Security 1 2 Mac Spoofing
Mac Address Spoofing Technocate Is an invisible intruder bypassing your firewall? learn how to detect mac address spoofing using wireshark, python, and enterprise switch logs. Learn what mac spoofing is, how attackers use it, and how to prevent it. this 2025 guide covers detection tools, real world risks, and expert prevention techniques for businesses and individuals.
Mac Address Spoofing Technocate This study addresses the critical cybersecurity challenges faced by small and mediumsized businesses (smbs) in protecting their local area networks (lans) against evolving mac address. Learn what mac spoofing is, how attackers fake device identities, risks to networks, detection methods, and best ways to prevent mac address spoofing. This article delves into the concepts of layer 2 attacks, specifically arp poisoning, mac flooding, and mac address cloning. additionally, we will explore mitigation strategies to enhance network security. Media access control (mac) address spoofing is a fundamental technique in both offensive security operations and defensive network hardening.
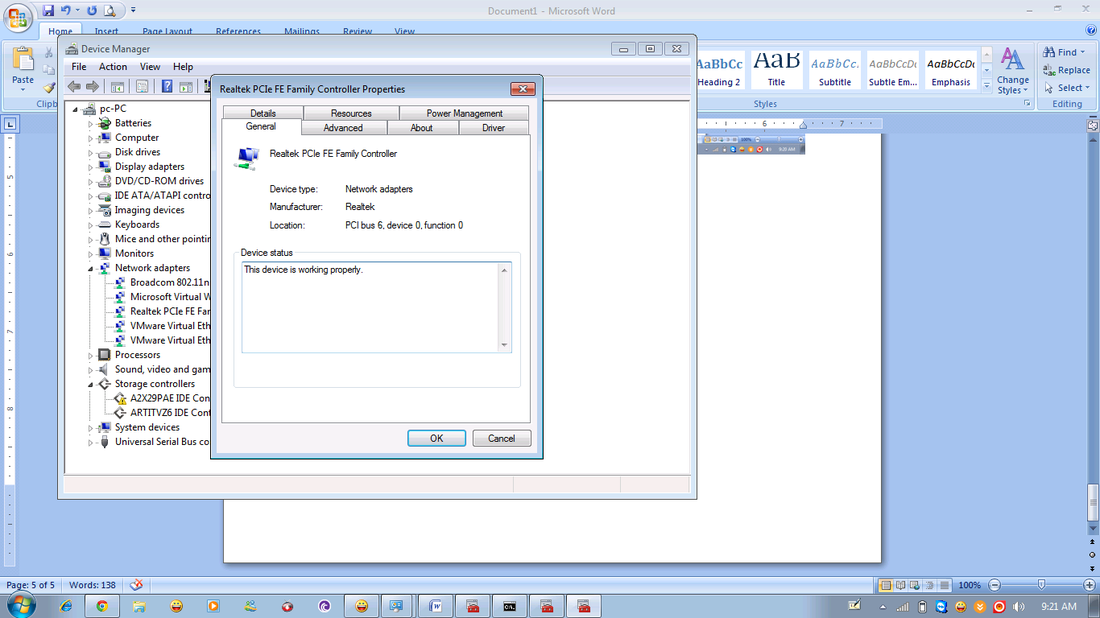
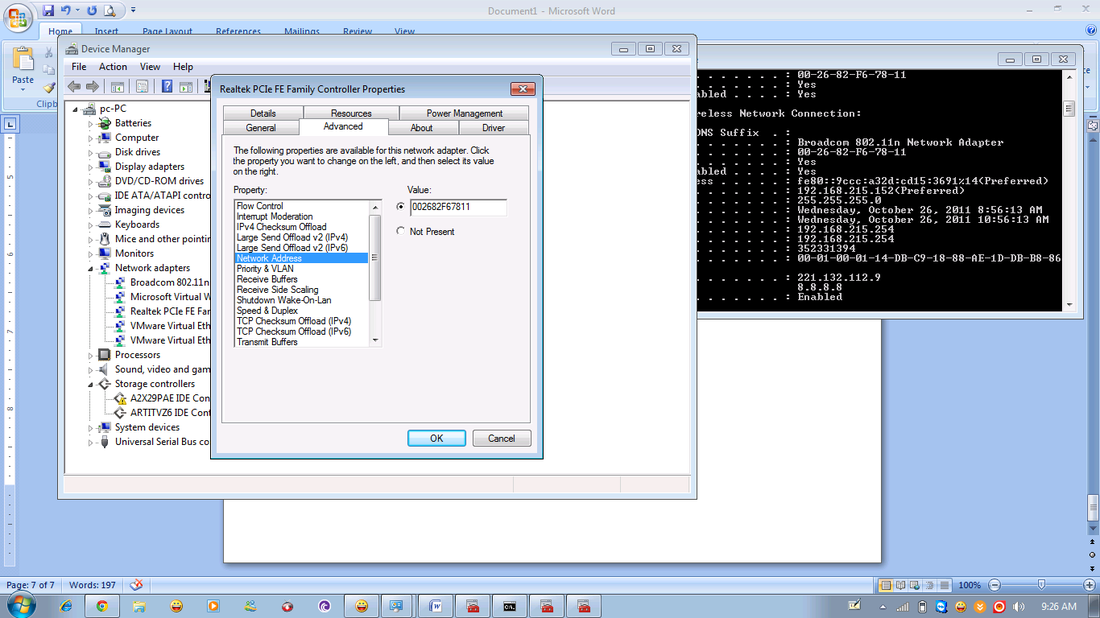
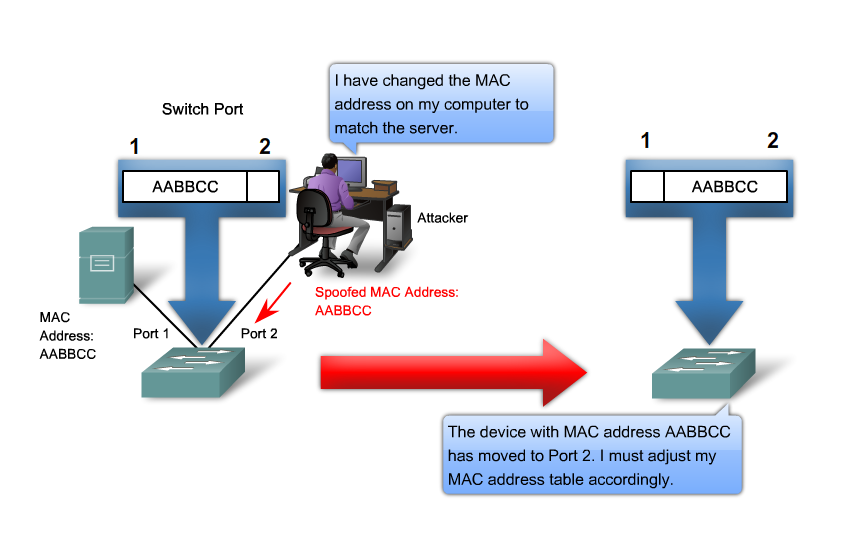
Mac Address Spoofing Technocate This article delves into the concepts of layer 2 attacks, specifically arp poisoning, mac flooding, and mac address cloning. additionally, we will explore mitigation strategies to enhance network security. Media access control (mac) address spoofing is a fundamental technique in both offensive security operations and defensive network hardening. What is mac spoofing, and how does it affect wi fi security? mac spoofing is when an attacker tricks a network by faking a device’s unique id (mac address) to gain unauthorized access or disrupt communication. A mac spoofing attack is when an attacker intentionally changes their device’s mac address to mimic your device’s mac address and redirect the data sent to your device to another one. Mac spoofing is a technique used to change a device's mac address. this practice, called mac spoofing, can affect network security and management. whether used for network troubleshooting or potential network breaches, this concept has implications for network security and management. Mac spoofing refers to the practice of changing or faking the mac address of a device to make it appear as if it belongs to another device. this is done using specialized software or command line tools that modify the mac address stored on the device’s network interface card.
Mac Address Spoofing Technocate What is mac spoofing, and how does it affect wi fi security? mac spoofing is when an attacker tricks a network by faking a device’s unique id (mac address) to gain unauthorized access or disrupt communication. A mac spoofing attack is when an attacker intentionally changes their device’s mac address to mimic your device’s mac address and redirect the data sent to your device to another one. Mac spoofing is a technique used to change a device's mac address. this practice, called mac spoofing, can affect network security and management. whether used for network troubleshooting or potential network breaches, this concept has implications for network security and management. Mac spoofing refers to the practice of changing or faking the mac address of a device to make it appear as if it belongs to another device. this is done using specialized software or command line tools that modify the mac address stored on the device’s network interface card.
Mac Address Spoofing Technocate Mac spoofing is a technique used to change a device's mac address. this practice, called mac spoofing, can affect network security and management. whether used for network troubleshooting or potential network breaches, this concept has implications for network security and management. Mac spoofing refers to the practice of changing or faking the mac address of a device to make it appear as if it belongs to another device. this is done using specialized software or command line tools that modify the mac address stored on the device’s network interface card.
Comments are closed.