Securing It Assets Across Distributed Environments Requires Proactive

Securing It Assets Across Distributed Environments Requires Proactive Discover how zero trust and cyber resilience strategies strengthen distributed it infrastructure against modern threats. Securing it assets across distributed environments requires proactive risk management with continuous discovery, real time assessments, and automated mitigation.

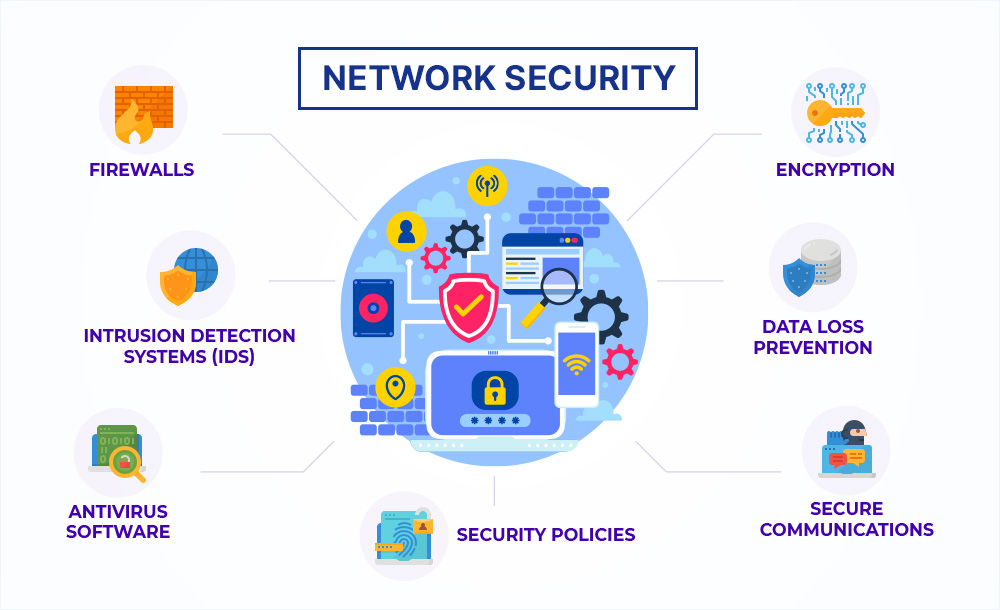
How Managed It Services Provide Proactive Cybersecurity Solutions Securing data across distributed cloud environments requires more than basic firewalls or encryption — it demands a holistic, layered security approach that combines governance, automation, and ai driven visibility. Traditional perimeter based security models can fail, as users and workloads operate across distributed systems in multi cloud and hybrid environments. here, implementing a zero trust security framework can help. This paper examines innovative approaches to securing distributed systems, focusing on cutting edge solutions such as zero trust architecture (zta), artificial intelligence (ai) powered. This security approach enables fast, simple, and secure connections from any device and location to workloads across any it infrastructure in cloud, on premises, and hybrid environments.
Securing Remote Work Environments Strategies For Protecting This paper examines innovative approaches to securing distributed systems, focusing on cutting edge solutions such as zero trust architecture (zta), artificial intelligence (ai) powered. This security approach enables fast, simple, and secure connections from any device and location to workloads across any it infrastructure in cloud, on premises, and hybrid environments. This article provides a leadership blueprint for cisos tasked with securing multi cloud environments, offering strategic frameworks, operational best practices, and forward looking approaches to transform security from a potential constraint into a business enabler. Understanding and implementing robust security measures in these distributed environments is essential for ensuring smooth business operations and safeguarding. edge computing fundamentally changes the security landscape by expanding the attack surface across numerous distributed endpoints. Traditional perimeter security cannot keep up with distributed infrastructure. the reality: multi cloud adoption widens exposure & proactive defense is essential. security is not an afterthought but a core business enabler. Developing an asset inventory is a multi step process where ot owners and operators identify, classify, and document assets. ot owners and operators that develop an ot taxonomy as part of the inventory process can significantly enhance the process.

Safeguarding Your Business Assets With Proactive It Support This article provides a leadership blueprint for cisos tasked with securing multi cloud environments, offering strategic frameworks, operational best practices, and forward looking approaches to transform security from a potential constraint into a business enabler. Understanding and implementing robust security measures in these distributed environments is essential for ensuring smooth business operations and safeguarding. edge computing fundamentally changes the security landscape by expanding the attack surface across numerous distributed endpoints. Traditional perimeter security cannot keep up with distributed infrastructure. the reality: multi cloud adoption widens exposure & proactive defense is essential. security is not an afterthought but a core business enabler. Developing an asset inventory is a multi step process where ot owners and operators identify, classify, and document assets. ot owners and operators that develop an ot taxonomy as part of the inventory process can significantly enhance the process.

Securing It Assets Traditional perimeter security cannot keep up with distributed infrastructure. the reality: multi cloud adoption widens exposure & proactive defense is essential. security is not an afterthought but a core business enabler. Developing an asset inventory is a multi step process where ot owners and operators identify, classify, and document assets. ot owners and operators that develop an ot taxonomy as part of the inventory process can significantly enhance the process.

Securing Your Business Future With Proactive It Management Effiease
Comments are closed.