Securing The Ci Cd Pipeline

Securing The Ci Cd Pipeline Best Practices For Devsecops By Sai Sravan Incorporating security into your ci cd pipeline is essential for ensuring that your software remains resilient against emerging threats. by embedding security measures throughout the development life cycle, you can identify and mitigate vulnerabilities and maintain the integrity of your applications. Learn about ci cd pipeline security best practices to protect your software lifecycle from vulnerabilities and attacks while maintaining development velocity.

8 Tips For Securing Your Ci Cd Pipeline With Snyk Snyk As such, integrity verification is an important method of reducing risk in ci cd environments. as with many other defensive actions, implementation of integrity related controls begins early in the sdlc. as noted earlier, the scm should require commits to be signed before the code can be merged. This comprehensive ci cd pipeline guide covers security integration, devsecops best practices, and automation solutions for faster, secure software delivery. Learn ci cd pipeline security, key risks, and best practices to secure ci cd pipelines effectively. explore devsecops strategies and cloud security integration. This comprehensive guide will explain why ci cd pipeline security is mission critical and provide a detailed, actionable framework of best practices to protect your pipelines from evolving cyber threats in 2026.

8 Tips For Securing Your Ci Cd Pipeline With Snyk Snyk Learn ci cd pipeline security, key risks, and best practices to secure ci cd pipelines effectively. explore devsecops strategies and cloud security integration. This comprehensive guide will explain why ci cd pipeline security is mission critical and provide a detailed, actionable framework of best practices to protect your pipelines from evolving cyber threats in 2026. A comprehensive approach to ci cd security involves implementing security controls at every stage of the pipeline, from code development through deployment and monitoring. this technical guide explores essential security practices, tools, and implementation strategies for building robust and secure devops pipelines. Learn why ci cd security is the key to faster and more reliable software delivery with tips on how to keep your pipelines secure. We used a combination of tools and techniques to integrate security seamlessly into our ci cd pipeline, ensuring the project is secure while maintaining the speed and agility of devops. This section examines 20 key ci cd pipeline security best practices that strengthen security in every pipeline stage for maintaining integrity from code development through deployment.
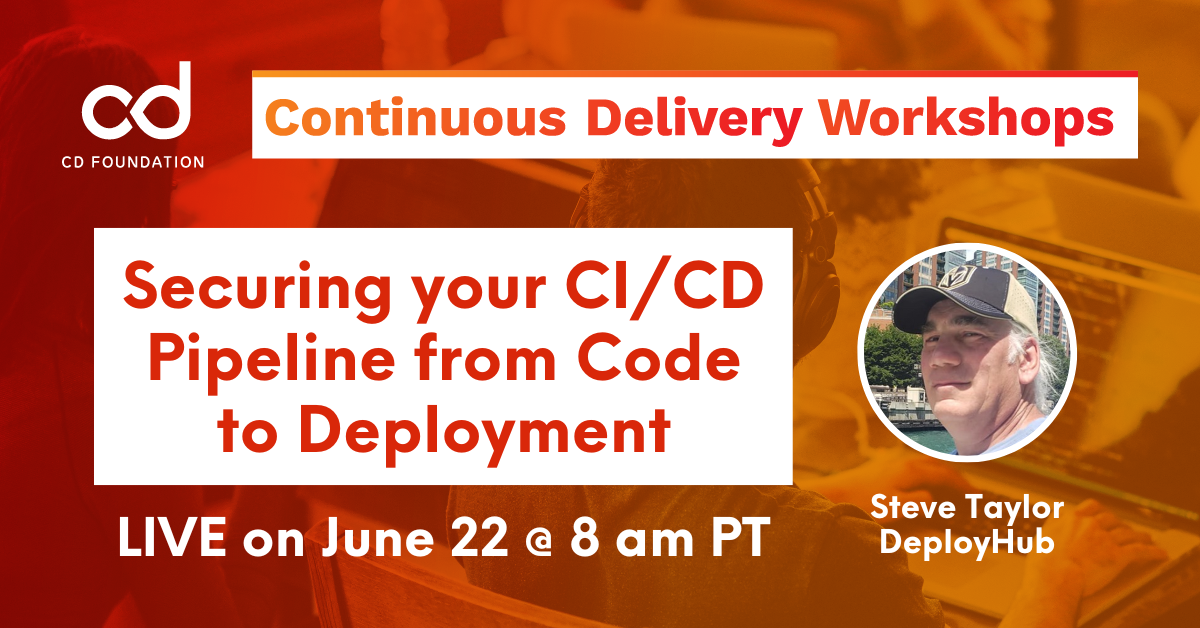
Cdf Workshop Securing Your Ci Cd Pipeline From Code To Deployment Cd A comprehensive approach to ci cd security involves implementing security controls at every stage of the pipeline, from code development through deployment and monitoring. this technical guide explores essential security practices, tools, and implementation strategies for building robust and secure devops pipelines. Learn why ci cd security is the key to faster and more reliable software delivery with tips on how to keep your pipelines secure. We used a combination of tools and techniques to integrate security seamlessly into our ci cd pipeline, ensuring the project is secure while maintaining the speed and agility of devops. This section examines 20 key ci cd pipeline security best practices that strengthen security in every pipeline stage for maintaining integrity from code development through deployment.
Comments are closed.