Securing Your Ci Cd Pipeline Exploring The Dangers Of Self Hosted Runners
Securing Your Ci Cd Pipeline Exploring The Dangers Of Self Hosted Overall, self hosting ci cd pipelines can be risky if not properly managed. to minimize the potential dangers, it's essential to follow security best practices, such as regularly updating self hosted agents, implementing access controls, and monitoring for suspicious activity. Overall, self hosting ci cd pipelines can be risky if not properly managed. to minimize the potential dangers, it’s essential to follow security best practices, such as regularly updating self hosted agents, implementing access controls, and monitoring for suspicious activity.
Securing Your Ci Cd Pipeline Exploring The Dangers Of Self Hosted Runners Overall, self hosting ci cd pipelines can be risky if not properly managed. to minimize the potential dangers, its essential to follow security best practices, such as regularly updating self hosted agents, implementing access controls, and monitoring for suspicious activity. A gitlab ci cd pipeline is a workflow automation engine used for simple or complex devops automation tasks. because these pipelines enable a remote code execution service, you should implement the following process to reduce security risks:. Choosing, configuring, and securing your runners is arguably the most critical operational decision in your ci cd strategy. a poor choice can lead to prohibitive costs, security. One emerging trend in ci cd is the use of self hosted runners. while these tools offer custom hardware configurations and can be hosted in various environments, they can also pose.

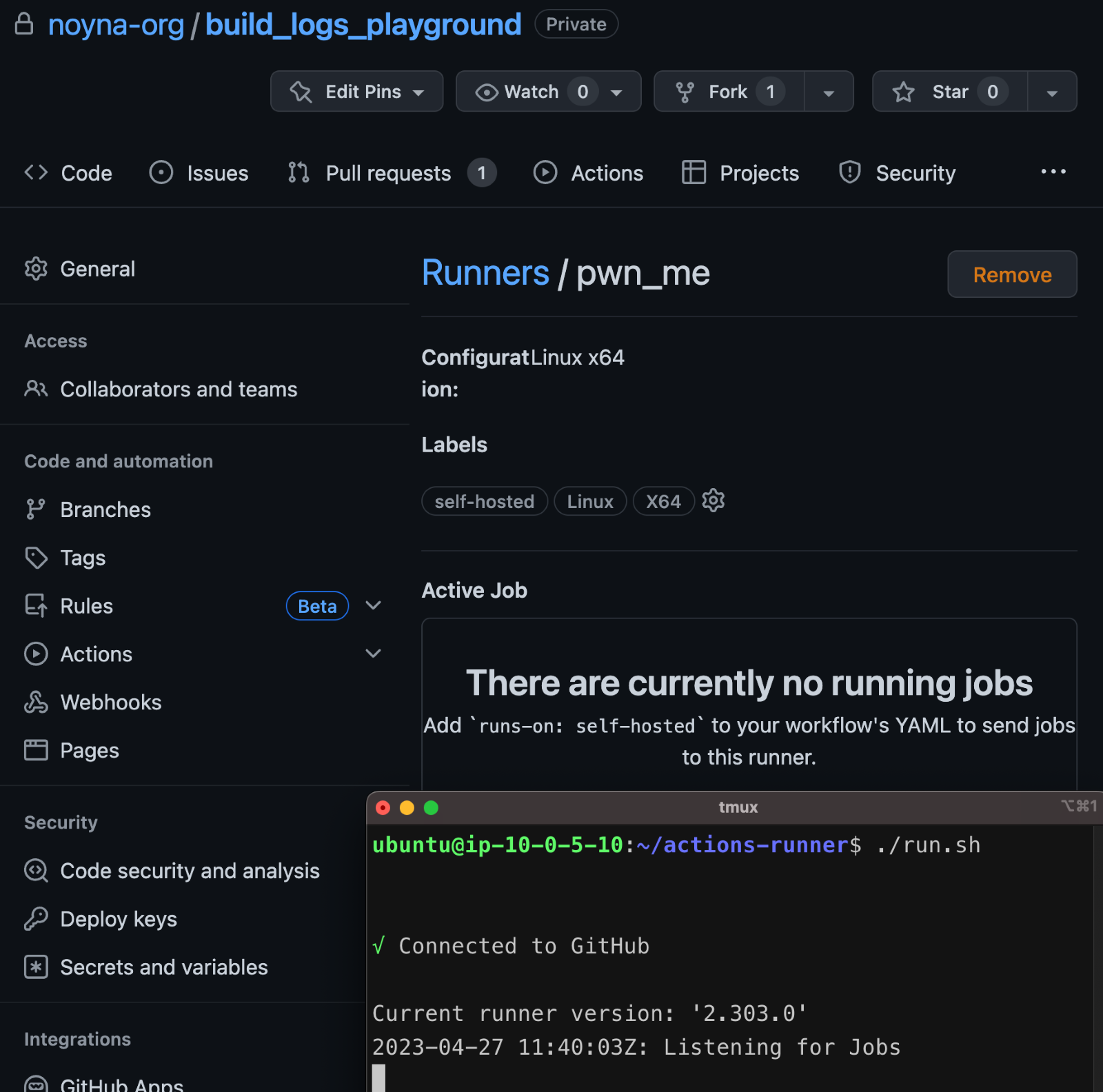
Securing Your Ci Cd Pipeline Exploring The Dangers Of Self Hosted Runners Choosing, configuring, and securing your runners is arguably the most critical operational decision in your ci cd strategy. a poor choice can lead to prohibitive costs, security. One emerging trend in ci cd is the use of self hosted runners. while these tools offer custom hardware configurations and can be hosted in various environments, they can also pose. As the name suggests, github manages the github hosted runners, but of particular interest to attackers are self hosted runners, which developers manage. self hosted runners reside on internal networks, bypassing the firewalls and network access controls that usually prevent unauthorized access. Learn about ci cd pipeline security best practices to protect your software lifecycle from vulnerabilities and attacks while maintaining development velocity. Security in ci cd pipelines is a pressing issue. read our blog to understand the pitfalls of self hosted agents and how you can take steps to secure your software development. Here's what attackers look for: overly permissive service accounts, secrets stored in plaintext within pipeline configurations, and self hosted runners with network access to internal systems.
-1.jpg)
Securing Your Ci Cd Pipeline Exploring The Dangers Of Self Hosted Runners As the name suggests, github manages the github hosted runners, but of particular interest to attackers are self hosted runners, which developers manage. self hosted runners reside on internal networks, bypassing the firewalls and network access controls that usually prevent unauthorized access. Learn about ci cd pipeline security best practices to protect your software lifecycle from vulnerabilities and attacks while maintaining development velocity. Security in ci cd pipelines is a pressing issue. read our blog to understand the pitfalls of self hosted agents and how you can take steps to secure your software development. Here's what attackers look for: overly permissive service accounts, secrets stored in plaintext within pipeline configurations, and self hosted runners with network access to internal systems.
Comments are closed.