Security Triad And Aaa Services Explained Pdf Information Security

Information Security Cia Triad Pdf The document discusses security concepts including the security triad of confidentiality, integrity and availability. it defines each component and provides examples. This article has defined the three important goals of cybersecurity referred to as the cia model and the aaa model, which is one of the methods through which these objectives are achieved.
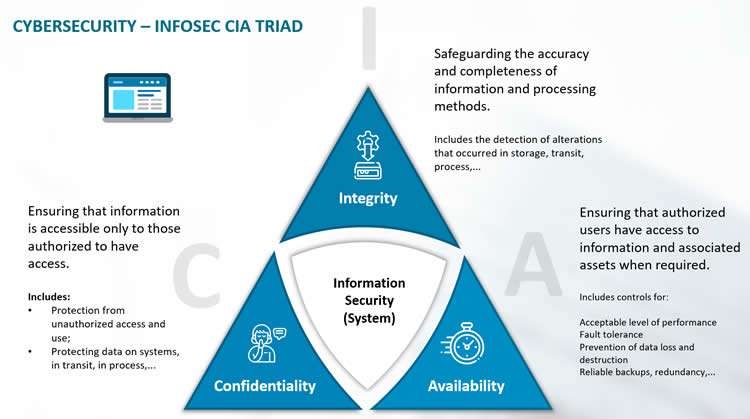
Information Security Cia Triad Availability can be impacted by natural (fire, floods, hurricanes), environmental (power outage), or artificial (ddos attack) events. flexible and can be applied to different types of information systems and organizations, regardless of size or industry. Abdullah security* information security cia triad cybersecurity framework gap analysis access control iam and aaa techcampus review: security concepts @techcampuscom. This article reviews the post‐quantum security threats of edge devices and systems and the secure methods developed for them. although there is relatively little research in this field, it. It is a discipline to protect data, hardware, software, and networked systems from cyber attackers and malicious users. it’s a risk that can harm a computer system or network, making it partially or completely unavailable, or compromise the confidentiality and integrity of data.

Information Security Cia Triad This article reviews the post‐quantum security threats of edge devices and systems and the secure methods developed for them. although there is relatively little research in this field, it. It is a discipline to protect data, hardware, software, and networked systems from cyber attackers and malicious users. it’s a risk that can harm a computer system or network, making it partially or completely unavailable, or compromise the confidentiality and integrity of data. Aaa and its combined processes play a major role in network management and cybersecurity by screening users and keeping track of their activity while they are connected, aligning with the principles of the cia triad to ensure data security. This chapter describes authentication, authorization, and accounting (aaa, pronounced “triple a”). aaa is a a set of services for controlling access to computer resources, enforcing policies, assessing usage, and providing the information necessary to bill for services. Explain the role of the three a's in the aaa model as applied to cybersecurity. key security concepts availability integrity confidentiality discussion post does the cia triad cover all aspects of cybersecurity?. Dive into the cia triad and discover how aaa reinforces cybersecurity measures to bolster data protection.
Comments are closed.