Security Vulnerability Analysis Devpost
Security Vulnerability Analysis Devpost This approach highlights the technical depth, practical implementation, and future roadmap of your security vulnerability analysis microservice project for github repositories, positioning it effectively for the perplexity hackathon showcase. Learn what vulnerability analysis is, how it works, key tools, and why it is critical for cybersecurity. a complete beginner to advanced guide by ec council.
Security Vulnerability Analysis Devpost Conduct a vulnerability scan of your it infrastructure and compile a comprehensive list of the security dangers lurking beneath the surface. to complete this phase, perform an automated vulnerability scan and a manual penetration test to confirm findings and reduce false positives. Learn how to conduct a vulnerability assessment process and discover if it can help keep your organization safe from known and zero day vulnerabilities. The application provides comprehensive security analysis through an intuitive web interface. users can submit either code snippets or urls for analysis, and the ai powered backend examines the input for potential security vulnerabilities. A hands on web security lab demonstrating common vulnerabilities such as sql injection, xss, idor, and csrf alongside secure implementation techniques. includes automated testing, comparative analysis, and structured security reporting.
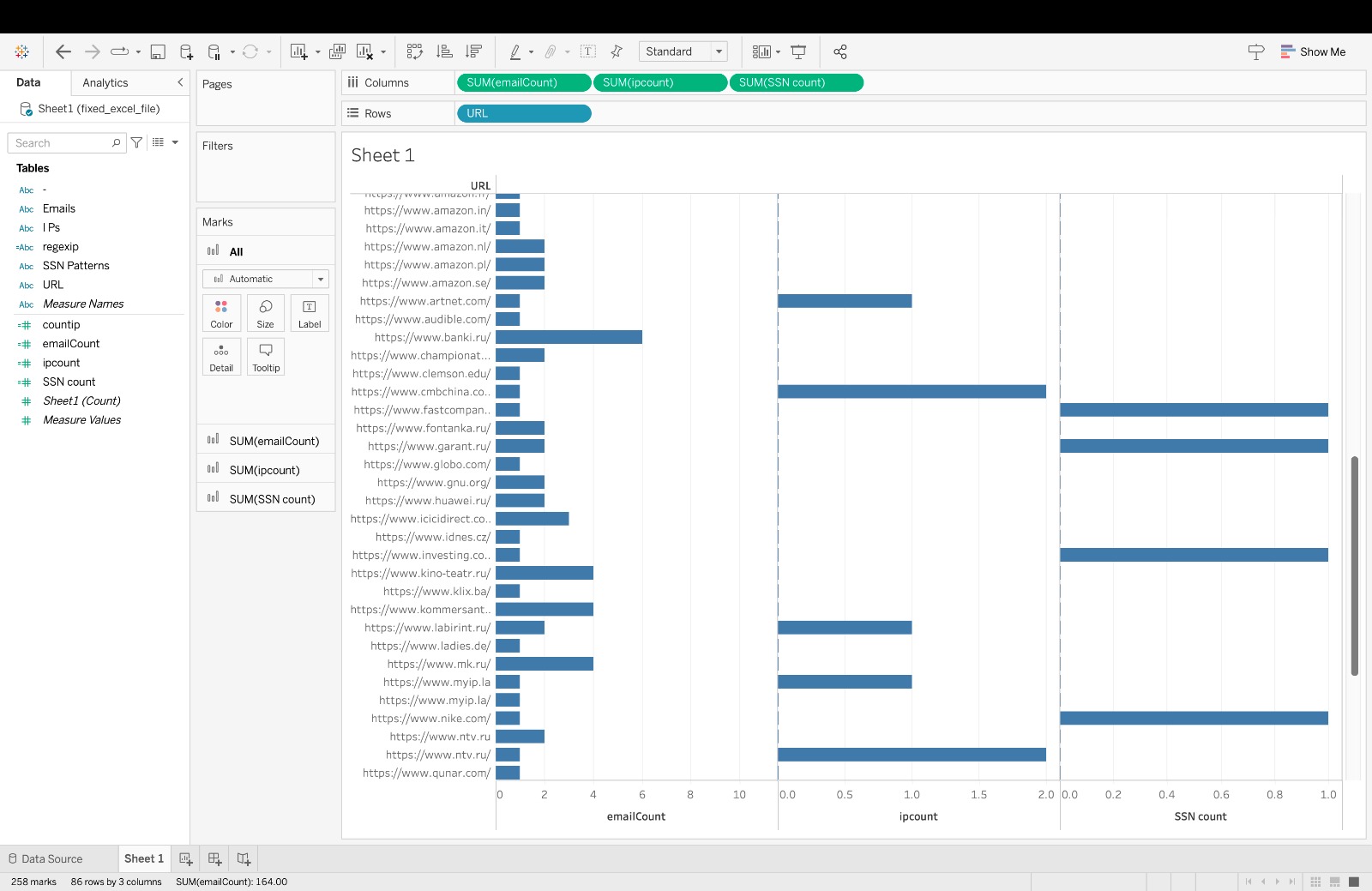
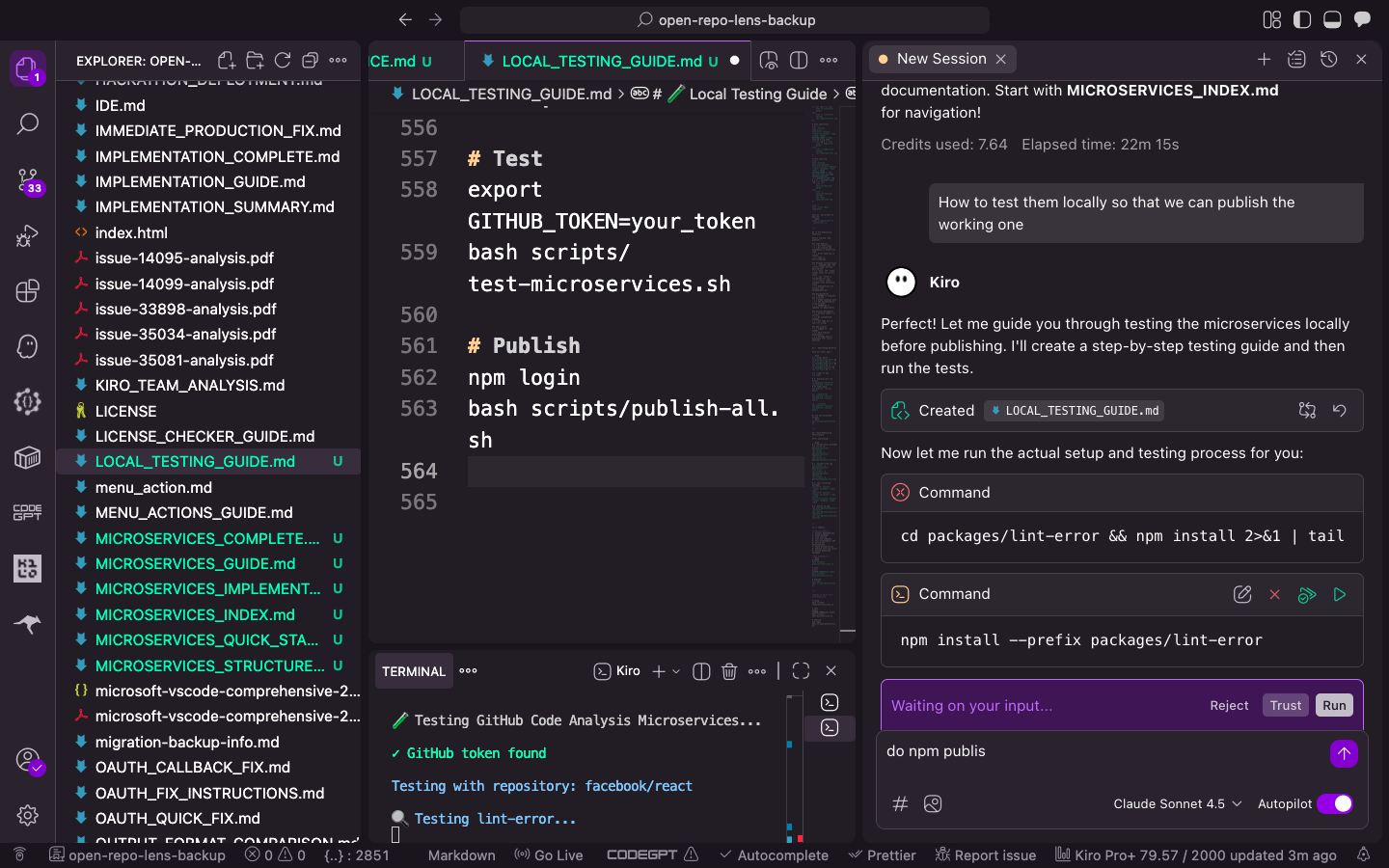
Websentinel Website Vulnerability Analyzer Devpost The application provides comprehensive security analysis through an intuitive web interface. users can submit either code snippets or urls for analysis, and the ai powered backend examines the input for potential security vulnerabilities. A hands on web security lab demonstrating common vulnerabilities such as sql injection, xss, idor, and csrf alongside secure implementation techniques. includes automated testing, comparative analysis, and structured security reporting. It systematically analyzes source code to detect complexity issues, security vulnerabilities, and non compliance with coding standards using a hybrid approach that combines llm based reasoning with rule based validation. The system performs a systematic 7 step security audit spanning reconnaissance, secret detection, dependency analysis, code vulnerability scans, and configuration audits. it reviews merge request diffs for security anti patterns and posts inline code comments with severity levels and concrete fix suggestions directly on the vulnerable lines. Vulnpilot: ai powered security scanning and automated workflows to identify, understand, and remediate vulnerabilities in your code and infrastructure. security vulnerability scanning often feels like a "black box" for developers. While we don’t have a bug bounty program, we do welcome skilled individuals who come across vulnerabilities on our site to share issues that may impact the security of devpost. if you believe you have found a vulnerability on our site, we’ll be happy to look into it.
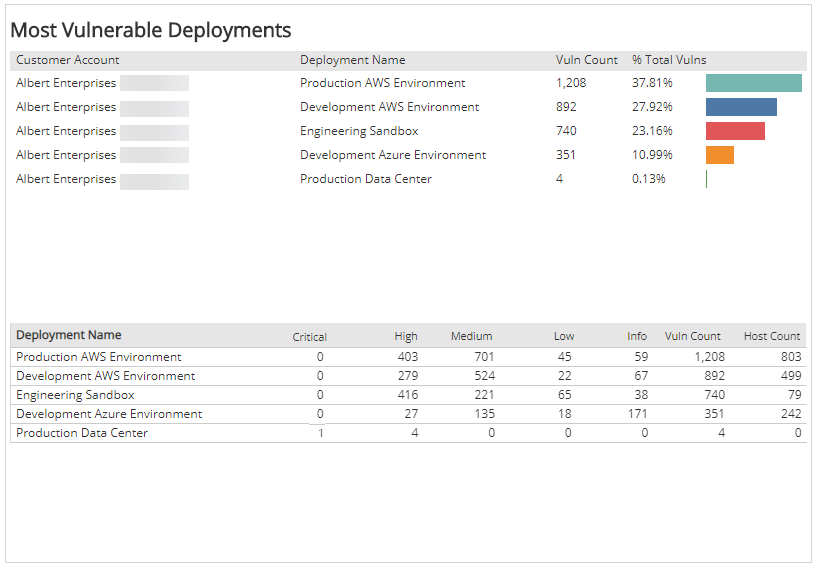
Monthly Vulnerability Analysis It systematically analyzes source code to detect complexity issues, security vulnerabilities, and non compliance with coding standards using a hybrid approach that combines llm based reasoning with rule based validation. The system performs a systematic 7 step security audit spanning reconnaissance, secret detection, dependency analysis, code vulnerability scans, and configuration audits. it reviews merge request diffs for security anti patterns and posts inline code comments with severity levels and concrete fix suggestions directly on the vulnerable lines. Vulnpilot: ai powered security scanning and automated workflows to identify, understand, and remediate vulnerabilities in your code and infrastructure. security vulnerability scanning often feels like a "black box" for developers. While we don’t have a bug bounty program, we do welcome skilled individuals who come across vulnerabilities on our site to share issues that may impact the security of devpost. if you believe you have found a vulnerability on our site, we’ll be happy to look into it.
Comments are closed.