Security Audit Pdf Audit Computer Security

Computer Security Audit Checklist Pdf Password File System 7001 for structured audits. this will ensure that your it security complies with current standards and that po. Security audit checklist free download as pdf file (.pdf), text file (.txt) or read online for free. the document outlines the daily and monthly security maintenance audit checklists for an organization's it systems.

Cybersecurity Audit Guide 1701218416 Pdf Computer Security Security Cybersecurity audit checklist 2025 edition use this checklist as your day one framework. adapt each item to your it infrastructure, industry regulations, and internal security maturity. this list is structured to help you identify vulnerabilities, address compliance requirements, and improve your organization’s information security posture. Download and use free security audit checklists to assess your organization’s security measures and address threats proactively. Cybersecurity audits ensure compliance and security are integrated into daily operations and development lifecycles. a checklist approach provides structure, simplifies audits, and supports continuous compliance. This checklist is designed to help businesses identify vulnerabilities, assess risks, and improve their overall cybersecurity posture. use it as a starting point to evaluate your current it security. step 1: network security do you have a business grade firewall installed and actively managed?.
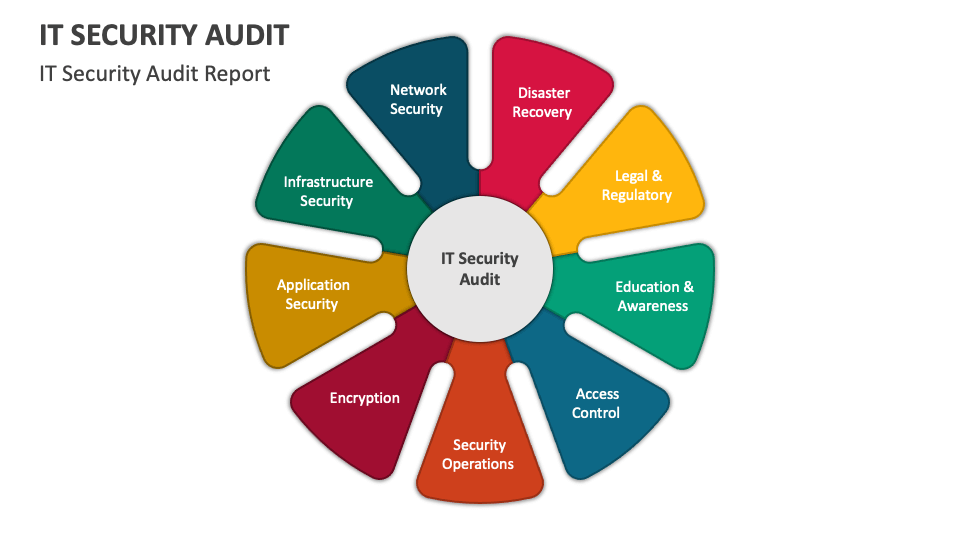
It Security Audit Powerpoint And Google Slides Template Ppt Slides Cybersecurity audits ensure compliance and security are integrated into daily operations and development lifecycles. a checklist approach provides structure, simplifies audits, and supports continuous compliance. This checklist is designed to help businesses identify vulnerabilities, assess risks, and improve their overall cybersecurity posture. use it as a starting point to evaluate your current it security. step 1: network security do you have a business grade firewall installed and actively managed?. This procedure covers

Download Free It Security Audit Checklist Template Captain It This procedure covers

Security Audit Checklist 2 Pdf Computer Security Security Global technology audit guides® (gtag®) provide auditors with the knowledge to perform assurance and advisory services related to an organization’s information technology and information security risks and controls. global guidance is available as a benefit of membership in the iia. An audit of cybersecurity operations should evaluate whether all appropriate personnel complete general and targeted security training, and whether the ciso ensures participation through monitoring, reporting, and other management controls.
Comments are closed.