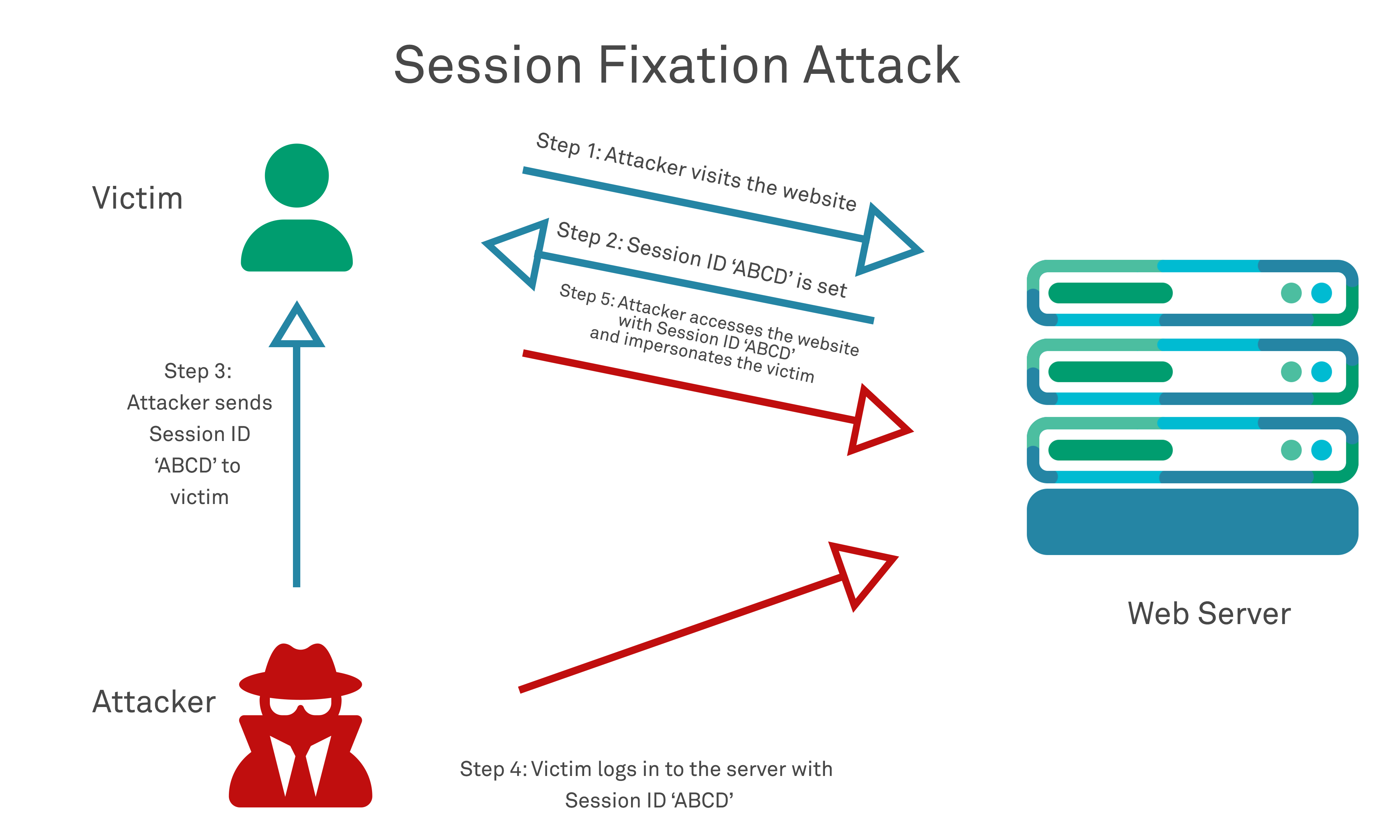
Session Hijacking Learn how session hijacking bypasses mfa through cookie theft. explore real attack scenarios, detection signals, and automated monitoring solutions for enterprise security. Cookie theft uses phishing and malware to steal a client's session token once they have logged into a secured web server. info stealing malware is often designed to scrape browser cookies and export them to attackers, who can then import these cookies into their own browsers to bypass authentication. What is session hijacking? session hijacking is a cyber attack method where adversaries intercept or steal valid session tokens (like cookies or authentication ids) to impersonate legitimate users and gain unauthorized access to systems, applications, or data. Pro security 'stolen session cookies render mfa irrelevant': how $900 per month turnkey malware is putting enterprise grade account hijacking in the hands of rookie hackers news.
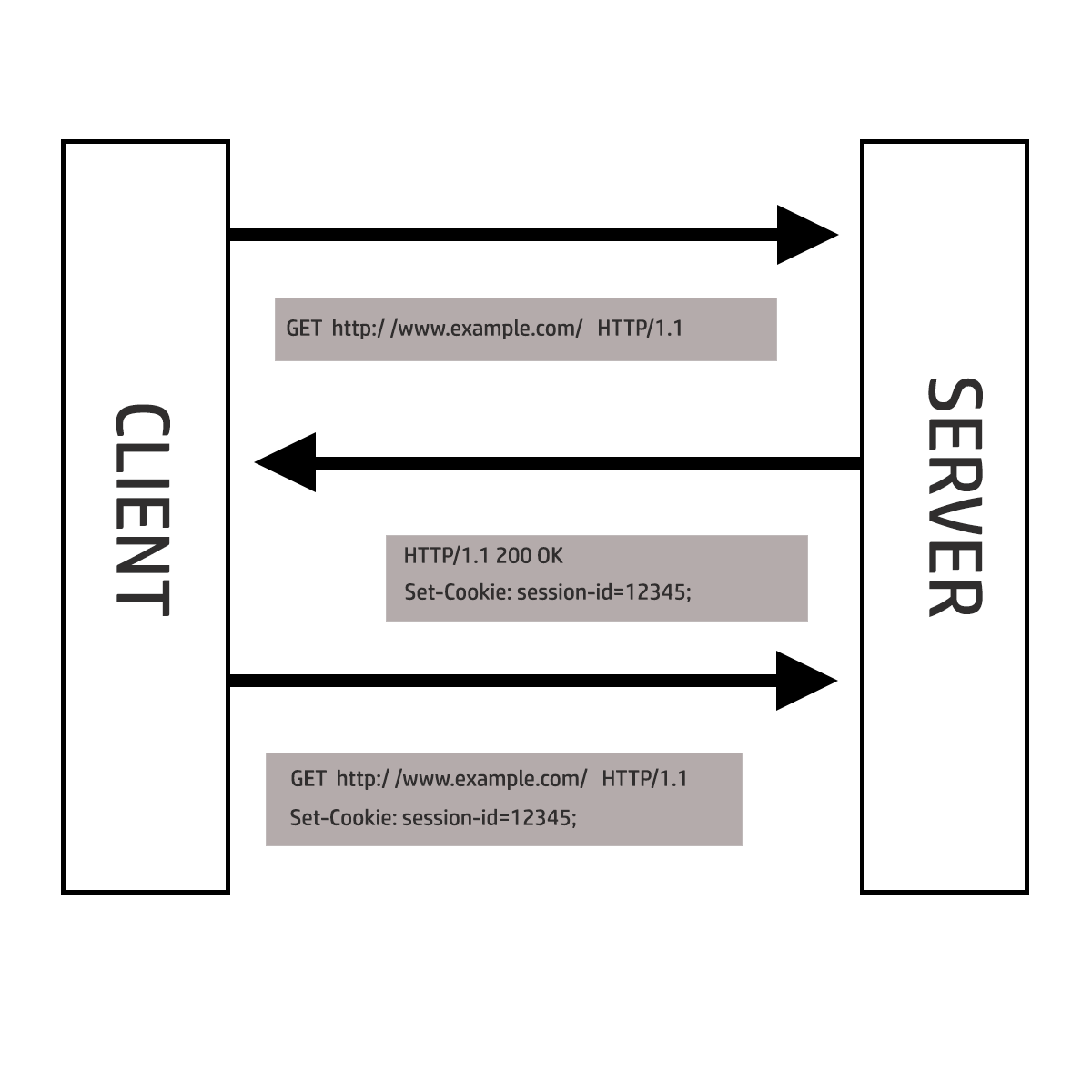
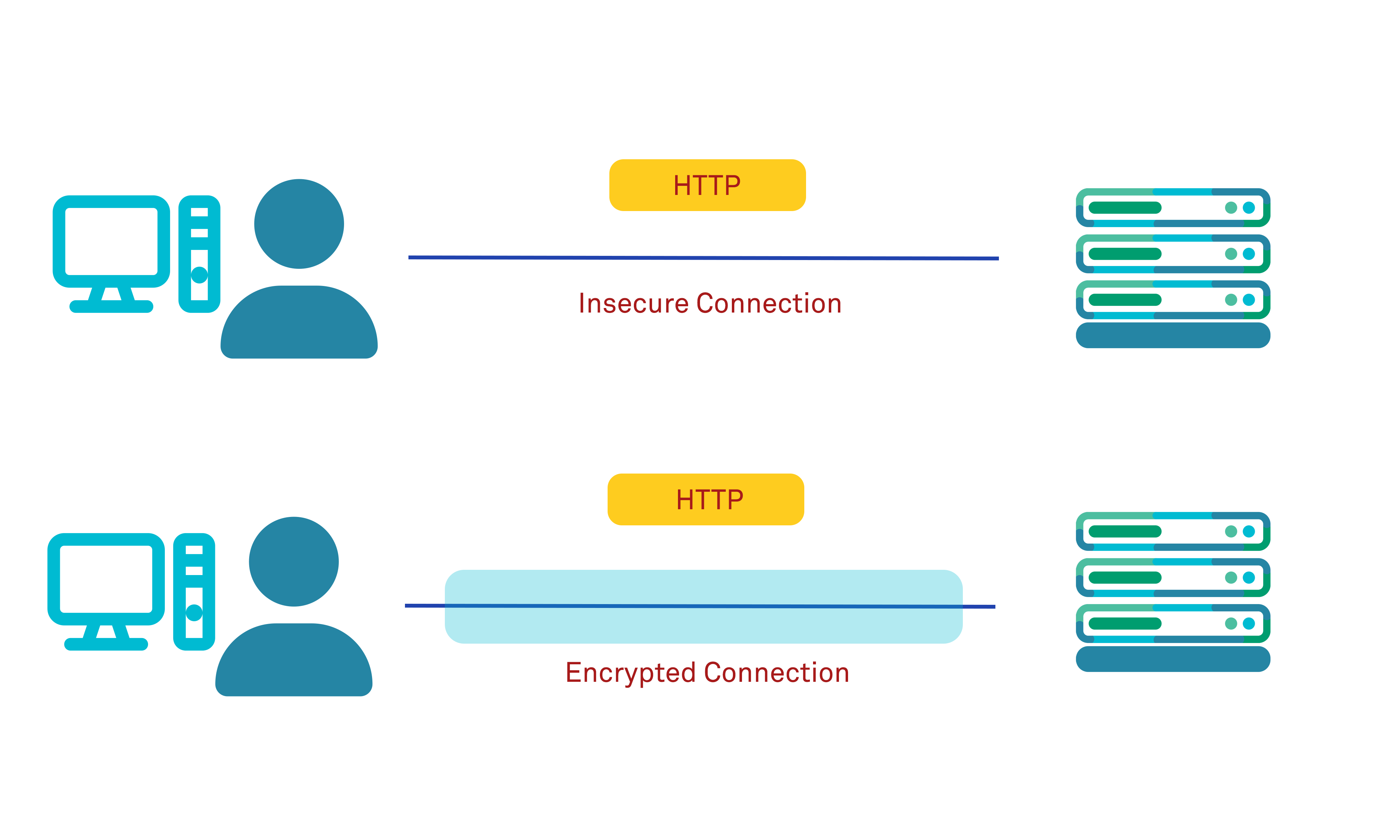
Session Hijacking What is session hijacking? session hijacking is a cyber attack method where adversaries intercept or steal valid session tokens (like cookies or authentication ids) to impersonate legitimate users and gain unauthorized access to systems, applications, or data. Pro security 'stolen session cookies render mfa irrelevant': how $900 per month turnkey malware is putting enterprise grade account hijacking in the hands of rookie hackers news. This design allows large and small websites to upgrade to secure, hardware bound sessions by adding dedicated registration and refresh endpoints to their backends, while maintaining complete compatibility with their existing front end. Learn how session hijacking through cookies works, the risks it poses to user security, and best practices to defend against it. discover how a consent management platform (cmp) can reduce cookie exposure and strengthen web protection. Proactive defense mechanisms such as secure cookies, https encryption, and session id regeneration form the foundation of a secure authentication process. in the next section, we’ll examine real world examples of session hijacking to illustrate the impact of these attacks. Explore how cookie hijacking works, its risks, and effective prevention techniques with our comprehensive guide on session security threats.
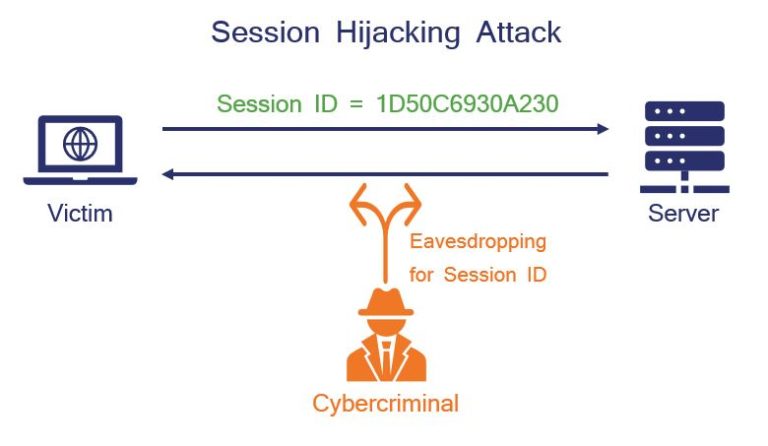
The Ultimate Guide To Session Hijacking Aka Cookie Hijacking Hashed This design allows large and small websites to upgrade to secure, hardware bound sessions by adding dedicated registration and refresh endpoints to their backends, while maintaining complete compatibility with their existing front end. Learn how session hijacking through cookies works, the risks it poses to user security, and best practices to defend against it. discover how a consent management platform (cmp) can reduce cookie exposure and strengthen web protection. Proactive defense mechanisms such as secure cookies, https encryption, and session id regeneration form the foundation of a secure authentication process. in the next section, we’ll examine real world examples of session hijacking to illustrate the impact of these attacks. Explore how cookie hijacking works, its risks, and effective prevention techniques with our comprehensive guide on session security threats.

The Ultimate Guide To Session Hijacking Aka Cookie Hijacking Hashed Proactive defense mechanisms such as secure cookies, https encryption, and session id regeneration form the foundation of a secure authentication process. in the next section, we’ll examine real world examples of session hijacking to illustrate the impact of these attacks. Explore how cookie hijacking works, its risks, and effective prevention techniques with our comprehensive guide on session security threats.
The Ultimate Guide To Session Hijacking Aka Cookie Hijacking Hashed
Comments are closed.