Security Protocols Pdf

Security Protocols Pdf Transport Layer Security Communications Security protocols are considered abstract when analyzed, but they can have extra vulnerabilities when implemented. this manuscript provides a holistic study on security protocols. Dishonest participants: hostile agents that claim to be honest, but try to prevent the security goals from being achieved. security protocols are about alice and bob.
11 Implementing Secure Network Protocols Pdf Transport Layer Transport layer security (tls) is a cryptographic protocol that operates above the transport layer to provide security services to applications tls runs over tcp. Figure 1: confidentiality and authentication for informa tion security can be provided in three different layers in the tcp ip protocol stack, as shown in this figure. Network security protocols generally implement cryptography and encryption techniques to secure the data so that it can only be decrypted. The paper discusses the theoretical foundations of security protocols for networks, important cryptographic principles, and formal verification approaches. recent trends include blockchain technology, iot security, and the growth of 5g networks.
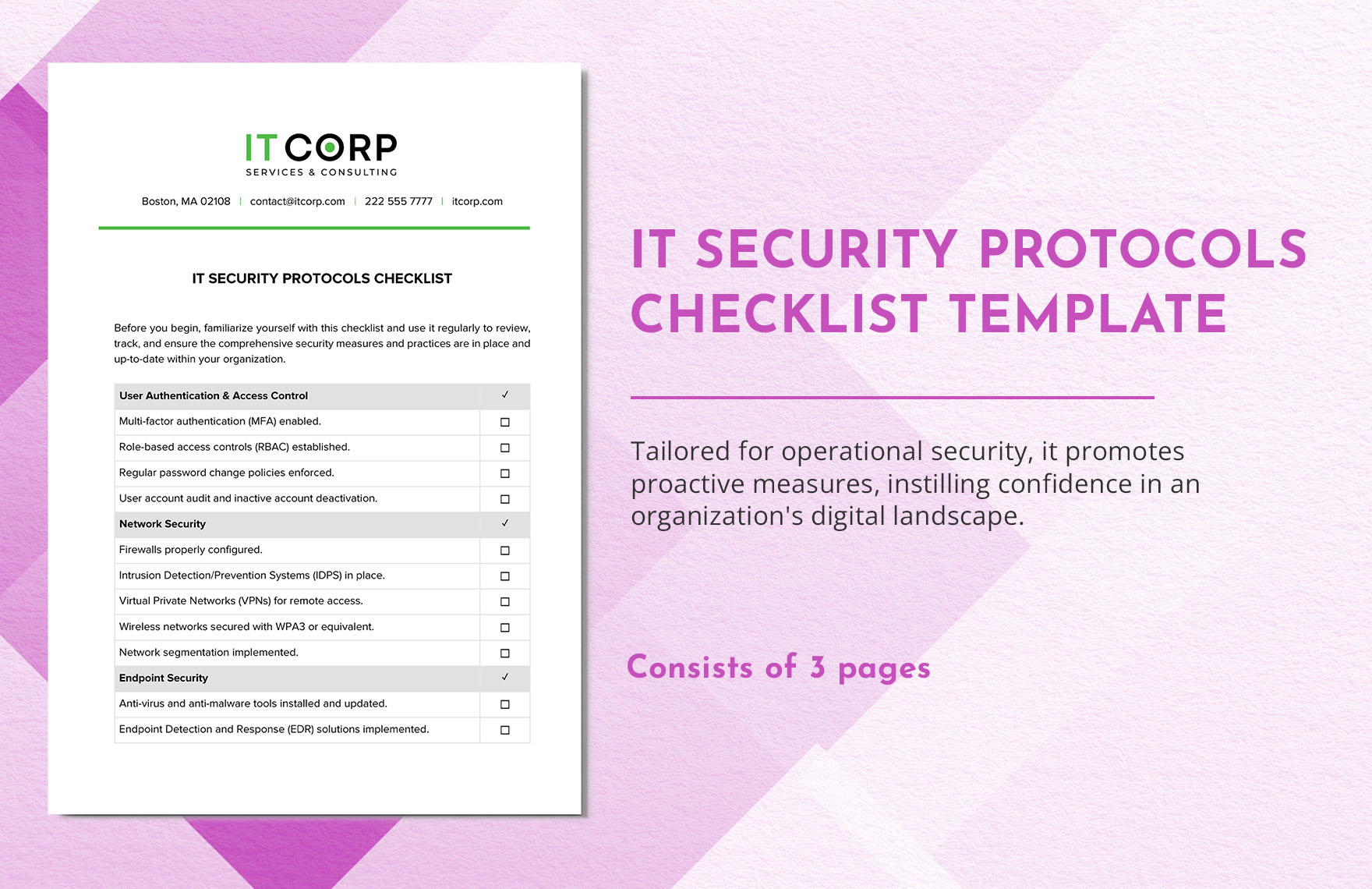
It Security Protocols Checklist Template In Word Pdf Google Docs Network security protocols generally implement cryptography and encryption techniques to secure the data so that it can only be decrypted. The paper discusses the theoretical foundations of security protocols for networks, important cryptographic principles, and formal verification approaches. recent trends include blockchain technology, iot security, and the growth of 5g networks. In particular, the information should identify the protocol, the protocol variant, the message number, and the particular position within the message, from which the component was sent.”. Security protocols giampaolo bella, frederic blanqui, lawrence c. paulson et al. march 13, 2025. In section 1.2, we consider modeling and verification in the context of security protocol development, and we introduce the fundamentals like the attacker model and security properties. then, in section 1.3, we discuss the theoretical and practical challenges in automated verification. Routing (bgp) bgp (border gateway protocol): protocol that allows routers to exchange information about their routing tables each router announces what it can route to all of its neighbors. every router maintains a global table of routes.

Internet Security Protocols Pdf Transport Layer Security Internet In particular, the information should identify the protocol, the protocol variant, the message number, and the particular position within the message, from which the component was sent.”. Security protocols giampaolo bella, frederic blanqui, lawrence c. paulson et al. march 13, 2025. In section 1.2, we consider modeling and verification in the context of security protocol development, and we introduce the fundamentals like the attacker model and security properties. then, in section 1.3, we discuss the theoretical and practical challenges in automated verification. Routing (bgp) bgp (border gateway protocol): protocol that allows routers to exchange information about their routing tables each router announces what it can route to all of its neighbors. every router maintains a global table of routes.
Comments are closed.