Security Compliance Risk Assessment
How To Conduct A Security Risk Assessment Learn how to conduct a security risk assessment to identify vulnerabilities and take action to safeguard your systems against cyber threats. A cybersecurity risk assessment is a structured evaluation of your organization’s information security risks. it identifies what could go wrong, how likely it is to happen, and what the impact would be if it does.

Compliance Risk Assessment A Step By Step Guide For Businesses Learn a step by step framework for conducting a security risk assessment, from scoping and evidence collection to prioritization and roadmap development. Learn the key steps and best practices for conducting a compliance risk assessment in 2025 to strengthen security, stay audit ready, and reduce overall risk. This guide walks through each component of a defensible framework — from risk identification through control assessment, third party risk management, and technology enablement — with current data, practitioner tools, and an implementation roadmap you can put to work this quarter. Learn how to conduct a security risk assessment, key steps, controls, and tools to protect your business from cyber and physical security threats.
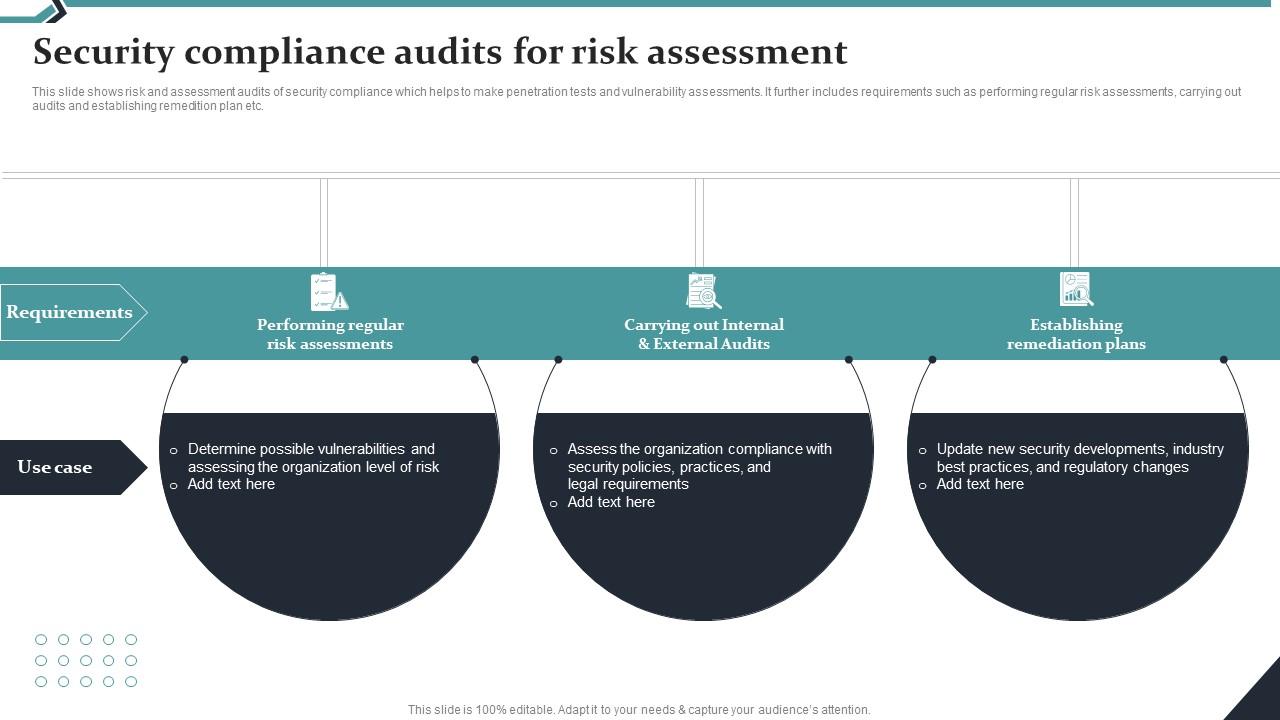
Security Compliance Audits For Risk Assessment Ppt Sample This guide walks through each component of a defensible framework — from risk identification through control assessment, third party risk management, and technology enablement — with current data, practitioner tools, and an implementation roadmap you can put to work this quarter. Learn how to conduct a security risk assessment, key steps, controls, and tools to protect your business from cyber and physical security threats. Learn how a compliance risk assessment process helps identify regulatory risks, evaluate controls, and implement mitigation strategies for stronger security. Discover how to conduct effective security risk assessments, explore benefits and challenges, and follow best practices for successful implementation. Most security teams treat risk assessments as a compliance checkbox, a periodic exercise that generates a thick report, collects dust for six months, and then gets repeated. the result? organizations discover their biggest exposures only after an incident, not before. a cybersecurity risk assessment, done right, is the foundation of every sound security strategy. it tells you what assets. What is a cybersecurity risk assessment? discover what a cybersecurity risk assessment entails and how it helps organizations put in place proactive, resilient security measures.
Comments are closed.