Session Hijacking Attack Complete Tutorial Session Id And Cookie Stealing Side Jacking
Session Hijacking Attack Owasp Foundation In this article, we’ll dive deep into what session hijacking is, how attackers execute it, and most importantly, how developers and users can protect themselves against these attacks. Session hijacking, also known as cookie hijacking, is a vulnerability that allows an attacker to gain unauthorized access to a user's session by stealing or predicting the session identifier (usually stored in a cookie).

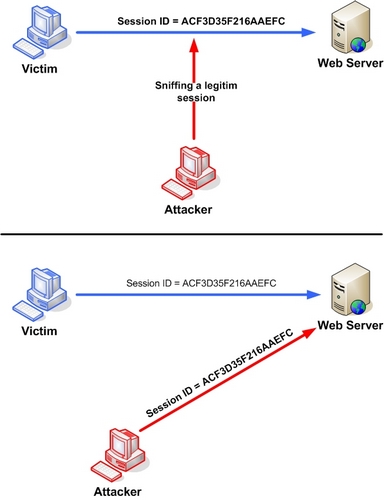
What Is Session Hijacking Examples Prevention Session hijacking is a cyberattack where a malicious actor takes over a user's authorized web session by stealing their session id or token. This article explain what is session hijacking, lists various methods of session hijacking, the ramifications of an attack, and how to prevent it. The attacker can compromise the session token by using malicious code or programs running at the client side. the example shows how the attacker could use an xss attack to steal the session token. Session hijacking attack complete tutorial | session id and cookie stealing | side jacking sniffing into active session: the attacker then finds an active session between the.

The Ultimate Guide To Session Hijacking Aka Cookie Hijacking Hashed The attacker can compromise the session token by using malicious code or programs running at the client side. the example shows how the attacker could use an xss attack to steal the session token. Session hijacking attack complete tutorial | session id and cookie stealing | side jacking sniffing into active session: the attacker then finds an active session between the. Session hijacking typically starts with an attacker identifying and intercepting session tokens, most often transmitted as cookies or url parameters between a client and a server. The fundamental ideas of session hijacking and the methods a hacker can use to carry out this activity have been explored in this article. we've talked about how hackers and attackers gain illegal access, including their strategies for creating vulnerabilities. The document outlines a lab setup for performing a cookie based session hijacking attack using two virtual machines: an attacker vm running kali linux and a victim vm with dvwa. Session hijacking occurs when an attacker takes control of a user’s online activity by stealing or guessing the information that allows a website to recognize them as logged in. this attack exploits the system websites use to identify and verify active user sessions.
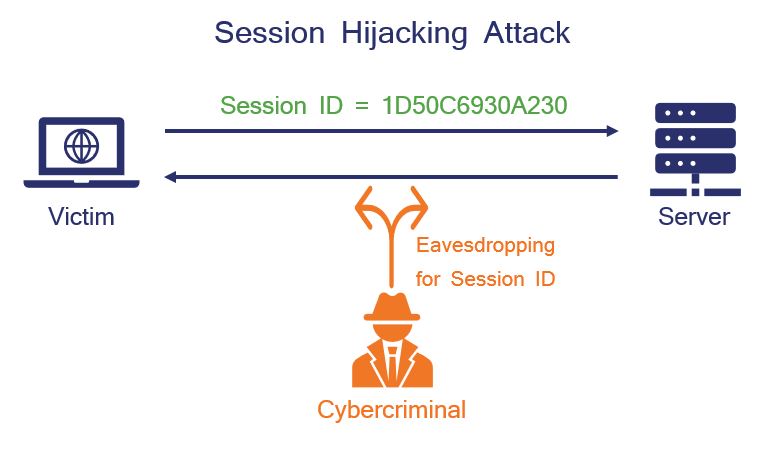
The Ultimate Guide To Session Hijacking Aka Cookie Hijacking Hashed Session hijacking typically starts with an attacker identifying and intercepting session tokens, most often transmitted as cookies or url parameters between a client and a server. The fundamental ideas of session hijacking and the methods a hacker can use to carry out this activity have been explored in this article. we've talked about how hackers and attackers gain illegal access, including their strategies for creating vulnerabilities. The document outlines a lab setup for performing a cookie based session hijacking attack using two virtual machines: an attacker vm running kali linux and a victim vm with dvwa. Session hijacking occurs when an attacker takes control of a user’s online activity by stealing or guessing the information that allows a website to recognize them as logged in. this attack exploits the system websites use to identify and verify active user sessions.
Comments are closed.