Security Architecture Diagram For Cloud Potential Unlocking
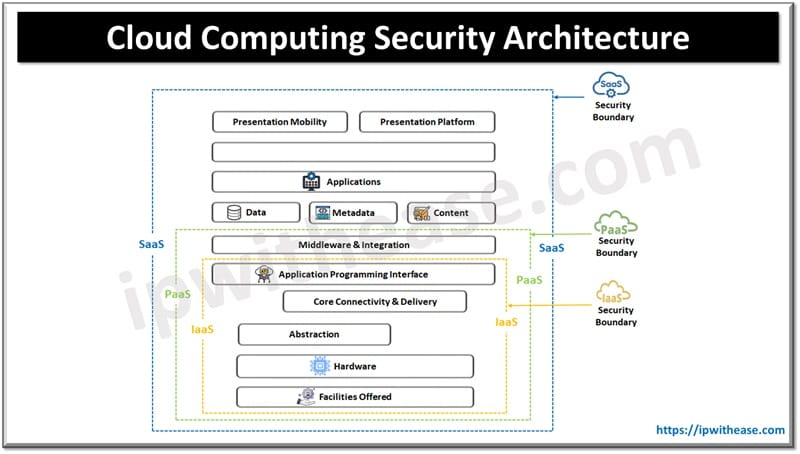
Cloud Computing Security Architecture 5 Key Components Ip With Ease Secure your data in google cloud with our gcp security architecture diagram template, combining iam policies, encryption, and network controls. This cheat sheet will discuss common and necessary security patterns to follow when creating and reviewing cloud architectures. each section will cover a specific security guideline or cloud design decision to consider.
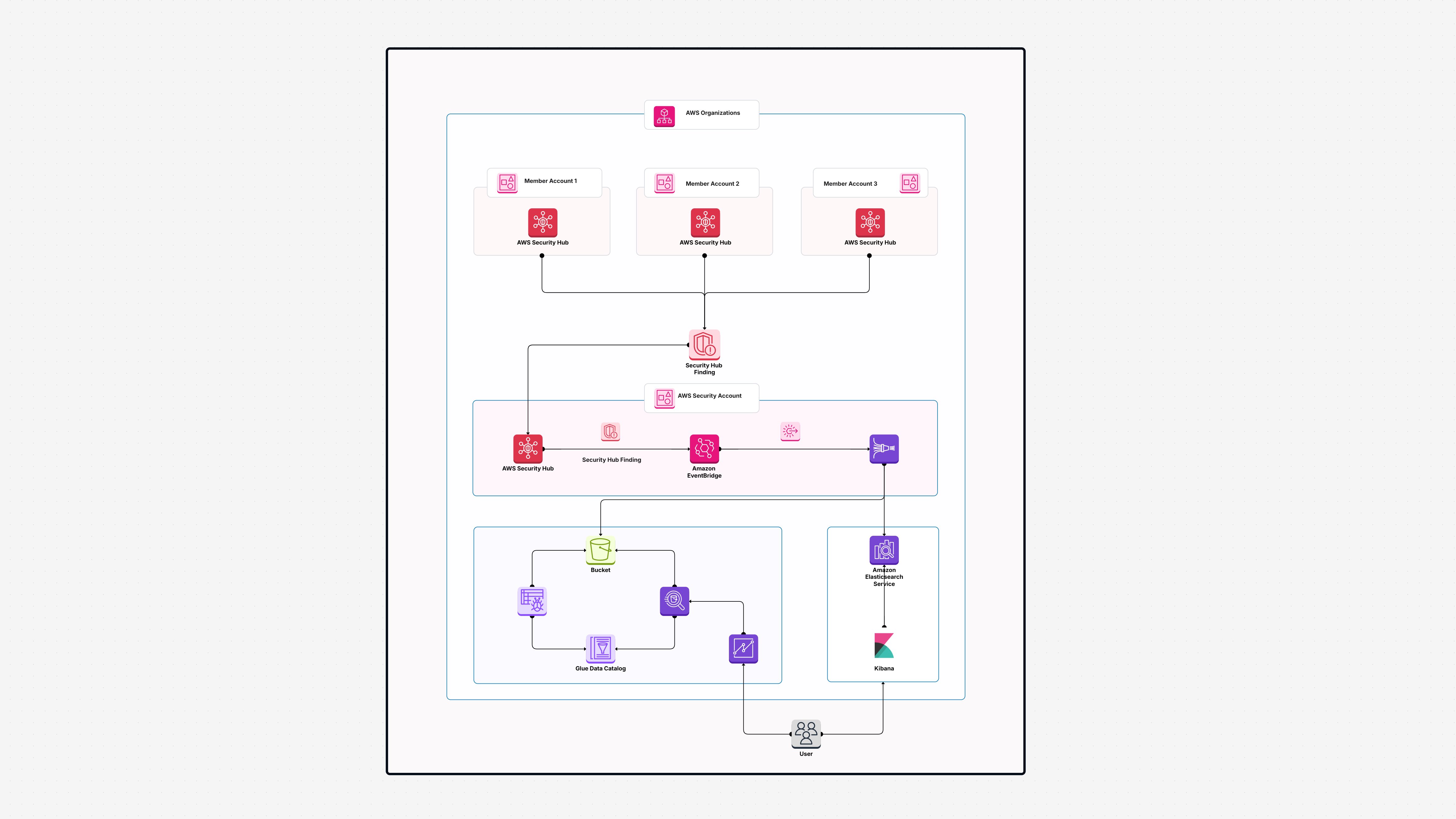
Security Architecture Diagram For Cloud Potential Unlocking This cheat sheet will discuss common and necessary security patterns to follow when creating and reviewing cloud architectures. each section will cover a specific security guideline or cloud design decision to consider. This article takes you through what cloud security architecture is important for, how it is implemented in the real world, the foundations it's developed on, and step by step methods to design your own secure cloud infrastructure. Learn how to create an effective cloud security architecture diagram. discover key strategies to enhance your cloud security architecture diagram today!. Every solid cloud security architecture can be explained as five layers. if you can talk through these layers, you can diagram almost any cloud environment and identify where risk is hiding.
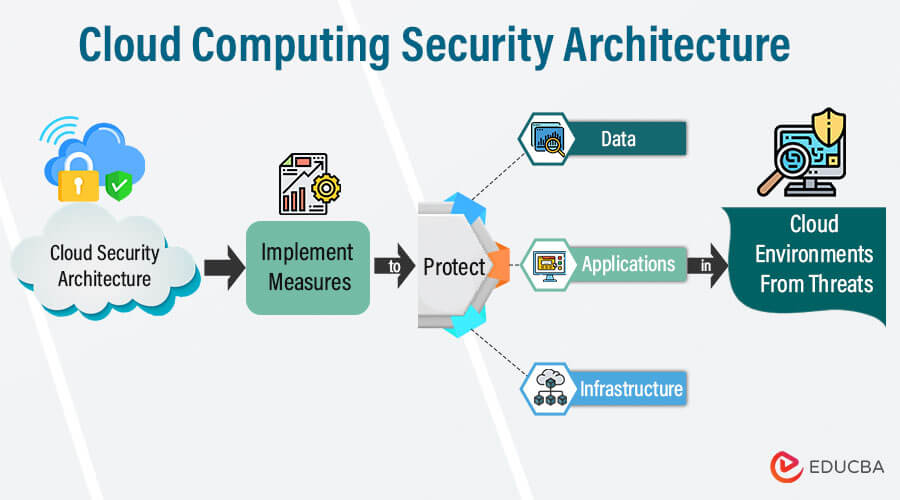
Cloud Computing Security Architecture Educba Learn how to create an effective cloud security architecture diagram. discover key strategies to enhance your cloud security architecture diagram today!. Every solid cloud security architecture can be explained as five layers. if you can talk through these layers, you can diagram almost any cloud environment and identify where risk is hiding. Secure cloud architecture owasp cheat sheet series free download as pdf file (.pdf), text file (.txt) or read online for free. risk analysis, threat modeling, and attack surface assessments are important to understand risks and properly allocate security resources for an architecture. The secure cloud business flows and security capabilities are arranged into a logical architecture. business use cases flow through the green architecture icons with the required blue security capabilities. Learn industry best practices, get real world insights and see expert recommendations for cloud security architecture. Cloud security architecture is the umbrella term used to describe all hardware, software and infrastructure that protects the cloud environment and its components, such as data, workloads, containers, virtual machines and apis.
/filters:no_upscale()/articles/cloud-security-architecture-intro/en/resources/fig 4.jpg)
Introduction To Cloud Security Architecture From A Cloud Consumer S Secure cloud architecture owasp cheat sheet series free download as pdf file (.pdf), text file (.txt) or read online for free. risk analysis, threat modeling, and attack surface assessments are important to understand risks and properly allocate security resources for an architecture. The secure cloud business flows and security capabilities are arranged into a logical architecture. business use cases flow through the green architecture icons with the required blue security capabilities. Learn industry best practices, get real world insights and see expert recommendations for cloud security architecture. Cloud security architecture is the umbrella term used to describe all hardware, software and infrastructure that protects the cloud environment and its components, such as data, workloads, containers, virtual machines and apis.
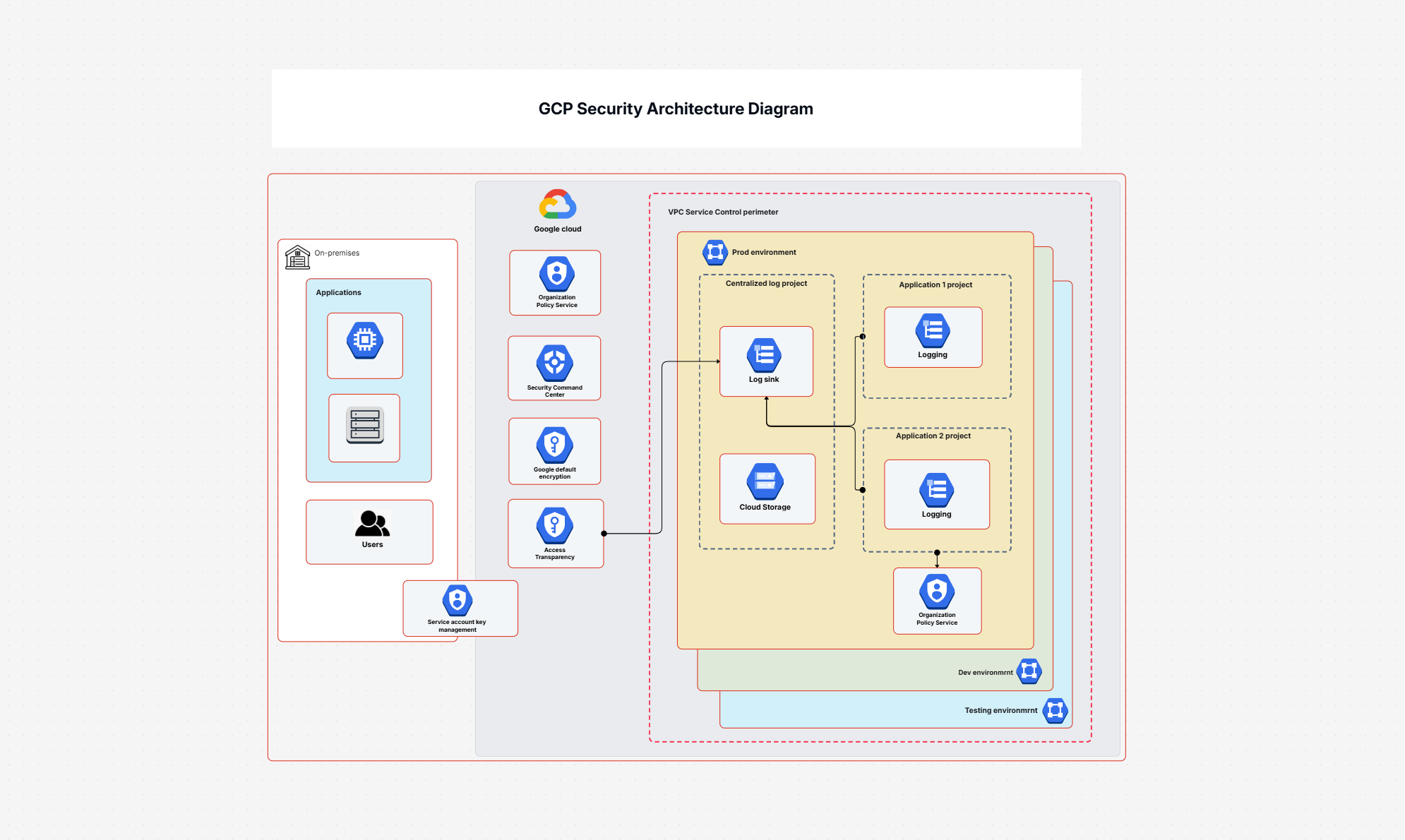
Security Architecture Diagram For Cloud Potential Unlocking Learn industry best practices, get real world insights and see expert recommendations for cloud security architecture. Cloud security architecture is the umbrella term used to describe all hardware, software and infrastructure that protects the cloud environment and its components, such as data, workloads, containers, virtual machines and apis.
Security Architecture Diagram For Cloud Potential Unlocking
Comments are closed.