Security Architecture All Cyber One

Security Architecture All Cyber One At allcyberone we follow a top down approach—start by looking at the business goals, objectives and vision. identify all the risk associated with the attributes that can prevent a business from achieving its goals. Explores the key components of a cyber security architecture and best practices to fortify your organization against modern threats.
What Is Cyber Security Architecture Component Implementation Security architecture is a strategy for designing and building a company's security infrastructure. troubleshoots data protection issues by analyzing processes, controls and systems. this multifaceted strategy has many elements such as security policy, risk management, and determination of controls and procedures. Cybersecurity architecture is the strategic design of all security components of an organization’s it infrastructure. this includes but is not limited to the operational design of systems that govern people, processes, products, functions, services, tools, technologies, policies, and procedures. This course is designed for anyone interested in gaining a solid understanding of cybersecurity. it covers fundamental topics such as the five security principles, the cia triad, identity and access management (iam), endpoint security, and key security domains. What cybersecurity architecture is, why it matters, and how it protects systems, networks, and data from modern cyber threats.
All Cyber One This course is designed for anyone interested in gaining a solid understanding of cybersecurity. it covers fundamental topics such as the five security principles, the cia triad, identity and access management (iam), endpoint security, and key security domains. What cybersecurity architecture is, why it matters, and how it protects systems, networks, and data from modern cyber threats. Security architecture is the strategic design of systems, policies and technologies to protect it and business assets from cyberthreats. a well designed security architecture aligns cybersecurity with the unique business goals and risk management profile of the organization. Security architecture is the structured design of security mechanisms, controls, and frameworks that protect an organization’s information assets. its purpose is to ensure that cybersecurity objectives are systematically embedded into people, processes, and technology. Cyberone’s security architecture and design service gives you a network foundation that’s built to defend, adapt, and scale. whether you’re deploying a new environment or rethinking an existing one, we create architecture strategies that align with your business goals and threat landscape. Effective security architecture incorporates key components such as: confidentiality, integrity, availability, authentication, authorisation, auditing and logging, network security, application security, incident response, and security governance.
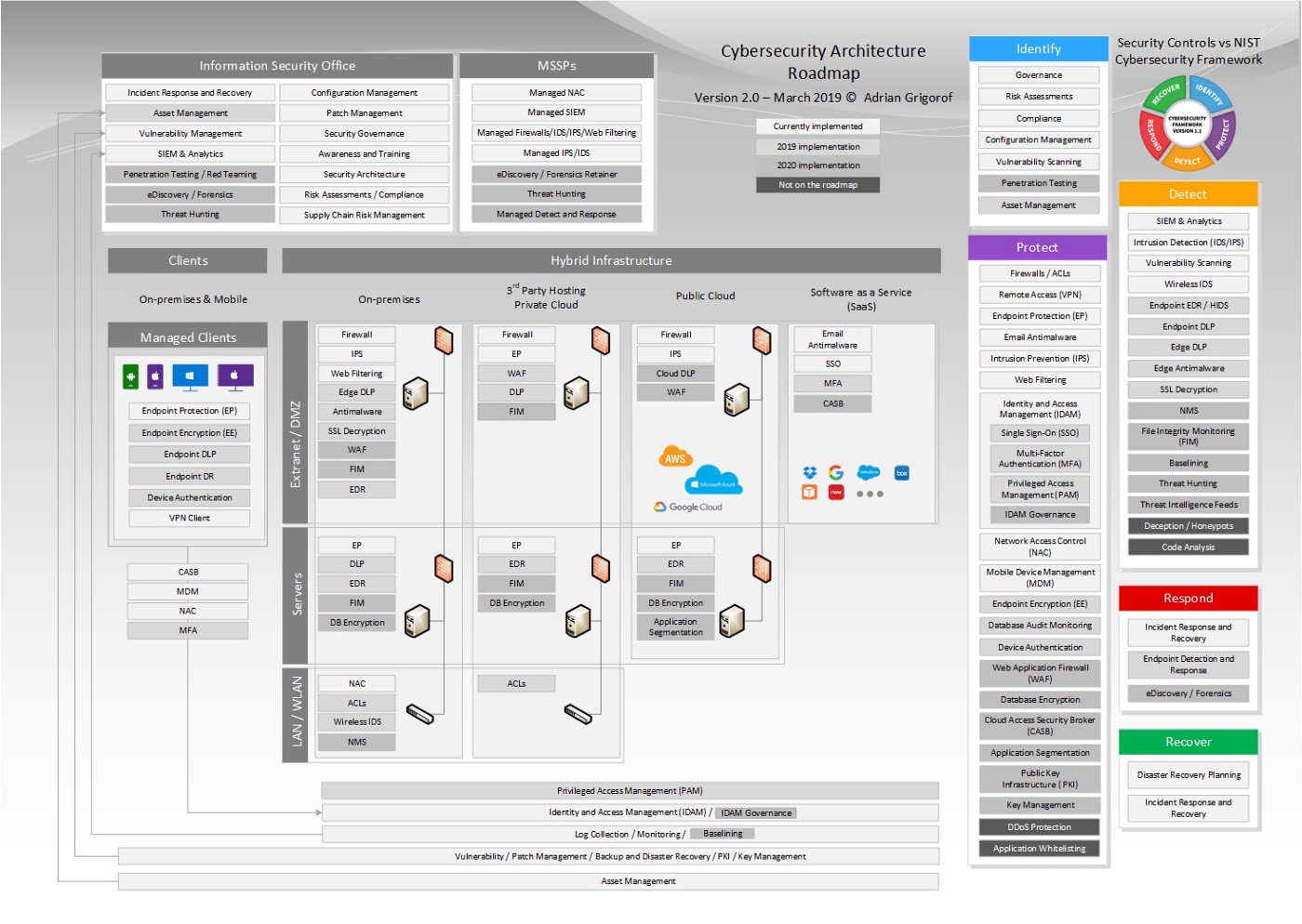
Cybersecurity Architecture Roadmap Managed Sentinel Security architecture is the strategic design of systems, policies and technologies to protect it and business assets from cyberthreats. a well designed security architecture aligns cybersecurity with the unique business goals and risk management profile of the organization. Security architecture is the structured design of security mechanisms, controls, and frameworks that protect an organization’s information assets. its purpose is to ensure that cybersecurity objectives are systematically embedded into people, processes, and technology. Cyberone’s security architecture and design service gives you a network foundation that’s built to defend, adapt, and scale. whether you’re deploying a new environment or rethinking an existing one, we create architecture strategies that align with your business goals and threat landscape. Effective security architecture incorporates key components such as: confidentiality, integrity, availability, authentication, authorisation, auditing and logging, network security, application security, incident response, and security governance.

Cyber Security Architecture Building Digital Fortresses Cyberone’s security architecture and design service gives you a network foundation that’s built to defend, adapt, and scale. whether you’re deploying a new environment or rethinking an existing one, we create architecture strategies that align with your business goals and threat landscape. Effective security architecture incorporates key components such as: confidentiality, integrity, availability, authentication, authorisation, auditing and logging, network security, application security, incident response, and security governance.
Comments are closed.