Security Fundamentals

Fundamentals Of Security Pdf Information Security Phishing This exam is targeted to you, if you’re looking to familiarize yourself with the fundamentals of security, compliance, and identity (sci) across cloud based and related microsoft services. Understand the fundamentals of cybersecurity, such as detecting threats, protecting systems and networks, and anticipating potential cyberattacks.
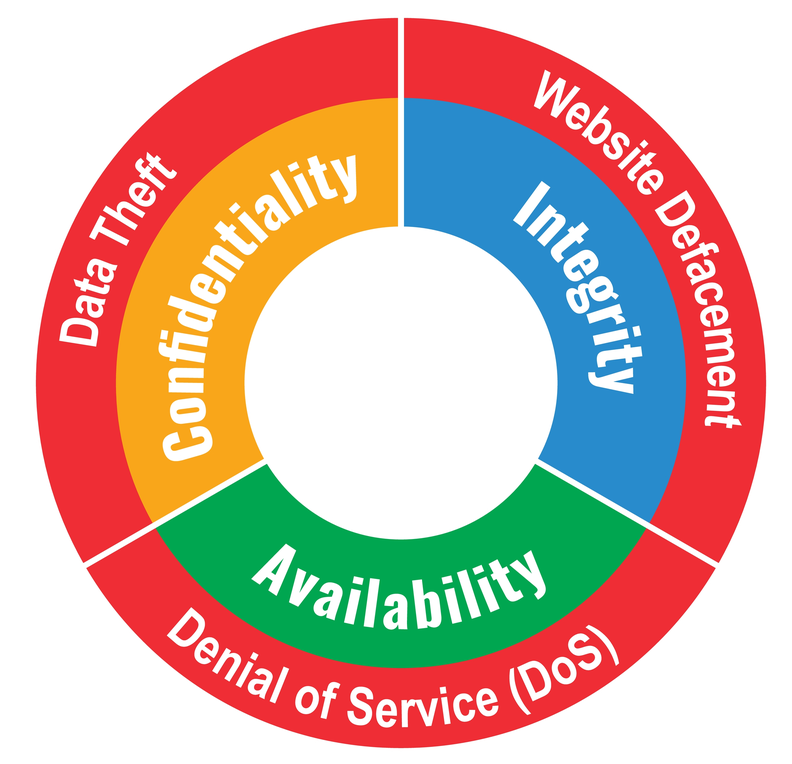
The Fundamentals Of Cybersecurity Allied It Systems Identify common security threats and risks; explain characteristics of cyberattacks and best practices to guard against them. discuss the foundational concepts of the five cybersecurity principles and the cia triad. In this course, you'll explore the fundamentals of security. you'll learn to define key security concepts, configure device access using local passwords, configure and verify access control lists, describe security program elements and more. Learn the cybersecurity fundamentals that will lay a foundation for securing your technology and personal life from dangerous cyber threats. includes cyber attacks, social engineering, threat actors, third party risks, intelligence sources, and more. The course is funded through the dhs fema homeland security national training program and is offered at no cost. this four hour web based course is an introduction to cybersecurity fundamentals for technologists and information technology managers.

Cyber Security Fundamentals Cosmas Scientific Publications Learn the cybersecurity fundamentals that will lay a foundation for securing your technology and personal life from dangerous cyber threats. includes cyber attacks, social engineering, threat actors, third party risks, intelligence sources, and more. The course is funded through the dhs fema homeland security national training program and is offered at no cost. this four hour web based course is an introduction to cybersecurity fundamentals for technologists and information technology managers. Learn the foundational concepts of network protection, covering segmentation, access control and monitoring for secure communication. explore how to capture, inspect and analyze network packets with wireshark to detect threats and troubleshoot issues. Learn cybersecurity basics to protect your personal digital life and the biggest security challenges companies face today. Explore cyber security standards and laws for red team and blue team professionals, including iso 27001, nist csf and rmf, pci dss, and global laws across the us, eu, and australia. Security is embedded in all we do online and is a critical job skill and career field. this foundations course explains security fundamentals including core principles, critical security controls, and cybersecurity best practices.
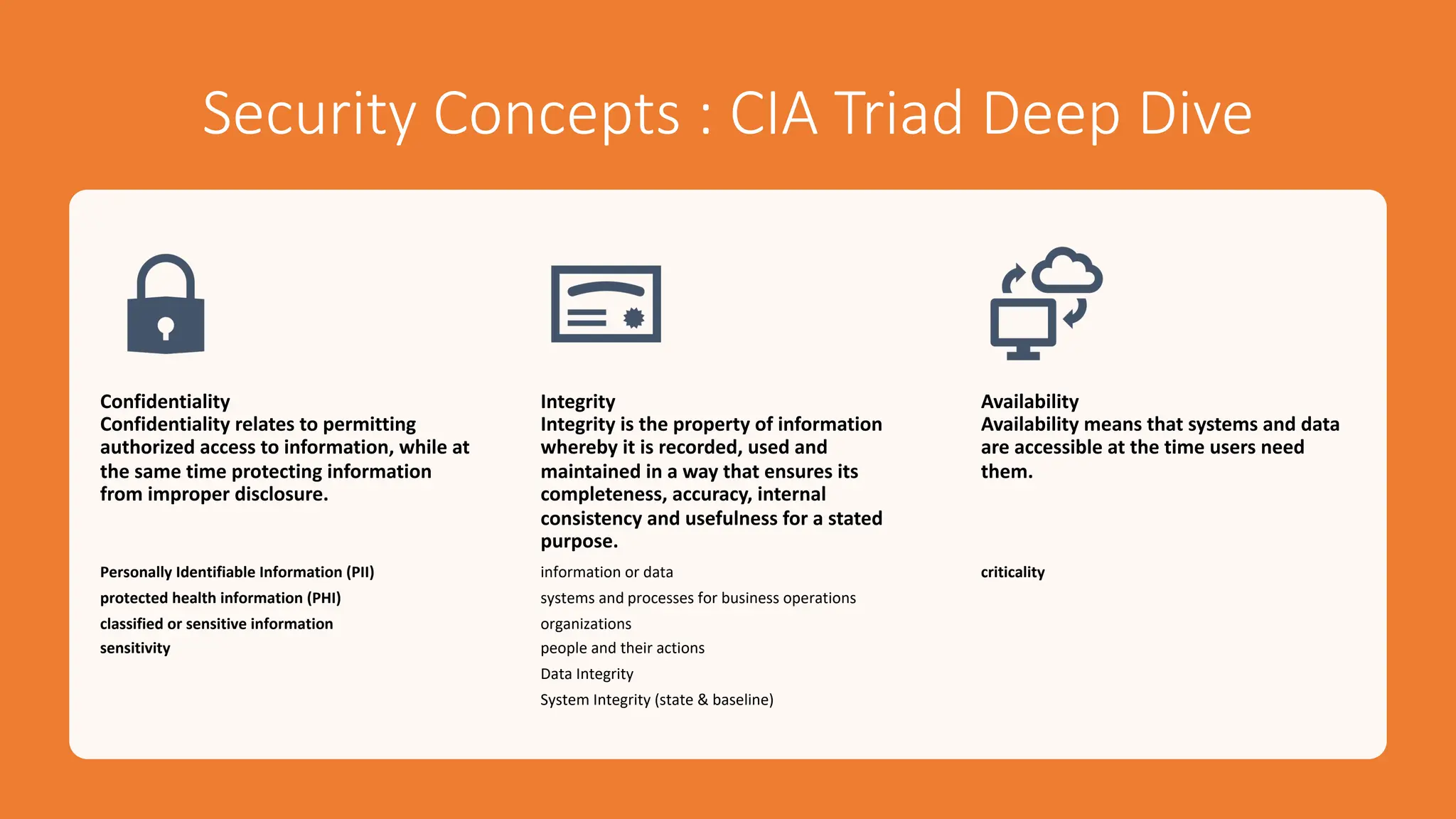
001 Cybersecurity Fundamentals Security Principles Pdf Learn the foundational concepts of network protection, covering segmentation, access control and monitoring for secure communication. explore how to capture, inspect and analyze network packets with wireshark to detect threats and troubleshoot issues. Learn cybersecurity basics to protect your personal digital life and the biggest security challenges companies face today. Explore cyber security standards and laws for red team and blue team professionals, including iso 27001, nist csf and rmf, pci dss, and global laws across the us, eu, and australia. Security is embedded in all we do online and is a critical job skill and career field. this foundations course explains security fundamentals including core principles, critical security controls, and cybersecurity best practices.
Comments are closed.