Securing Ldap With A Self Signed Certificate

Export And Install An Ldap Self Signed Certificate On An Iis Server Learn how to configure ldaps in active directory using a self signed certificate. step by step guide to secure your domain with ssl tls encryption. This example creats a self signed certificate. it makes use of the the subject alternative names (san) feature of certificates which enable one cert to work with multiple named hosts.

Enable Encryption For Ldap B Add A Self Signed Ldap Certificate To This article shows you how to create, install, and verify ssl certificates for ldaps on domain controllers using either microsoft certification authorities or third party certificate providers. To enable ldap over ssl (ldaps) all you need to do is "install" an ssl certificate on the active directory server. most enterprises will opt to purchase an ssl certificate from a 3rd party like verisign. While testing active directory on a closed private network, i needed ldaps connections to the domain controllers. but i didn't have any pki certificate servers on the network and i didn't want to build one. This guide walks through generating a private certificate authority, issuing a server certificate with subject alternative names (san), configuring slapd for both starttls (port 389) and ldaps (port 636), and setting up a client machine to trust the ca and query over encrypted connections.
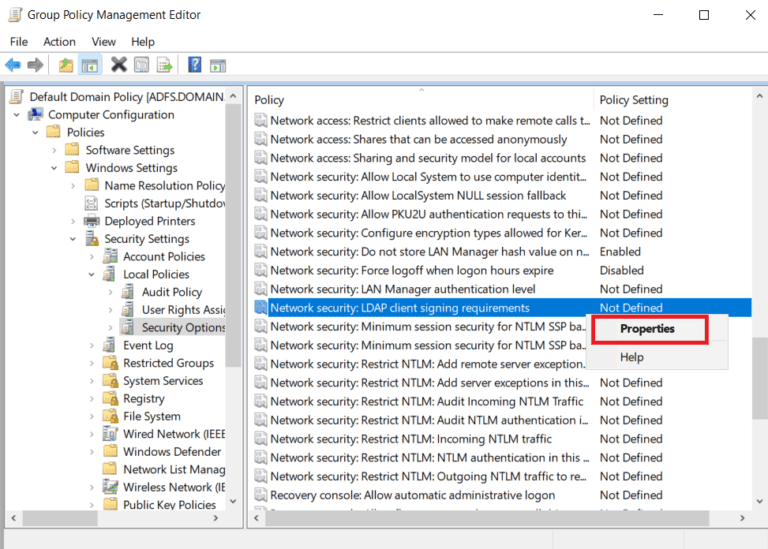
Securing Ldap Communications In Active Directory While testing active directory on a closed private network, i needed ldaps connections to the domain controllers. but i didn't have any pki certificate servers on the network and i didn't want to build one. This guide walks through generating a private certificate authority, issuing a server certificate with subject alternative names (san), configuring slapd for both starttls (port 389) and ldaps (port 636), and setting up a client machine to trust the ca and query over encrypted connections. Microsoft active directory servers by default provide ldap connections over unencrypted connections (boo!). the steps below will create a new self signed certificate appropriate for use with and thus enabling ldaps for an ad server. Here is how to do it. you need to run all of these commands in an elevated powershell prompt. the certificate will immediately start being used by ad ds; you don't need to restart services or reboot the machine. ad ds uses the standard ldaps port (636). Starttls is an alternative approach that is now the preferred method of encrypting an ldap connection. for those that stumble across this, php7.1 now allows you to set the ca file and ca directory via ldap set option() rather than having to update a server configuration file. To connect to an ldaps server using a self signed certificate, you’ll need to add the certificate to the trusted authorities on your client system (faveo server).
Comments are closed.