Session Blocking Wallarm Documentation
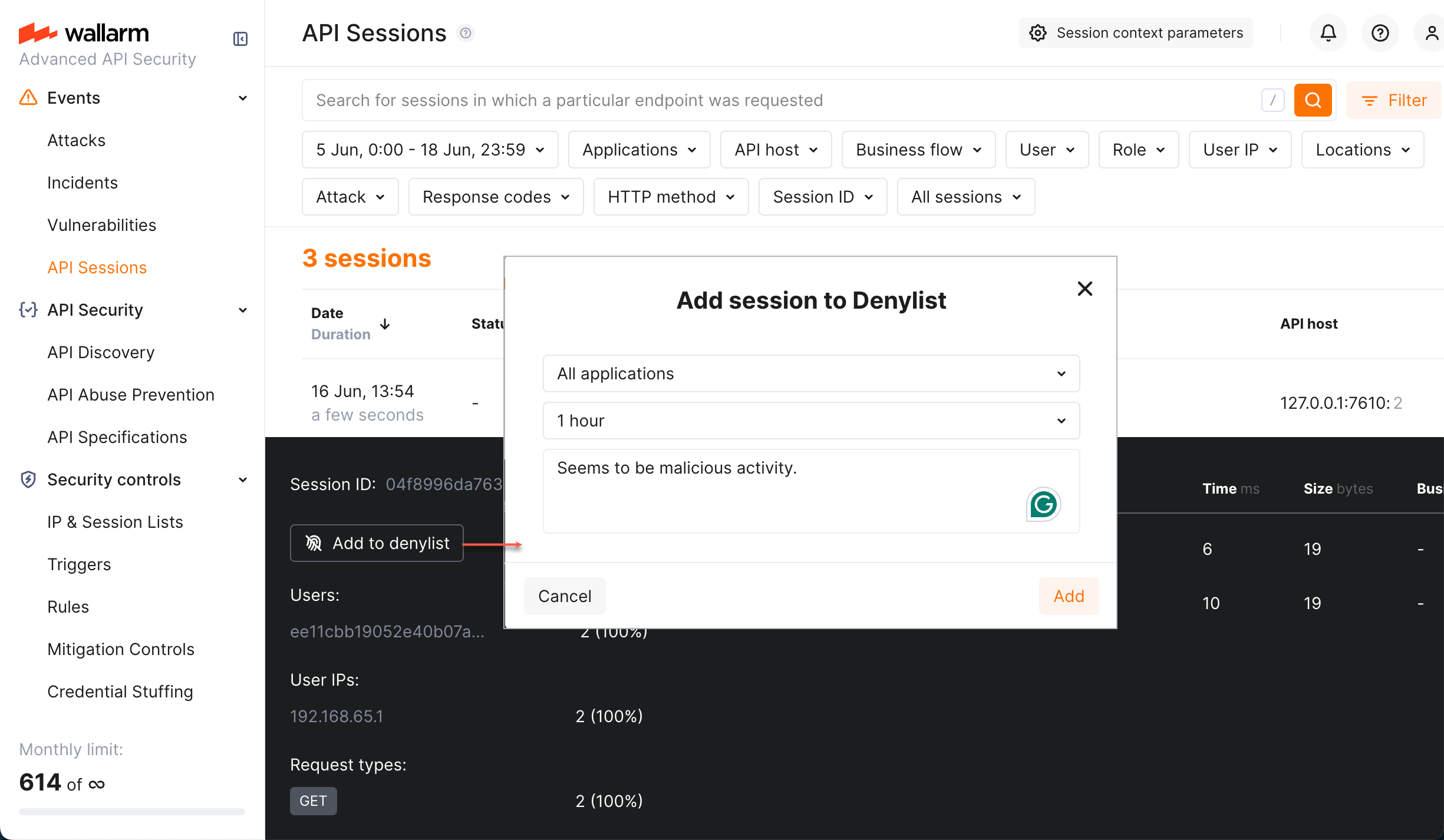
Blocking Wallarm Documentation For session blocking to be an effective measure against different types of threats, how requests are grouped into sessions should be properly configured. we recommend using fingerprints for unauthenticated sessions and a user identifier (like user id, token, etc.) for authenticated ones. Session blocking allows for more intelligent security decisions based on the state of the current interaction with the application, rather than just its network origins (source ip addresses).
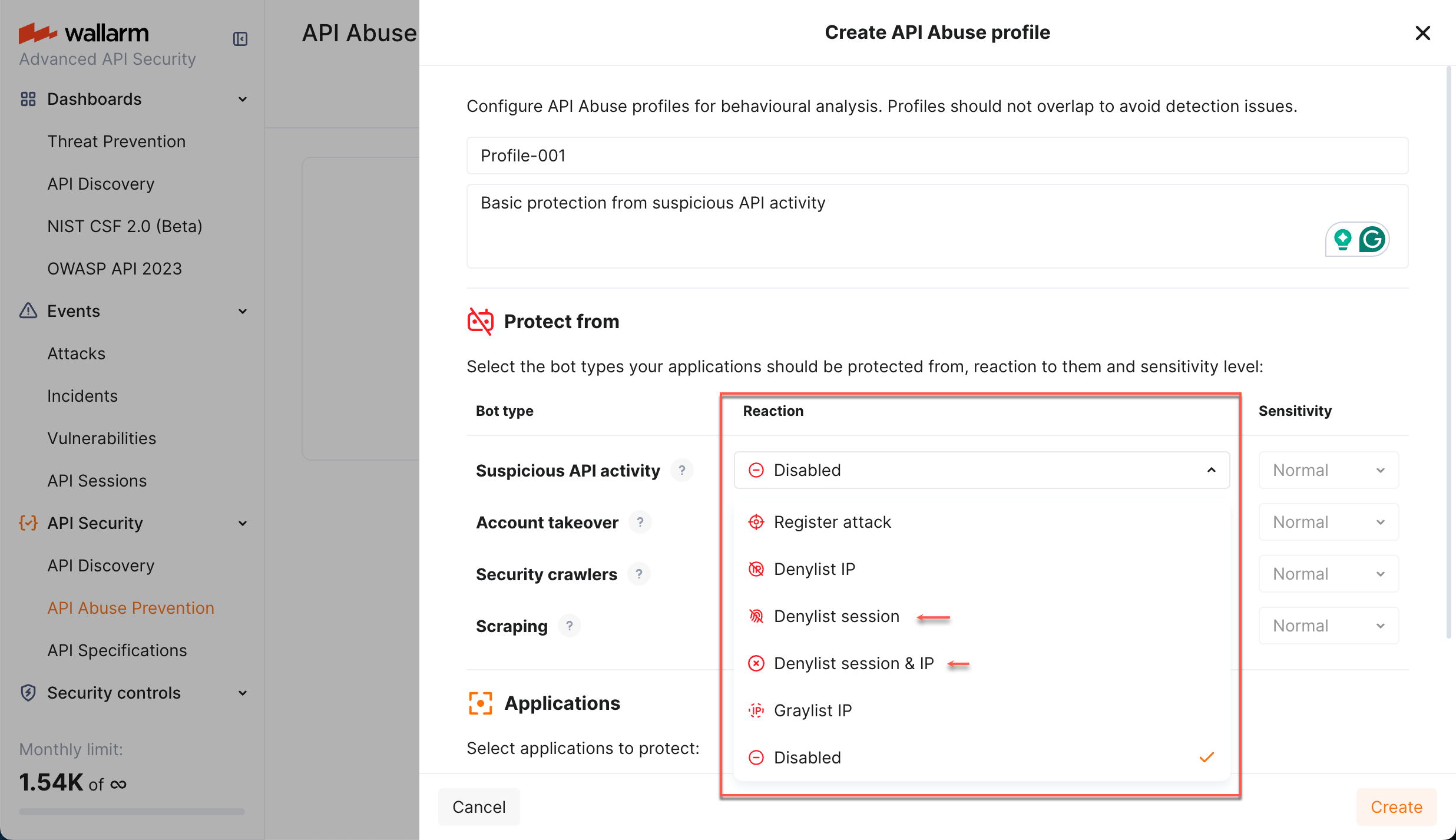
Session Blocking Wallarm Documentation Now, you can secure apis by completely blocking malicious api sessions, not just requests or ips. Instead of analyzing individual requests in isolation, this feature groups them into logical sessions that represent actual user journeys. this article gives an overview of api sessions: issues addressed by it, its purpose and main possibilities. Configuration of the blocking page and error code is supported in nginx based wallarm node deployments but is not supported in envoy and cdn based wallarm node deployments. As soon as wallarm's api sessions identified user sessions related to your applications, you can explore them in the api sessions section of wallarm console. learn from this article how to go through the discovered data.
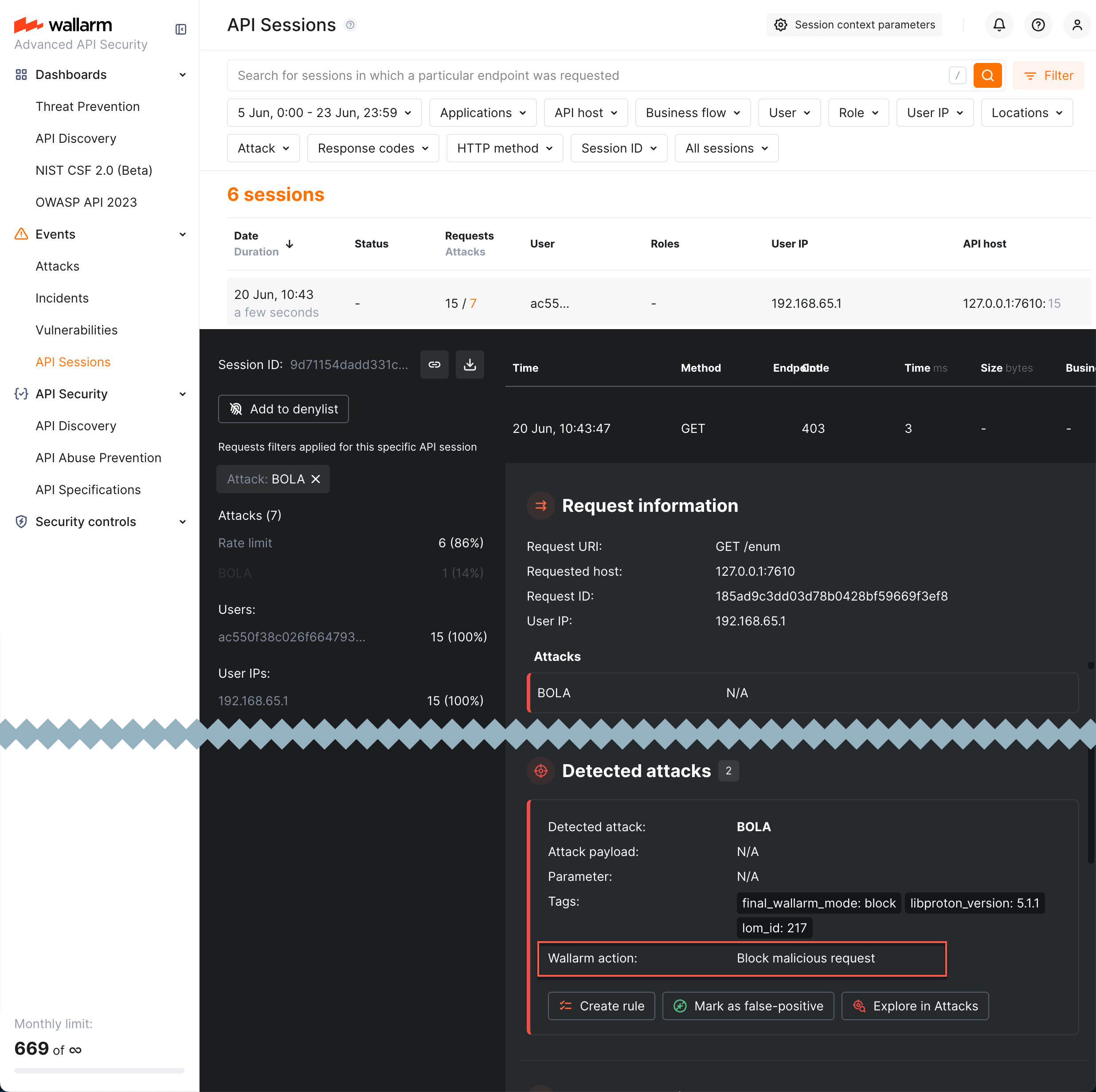
Session Blocking Wallarm Documentation Configuration of the blocking page and error code is supported in nginx based wallarm node deployments but is not supported in envoy and cdn based wallarm node deployments. As soon as wallarm's api sessions identified user sessions related to your applications, you can explore them in the api sessions section of wallarm console. learn from this article how to go through the discovered data. Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection. Api sessions include the built in rules for the session identification and requires only enabled wallarm node to start working. optionally, you can fine tune api sessions under your needs as described in this article. Wallarm provides the ability to block the use of specific authentication tokens in traffic. wallarm users can create virtual patch rules that block based on a regular expression in a specific header or request point. Use rate limiting to slow the incoming traffic and brute force protection to completely block the attacker. besides basic brute force protection, you can configure basic protection against forced browsing similarly.
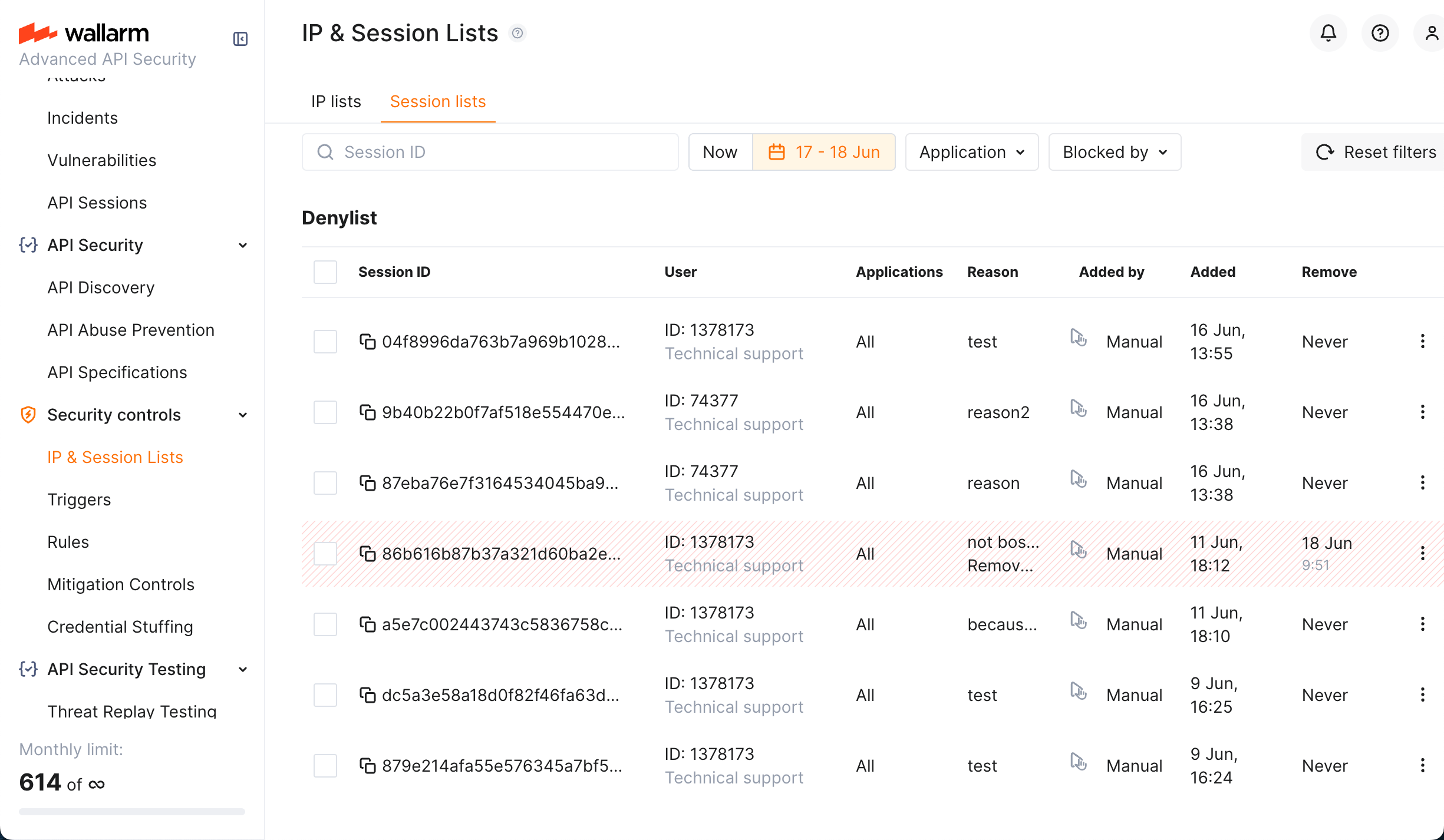
Session Blocking Wallarm Documentation Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection. Api sessions include the built in rules for the session identification and requires only enabled wallarm node to start working. optionally, you can fine tune api sessions under your needs as described in this article. Wallarm provides the ability to block the use of specific authentication tokens in traffic. wallarm users can create virtual patch rules that block based on a regular expression in a specific header or request point. Use rate limiting to slow the incoming traffic and brute force protection to completely block the attacker. besides basic brute force protection, you can configure basic protection against forced browsing similarly.
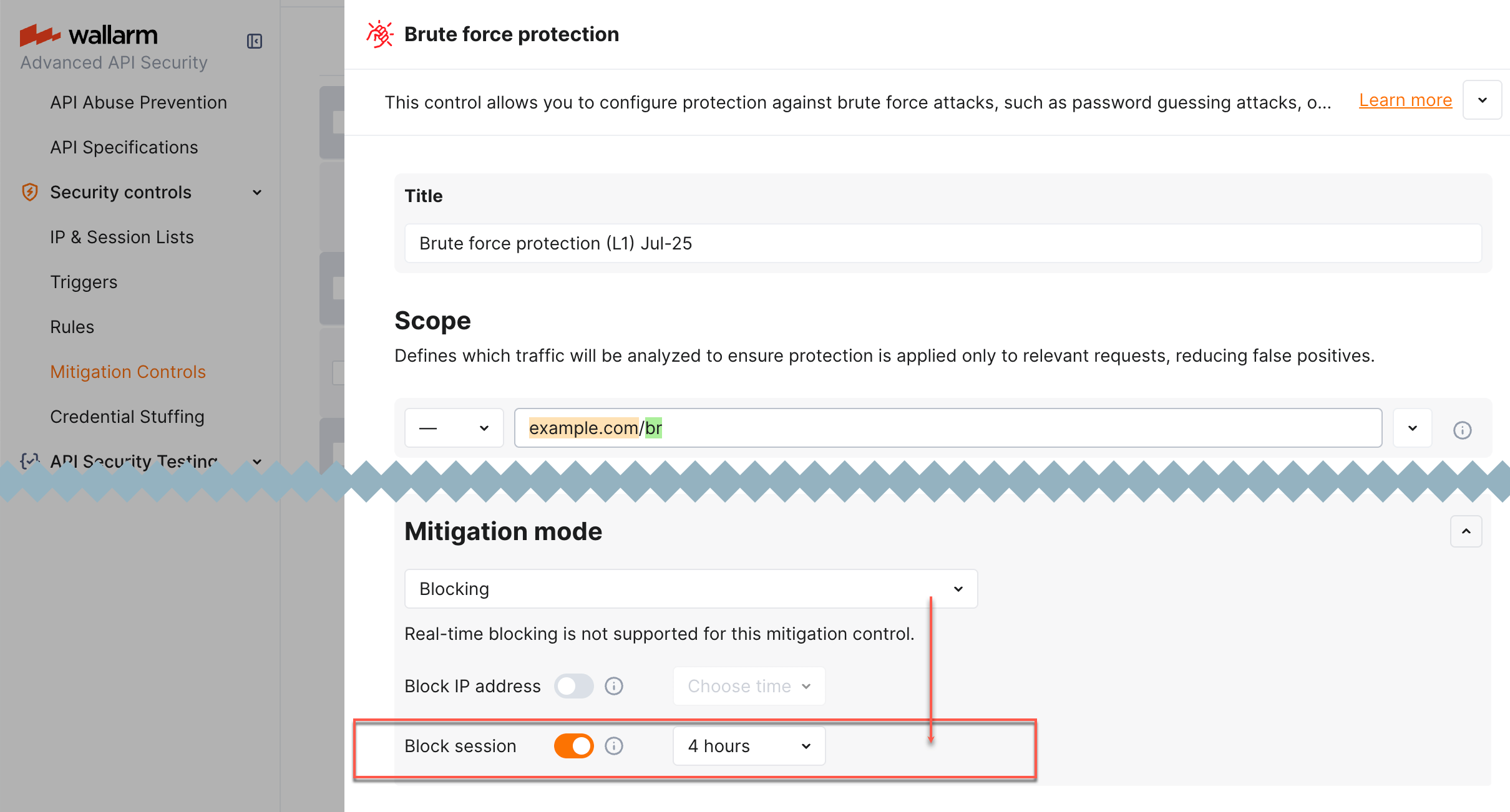
Session Blocking Wallarm Documentation Wallarm provides the ability to block the use of specific authentication tokens in traffic. wallarm users can create virtual patch rules that block based on a regular expression in a specific header or request point. Use rate limiting to slow the incoming traffic and brute force protection to completely block the attacker. besides basic brute force protection, you can configure basic protection against forced browsing similarly.
Comments are closed.