Security Admin With Microsoft Office 365 Grok

Security Admin With Microsoft Office 365 Grok Microsoft’s office 365 security strategy is based on four pillars. the first pillar–prevent breach, takes care of network level isolation breach borders, distributed denial of service (ddos) detection and mitigation, live site penetration testing, and multifactor authentication for service access. Learn how to set up and protect your administrator accounts in microsoft 365 business basic, microsoft 365 business standard, and microsoft 365 business premium.

Ensure The Security Of Microsoft 365 Admin Accounts R Office365 Yes, xai (grok) integrates with microsoft office 365 (copilot) in real time using albato's flexible trigger system. this system supports two types of triggers: webhook triggers and api triggers. Learn to create dedicated microsoft 365 admin accounts, set up emergency break glass accounts, and apply best practices like mfa and monitoring to ensure security and compliance. Learn to secure microsoft 365 global admin accounts with an 8 step framework to minimize risks and enhance protection against potential attacks. Microsoft’s office 365 security strategy is based on four pillars. the first pillar–prevent breach, takes care of network level isolation breach borders, distributed denial of service (ddos) detection and mitigation, live site penetration testing, and multifactor authentication for service access.
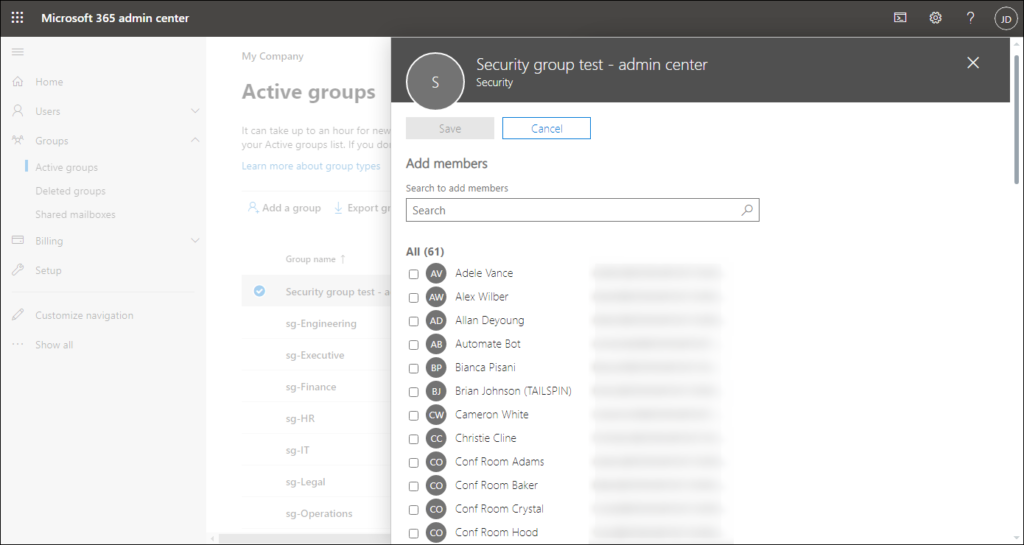
Office 365 Security Groups Learn How To Manage Them Learn to secure microsoft 365 global admin accounts with an 8 step framework to minimize risks and enhance protection against potential attacks. Microsoft’s office 365 security strategy is based on four pillars. the first pillar–prevent breach, takes care of network level isolation breach borders, distributed denial of service (ddos) detection and mitigation, live site penetration testing, and multifactor authentication for service access. After you finish setting up your microsoft 365 for business organization, you need to review and configure the security settings. you can organize the security settings in microsoft 365 for business into the following categories: account security. email and collaboration security. device security. Learn best practices to protect your data using microsoft 365 business basic, standard, or premium. protect devices, email, files, and accounts. This module examines the various features provided in the microsoft 365 ecosystem for securing user access, such as conditional access policies, multifactor authentication, self service password management, smart lockout policies, and security defaults. Although your organization includes a default level of protection for email and collaboration from the moment you create it, the steps in this article give you an actionable plan to unleash the full protection capabilities of microsoft 365.
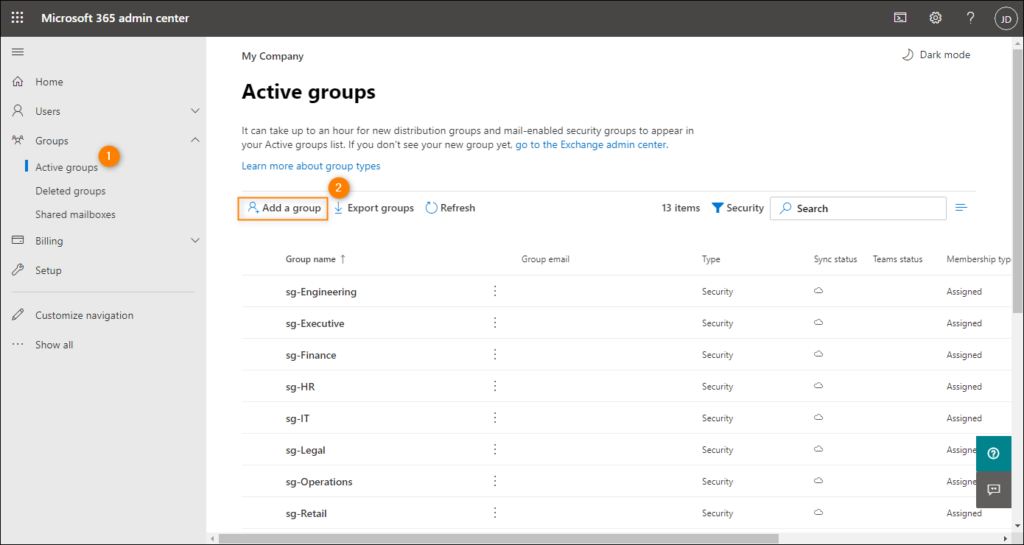
Office 365 Security Groups Learn How To Manage Them After you finish setting up your microsoft 365 for business organization, you need to review and configure the security settings. you can organize the security settings in microsoft 365 for business into the following categories: account security. email and collaboration security. device security. Learn best practices to protect your data using microsoft 365 business basic, standard, or premium. protect devices, email, files, and accounts. This module examines the various features provided in the microsoft 365 ecosystem for securing user access, such as conditional access policies, multifactor authentication, self service password management, smart lockout policies, and security defaults. Although your organization includes a default level of protection for email and collaboration from the moment you create it, the steps in this article give you an actionable plan to unleash the full protection capabilities of microsoft 365.

How To Boost Your Microsoft 365 Security With Office Protect This module examines the various features provided in the microsoft 365 ecosystem for securing user access, such as conditional access policies, multifactor authentication, self service password management, smart lockout policies, and security defaults. Although your organization includes a default level of protection for email and collaboration from the moment you create it, the steps in this article give you an actionable plan to unleash the full protection capabilities of microsoft 365.

Microsoft Office 365 Security Best Practices
Comments are closed.