Securing Your Restful Api A Guide To Authentication Methods Peerdh

Securing Your Restful Api A Guide To Authentication Methods Peerdh In the world of web development, securing your restful api is crucial. with the rise of data breaches and cyber threats, understanding how to implement robust authentication methods is more important than ever. this article will walk you through various authentication techniques, their pros and cons, and how to impleme. This protects authentication credentials in transit, for example passwords, api keys or json web tokens. it also allows clients to authenticate the service and guarantees integrity of the transmitted data.
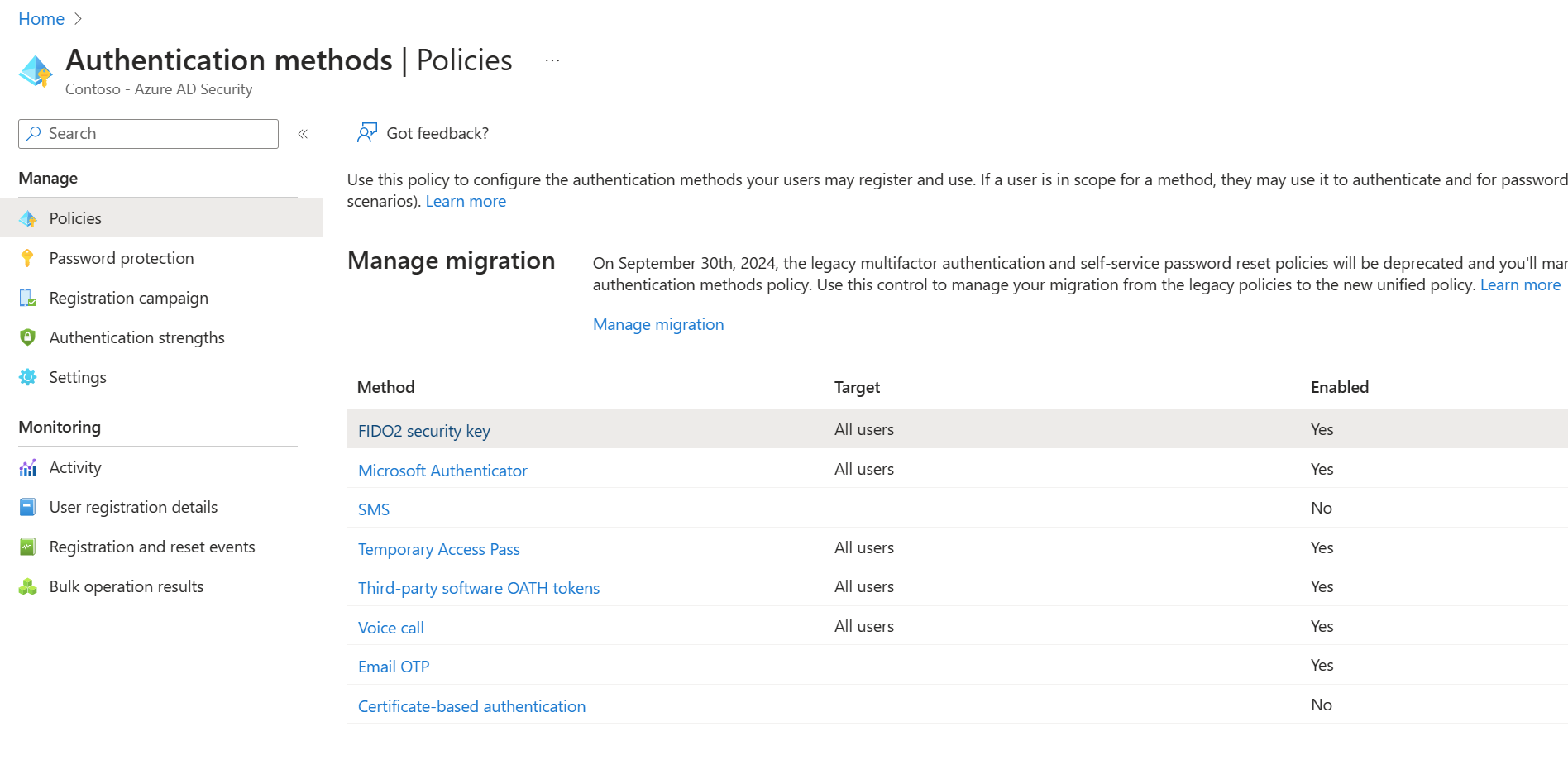
Api Authentication Methods Peerdh This article explores the various authentication schemes available for rest apis, from basic authentication methods to advanced token based approaches like oauth 2.0 and jwt. Having built authentication systems that protect millions of user accounts, i've seen firsthand how proper authentication can make or break an application's security posture. let's dive into the four fundamental rest api authentication methods every developer should master. Explore various authentication methods for rest apis. learn about api keys, oauth 2.0, jwt, and more to ensure the security of your web services. With the rise of data breaches and cyber threats, understanding how to implement robust authentication methods is crucial. this article will guide you through various authentication techniques that can help safeguard your api, ensuring that only authorized users can access your resources.
Rest Api Authentication Download Free Pdf Hypertext Transfer Explore various authentication methods for rest apis. learn about api keys, oauth 2.0, jwt, and more to ensure the security of your web services. With the rise of data breaches and cyber threats, understanding how to implement robust authentication methods is crucial. this article will guide you through various authentication techniques that can help safeguard your api, ensuring that only authorized users can access your resources. A well secured api protects sensitive data and ensures that only authorized users can access specific resources. this guide will cover various aspects of rest api security, including authentication, authorization, data validation, and best practices. This article will guide you through the best practices for securing your restful api, focusing on authentication, authorization, and other essential security measures. In the world of web development, securing your restful api is a top priority. with the increasing number of cyber threats, implementing robust authentication methods is crucial. this article will guide you through various authentication techniques, helping you choose the right one for your api. With the rise of cyber threats, protecting your api from unauthorized access and data breaches is more important than ever. this article will guide you through the best practices for securing your restful api.
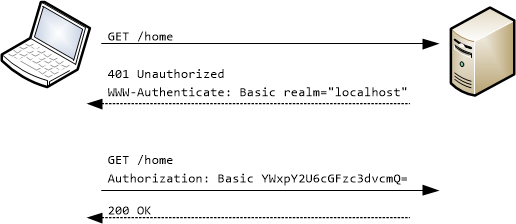
Restful Api Authentication Basics A well secured api protects sensitive data and ensures that only authorized users can access specific resources. this guide will cover various aspects of rest api security, including authentication, authorization, data validation, and best practices. This article will guide you through the best practices for securing your restful api, focusing on authentication, authorization, and other essential security measures. In the world of web development, securing your restful api is a top priority. with the increasing number of cyber threats, implementing robust authentication methods is crucial. this article will guide you through various authentication techniques, helping you choose the right one for your api. With the rise of cyber threats, protecting your api from unauthorized access and data breaches is more important than ever. this article will guide you through the best practices for securing your restful api.
Comments are closed.