Security Notes 3 Pdf Cryptography Key Cryptography
Cryptography And Network Security Notes Pdf Cyber security notes unit 3 free download as pdf file (.pdf), text file (.txt) or read online for free. the document provides an overview of cryptography, focusing on information theoretic security, key concepts, and various cryptographic methods such as symmetric and asymmetric encryption. Case studies on cryptography and security: secure multiparty calculation, virtual elections, single sign on, secure inter branch payment transactions, cross site scripting vulnerability.

Unit 3 Public Key Cryptography Pdf Public Key Cryptography There are, in general, three types of cryptographic schemes typically used to accomplish these goals: (1) secret key (or symmetric) cryptography, (2) public key (or asymmetric) cryptography, and (3) hash functions, each of which is described in the subsequent subsections. An assault on system security that derives from an intelligent threat; that is, an intelligent act that is a deliberate attempt (especially in the sense of a method or technique) to evade security services and violate the security policy of a system. Loading…. This definition introduces three key objectives that are at the heart of computer security.
Chapter 3 Cryptography Pdf Cryptography Key Cryptography Loading…. This definition introduces three key objectives that are at the heart of computer security. Symmetric key cryptography (also called symmetric key encryption or private key cryptography) is an encryption technique that uses one key to encrypt and decrypt messages. This page contains some useful information related to the course and the lecture notes. note that there are some useful buttons above the text, in particular one to download the notes as a well formatted pdf, for offline use. Asymmetric key public key cryptography asymmetric key cryptosystems public key cryptosystems use a pair of keys: public key (encryption key) and private key (decryption key). Cryptography can reformat and transform our data, making it safer on its trip between computers. the technology is based on the essentials of secret codes, augmented by modern mathematics that protects our data in powerful ways.
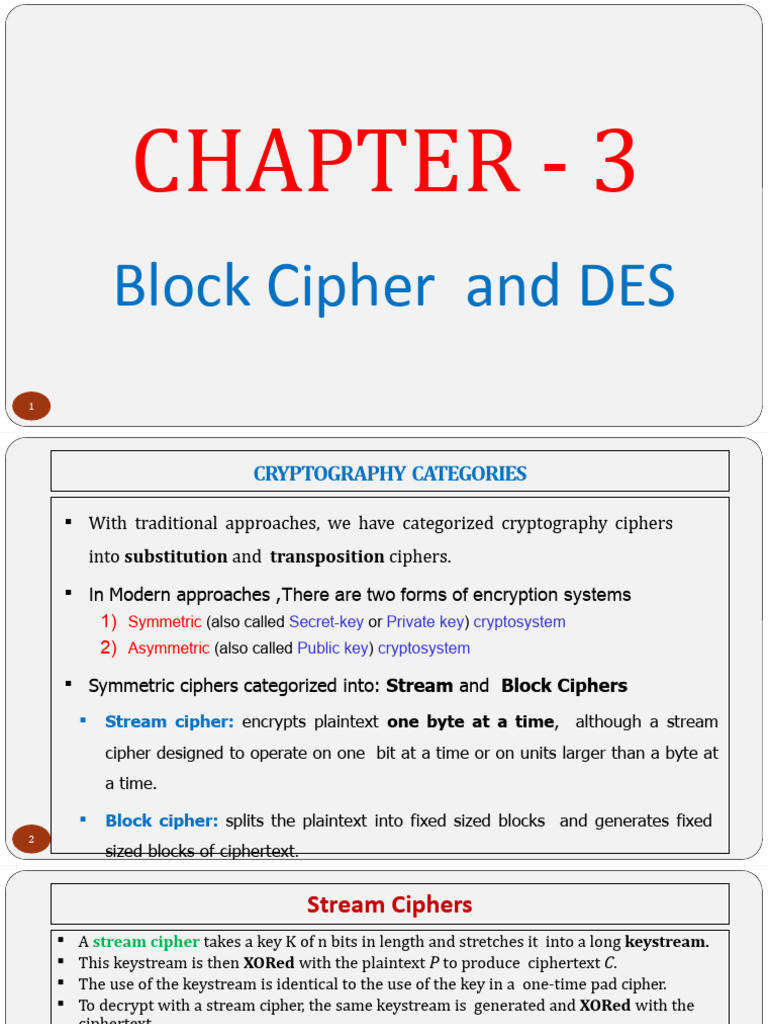
Chapter 3 Cryptography And Encryption Techniques Pdf Cryptography Symmetric key cryptography (also called symmetric key encryption or private key cryptography) is an encryption technique that uses one key to encrypt and decrypt messages. This page contains some useful information related to the course and the lecture notes. note that there are some useful buttons above the text, in particular one to download the notes as a well formatted pdf, for offline use. Asymmetric key public key cryptography asymmetric key cryptosystems public key cryptosystems use a pair of keys: public key (encryption key) and private key (decryption key). Cryptography can reformat and transform our data, making it safer on its trip between computers. the technology is based on the essentials of secret codes, augmented by modern mathematics that protects our data in powerful ways.

Cyber Security Notes Pdf Public Key Cryptography Security Technology Asymmetric key public key cryptography asymmetric key cryptosystems public key cryptosystems use a pair of keys: public key (encryption key) and private key (decryption key). Cryptography can reformat and transform our data, making it safer on its trip between computers. the technology is based on the essentials of secret codes, augmented by modern mathematics that protects our data in powerful ways.

Class Notes 3 Pdf Cryptography Espionage Techniques
Comments are closed.