Server Side Request Forgery Ssrf System Design
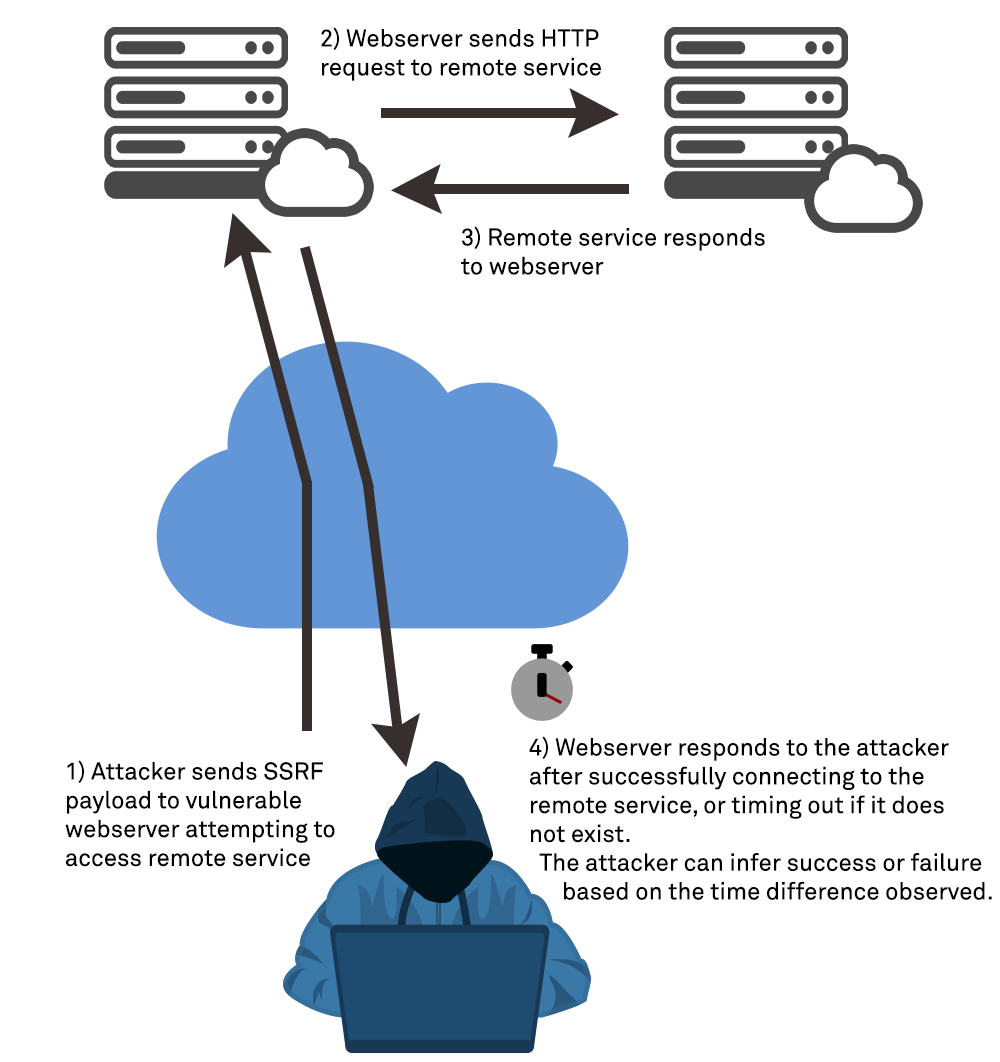
Server Side Request Forgery Ssrf The Cloud Resurgence In this chapter, we learned about the causes of server side request forgery attacks, the risks associated with these attacks, the damage that can result from them, and saw two real world examples where ssrf attacks caused serious damage. 1. what is ssrf? server side request forgery (ssrf) is a type of attack where an attacker tricks a server into making requests to other systems on its behalf.

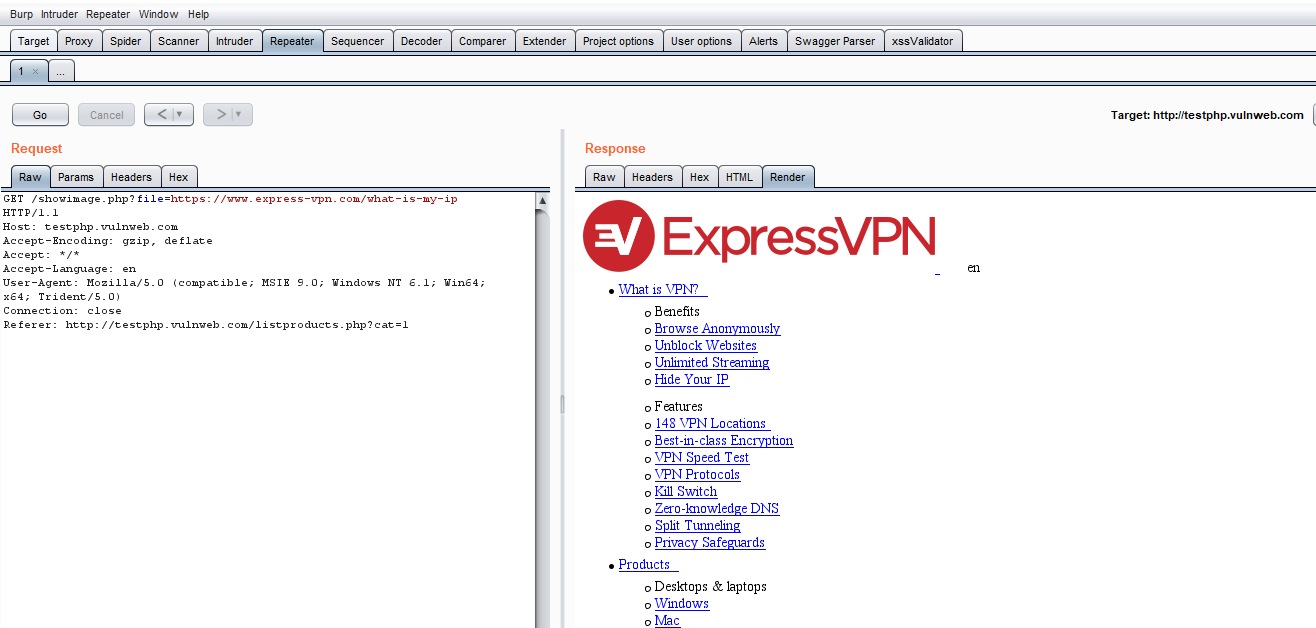
Server Side Request Forgery Ssrf The Cloud Resurgence In this section we explain what server side request forgery (ssrf) is, and describe some common examples. we also show you how to find and exploit ssrf vulnerabilities. Server‑side request forgery (ssrf) is a vulnerability that allows an attacker to make network requests to arbitrary destinations. ssrf makes these requests originate from within a server itself, which typically has broader access than an external client. Server side request forgery (ssrf) is a web vulnerability that occurs when an application accepts a user supplied url or request parameter and makes a server side request on the user’s behalf — without proper validation or restrictions. Below, we explore the primary methods for exploiting ssrf, drawn from bug bounty reports, conference presentations, and expert insights. these techniques are tailored for penetration testers working on authorized applications.
Server Side Request Forgery Ssrf Attacks How To Prevent Them Server side request forgery (ssrf) is a web vulnerability that occurs when an application accepts a user supplied url or request parameter and makes a server side request on the user’s behalf — without proper validation or restrictions. Below, we explore the primary methods for exploiting ssrf, drawn from bug bounty reports, conference presentations, and expert insights. these techniques are tailored for penetration testers working on authorized applications. Learn how to protect your code from server side request forgery (ssrf) attacks by exploiting a vulnerable web app as part of this snyk learn tutorial. Server side request forgery (ssrf) is a web vulnerability that continues to modern applications — especially cloud platforms, and misconfigured internal services. this article walks you through the mechanics of ssrf with a real world inspired example, explains its risks, and provides a step by step walkthrough of how an attack might unfold. In a server side request forgery (ssrf) attack, the attacker can abuse functionality on the server to read or update internal resources. Learn how to test and exploit server side request forgery (ssrf) vulnerabilities including detection, attack methods and bypass techniques.

Understanding Server Side Request Forgery Ssrf And How To Prevent It Learn how to protect your code from server side request forgery (ssrf) attacks by exploiting a vulnerable web app as part of this snyk learn tutorial. Server side request forgery (ssrf) is a web vulnerability that continues to modern applications — especially cloud platforms, and misconfigured internal services. this article walks you through the mechanics of ssrf with a real world inspired example, explains its risks, and provides a step by step walkthrough of how an attack might unfold. In a server side request forgery (ssrf) attack, the attacker can abuse functionality on the server to read or update internal resources. Learn how to test and exploit server side request forgery (ssrf) vulnerabilities including detection, attack methods and bypass techniques.

Server Side Request Forgery Ssrf In a server side request forgery (ssrf) attack, the attacker can abuse functionality on the server to read or update internal resources. Learn how to test and exploit server side request forgery (ssrf) vulnerabilities including detection, attack methods and bypass techniques.
Server Side Request Forgery Ssrf
Comments are closed.