Securing Your Open Source Dependency Chain
What Is Software Supply Chain Security Anchore A guide to software supply chain security, explaining how to find and mitigate vulnerabilities in your open source dependencies using software composition analysis (sca). Recent attacks on open source focus on exfiltrating secrets; here are the prevention steps you can take today, plus a look at the security capabilities github is working on.

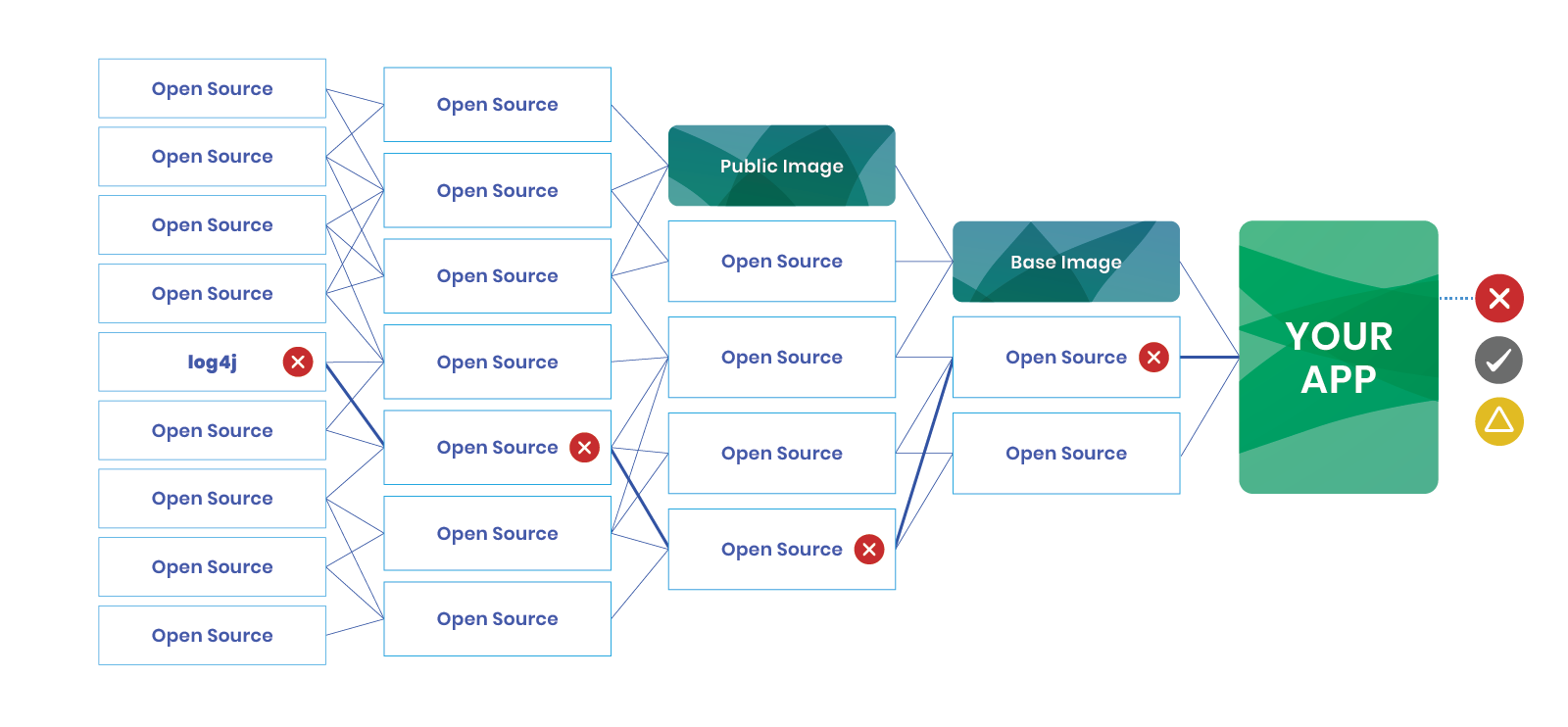
Securing Your Open Source Dependency Chain Aiven Understanding the security risks within the open source ecosystem, from supply chain attacks to protestware, and the tools and methods to mitigate them. Discover the two simple steps you can take to secure your open source dependency chain. open source software (oss) has become the backbone of modern software development, empowering developers with a vast ecosystem of freely available libraries, frameworks and tools. Read our easy to follow guide to help secure the open source packages commonly deployed in application development. checkmarx helps secure dependencies, detect hidden risks, and safeguard your software development lifecycle (sdlc). Learn how to defend against software supply chain threats, including log4j and dependency vulnerabilities.

Semgrep Securing Your Open Source Dependencies With Semgrep Supply Read our easy to follow guide to help secure the open source packages commonly deployed in application development. checkmarx helps secure dependencies, detect hidden risks, and safeguard your software development lifecycle (sdlc). Learn how to defend against software supply chain threats, including log4j and dependency vulnerabilities. Securing open source dependencies isn’t a one time fix — it’s a culture of vigilance. organizations can mitigate risks by combining structured triage, automation, and collaborative. The objective of the supply chain integrity working group (wg) is to provide a global community for collaborating to help individuals and organizations assess and improve the security of end to end supply chains for open source software. The landscape of open source software supply chains presents distinct vulnerabilities. discover effective strategies to pinpoint and alleviate these dangers. With supply chain attacks on the rise, securing your source code is critical. learn essential best practices for scm security, secrets management, and open source safety.
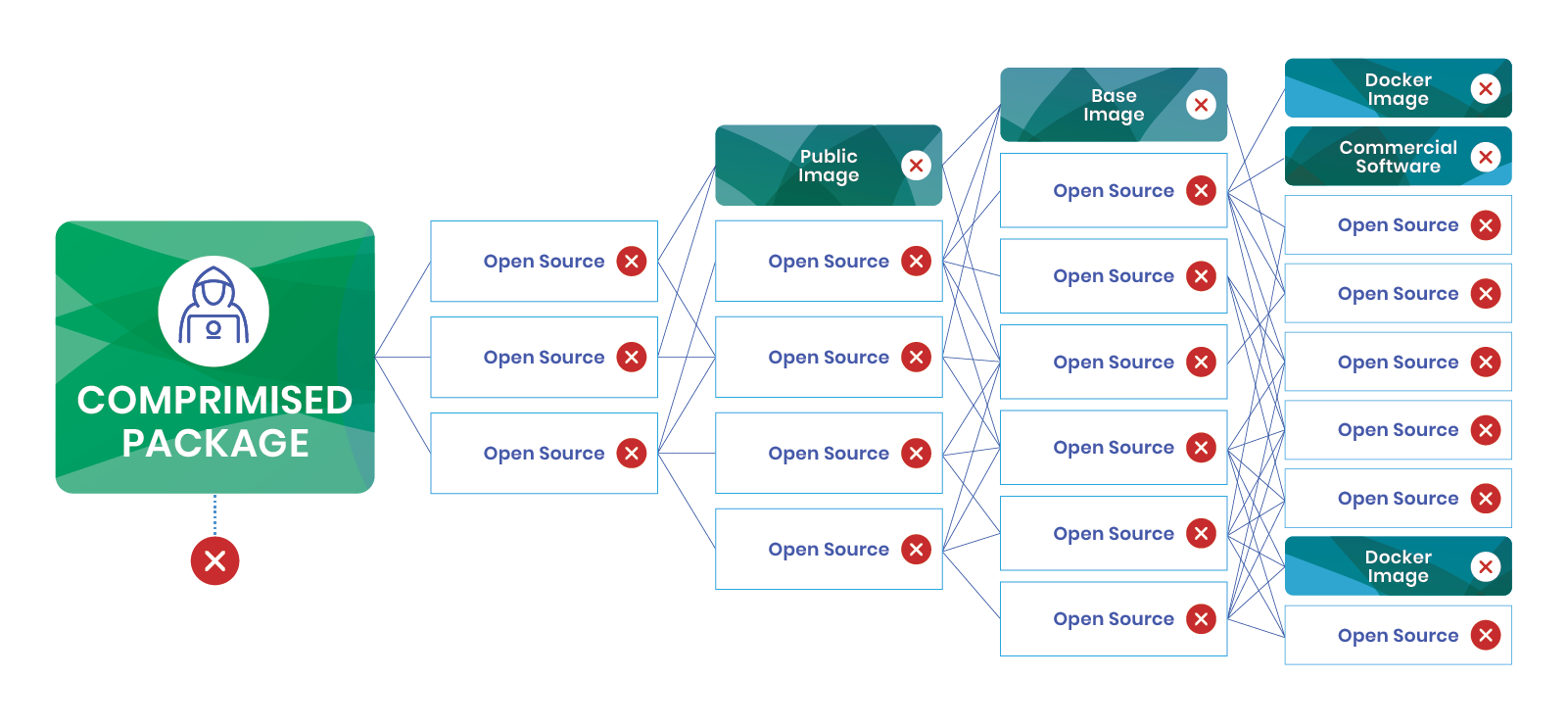
What Is Software Supply Chain Security Anchore Securing open source dependencies isn’t a one time fix — it’s a culture of vigilance. organizations can mitigate risks by combining structured triage, automation, and collaborative. The objective of the supply chain integrity working group (wg) is to provide a global community for collaborating to help individuals and organizations assess and improve the security of end to end supply chains for open source software. The landscape of open source software supply chains presents distinct vulnerabilities. discover effective strategies to pinpoint and alleviate these dangers. With supply chain attacks on the rise, securing your source code is critical. learn essential best practices for scm security, secrets management, and open source safety.

The Challenges Of Securing The Open Source Supply Chain The New Stack The landscape of open source software supply chains presents distinct vulnerabilities. discover effective strategies to pinpoint and alleviate these dangers. With supply chain attacks on the rise, securing your source code is critical. learn essential best practices for scm security, secrets management, and open source safety.
Comments are closed.