Security Information And Event Management Evolution And Best Practices

Implementation Of Security Information Event Manag Pdf Security The changing nature of security threats, the proliferation of mobile devices, globalization, the explosion of social media, and quick changes in regulation are speeding the evolution of security information and event management. Explore how security information and event management (siem) fortifies cybersecurity, tackles challenges, and adapts for the future.
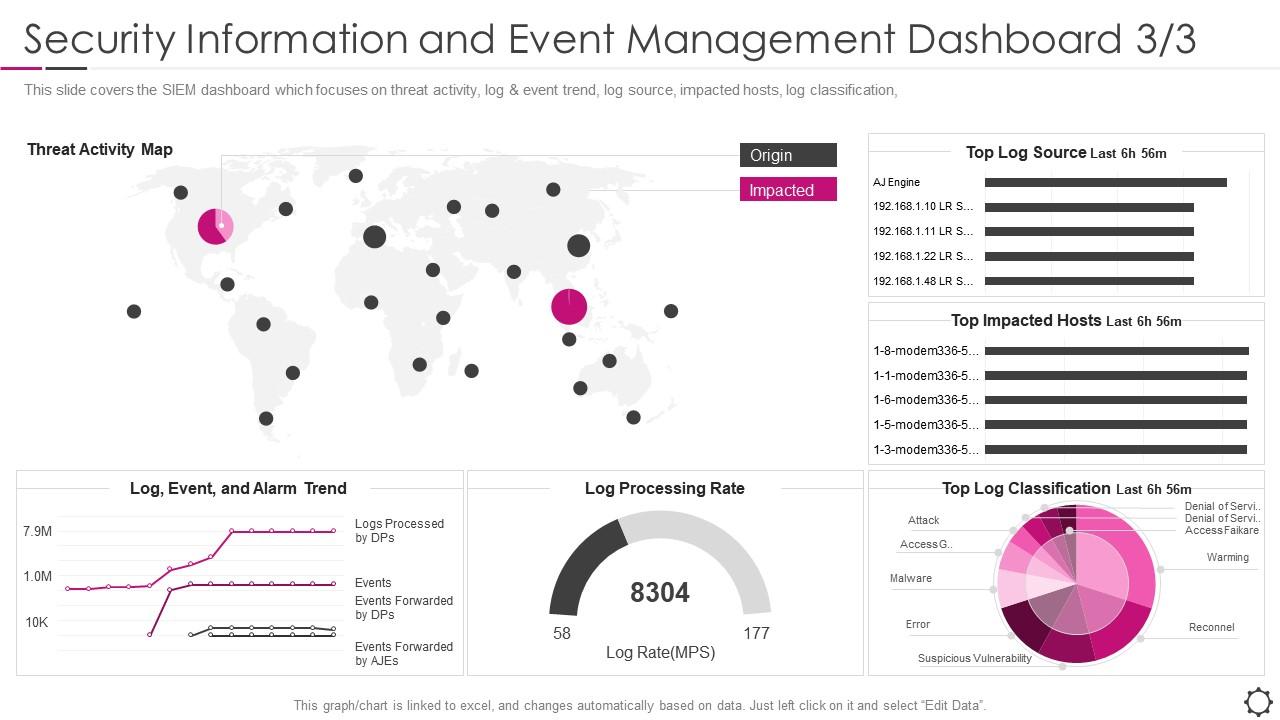
Security Event Management Security Information And Event Management We survey the most widely used siems regarding their critical functionality and provide an analysis of external factors affecting the siem landscape in mid and long term. Siem evolution including exploring the background, core characteristics, benefits, challenges, use cases, and best practices for implementation. It also helps decision makers compare different security information and event management solutions and identify the best fit for their security requirements. key trends shaping the siem market. Traditional security measures often fall short in detecting and mitigating these sophisticated attacks, necessitating advanced intrusion detection methods. the goal of our study is to develop robust network intrusion detection methods using machine learning techniques.

Security Information Event Management Siem It also helps decision makers compare different security information and event management solutions and identify the best fit for their security requirements. key trends shaping the siem market. Traditional security measures often fall short in detecting and mitigating these sophisticated attacks, necessitating advanced intrusion detection methods. the goal of our study is to develop robust network intrusion detection methods using machine learning techniques. Summary security information and event management (siem) systems play a crucial role in modern security operations centers by facilitating detection, investigat. Siem's driving force was to pinpoint threats in real time. read a history of siem to learn about its evolution and what to expect from its next gen versions. In the ever evolving landscape of cybersecurity, security information and event management (siem) has become a cornerstone technology. this vital system is essential for protecting sensitive data and maintaining the integrity of networks. Security information and event management (siem) technologies provide a holistic view of an organization information security, combining security information management and security event management capabilities into one security management system.
Security Information Event Management Siem 650 Group Summary security information and event management (siem) systems play a crucial role in modern security operations centers by facilitating detection, investigat. Siem's driving force was to pinpoint threats in real time. read a history of siem to learn about its evolution and what to expect from its next gen versions. In the ever evolving landscape of cybersecurity, security information and event management (siem) has become a cornerstone technology. this vital system is essential for protecting sensitive data and maintaining the integrity of networks. Security information and event management (siem) technologies provide a holistic view of an organization information security, combining security information management and security event management capabilities into one security management system.

Security Information And Event Management Siem Stock Image Image Of In the ever evolving landscape of cybersecurity, security information and event management (siem) has become a cornerstone technology. this vital system is essential for protecting sensitive data and maintaining the integrity of networks. Security information and event management (siem) technologies provide a holistic view of an organization information security, combining security information management and security event management capabilities into one security management system.

Security Information Event Management Security Information Event
Comments are closed.