Security By Design For Mobile Application Development

Rh Isac Mobile Application Security Best Practices Rh Isac This article explores the evolving mobile threat landscape, reveals why conventional security practices fall short, and lays out a forward looking, secure by design approach for mobile app development especially for ios app development services and android platforms. The secure by design process is the operational playbook for applying secure by design during the design phase and engaging with appsec efficiently without creating bottlenecks.
Mobile Application Development Concept Mobile Programming Coding Multi While new technologies will always bring risks and create privacy and safety issues, we have created this document to address the threats posed by mobile applications. By embedding security considerations into architecture and engineering decisions, developers can avoid costly reworks, reputational harm, and breaches down the line. With a long history of expertise and a customer centric technique, we help you design and install mobile applications that meet the very best requirements—secure via design, compliant through default. Through detailed analysis of architectural patterns, security control implementations, and testing methodologies, this paper provides insights into effective security measures across the entire.
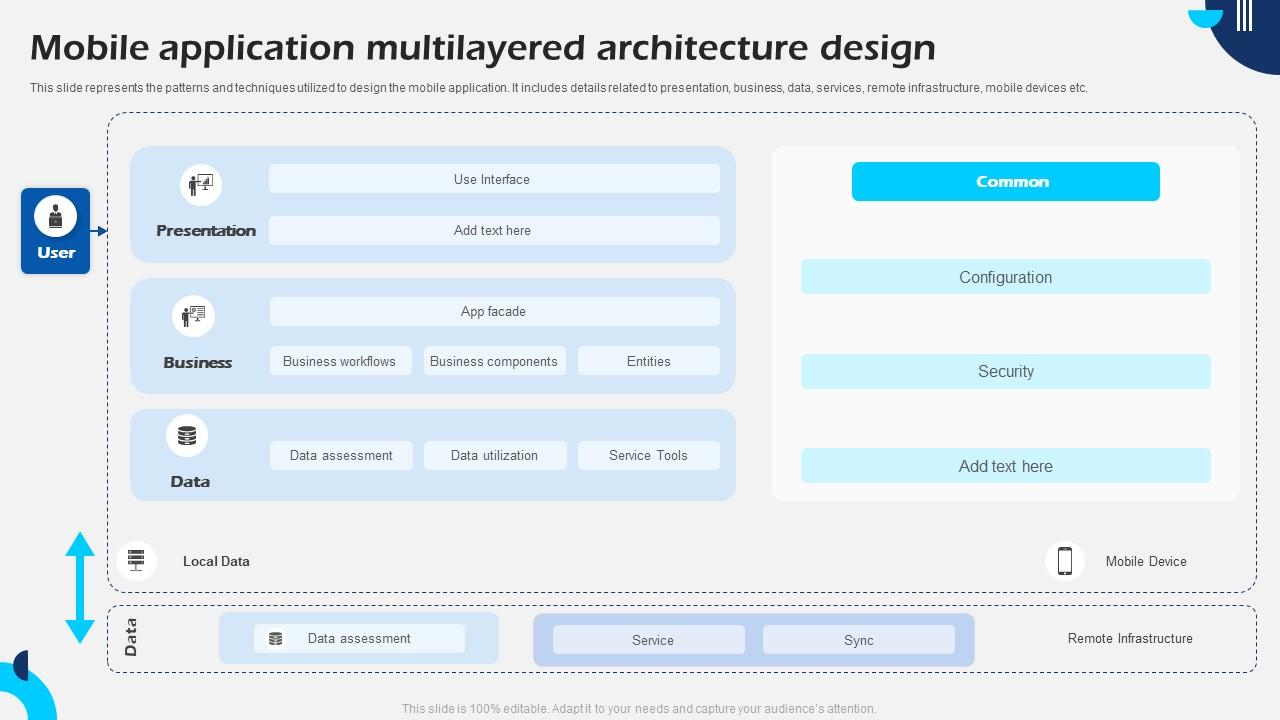
Mobile Application Multilayered Architecture Design Ppt Presentation With a long history of expertise and a customer centric technique, we help you design and install mobile applications that meet the very best requirements—secure via design, compliant through default. Through detailed analysis of architectural patterns, security control implementations, and testing methodologies, this paper provides insights into effective security measures across the entire. Here is a step by step guide to embedding security throughout the application lifecycle. this checklist is updated to address the challenges you will face in 2026 and beyond. Security by design for a long time, security was a bit of an afterthought in app development. but last minute fixes aren't adequate when faced with sophisticated attacks that can ruin business reputations. follow the seven security by design steps we've set out here to create safer apps for your end users. Master mobile app security by learning top risks, secure development practices, and compliance with standards like gdpr and owasp. This guide offers practical, risk based strategies for integrating security into every phase of the software development lifecycle — tailored to real world development environments.

Securing Mobile Application Development 9 Best Practices For Data Here is a step by step guide to embedding security throughout the application lifecycle. this checklist is updated to address the challenges you will face in 2026 and beyond. Security by design for a long time, security was a bit of an afterthought in app development. but last minute fixes aren't adequate when faced with sophisticated attacks that can ruin business reputations. follow the seven security by design steps we've set out here to create safer apps for your end users. Master mobile app security by learning top risks, secure development practices, and compliance with standards like gdpr and owasp. This guide offers practical, risk based strategies for integrating security into every phase of the software development lifecycle — tailored to real world development environments.

Mobile Application Security And Privacy An Inevitable Aspect Master mobile app security by learning top risks, secure development practices, and compliance with standards like gdpr and owasp. This guide offers practical, risk based strategies for integrating security into every phase of the software development lifecycle — tailored to real world development environments.
E Commerce Mobile Application Development Associative
Comments are closed.