Securing Cryptographic Keys In An Enterprise Environment

Protect Your Company S Data With Cryptographic Keys In A Pki By following these best practices, you can ensure that your enterprise encryption key management is effective and secure. proper key management is essential for protecting your sensitive data and ensuring that only authorized individuals can access it. Explore top practices for encryption key management to boost security, compliance, and risk management.
Securing Cryptographic Keys Across The Hybrid Multi Cloud Akeyless Learn about the encryption key management best practices that help centralize and protect all operations involving cryptographic keys. This recommendation provides guidance on how organizations should manage cryptographic keys in accordance with the federal key management policies and best practices described in sp 800 57 part 1. These 12 enterprise encryption key management best practices will help save you time, stress and money. Keys are sensitive data's gatekeepers; their mismanagement leads to catastrophic breaches. this guide delves into advanced key management practices for enterprises, exploring key lifecycles, challenges, core principles, and emerging trends to build a resilient security posture.
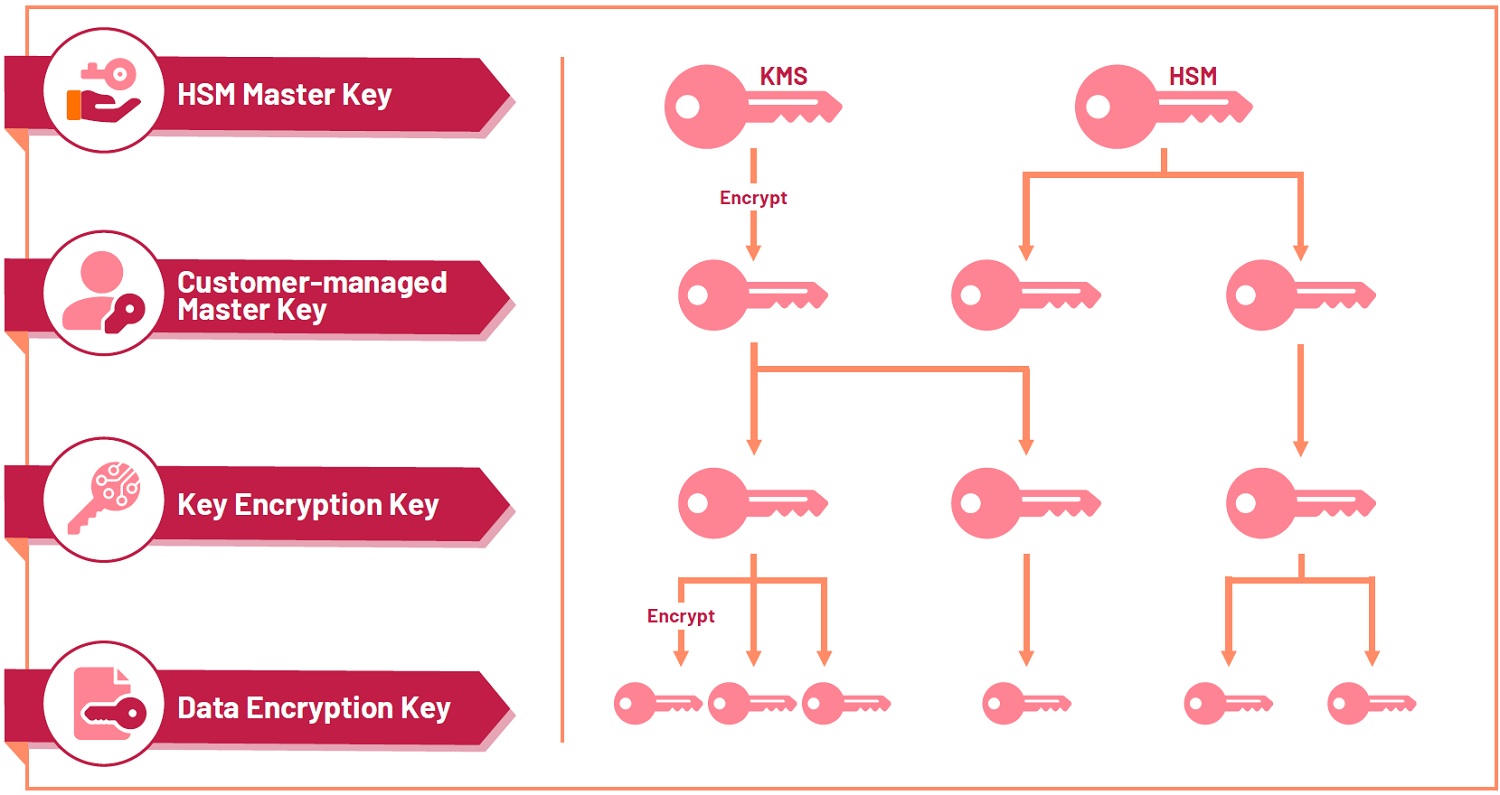
Technologies In Cloud To Protect Cryptographic Keys Singapore These 12 enterprise encryption key management best practices will help save you time, stress and money. Keys are sensitive data's gatekeepers; their mismanagement leads to catastrophic breaches. this guide delves into advanced key management practices for enterprises, exploring key lifecycles, challenges, core principles, and emerging trends to build a resilient security posture. A practical guide to implementing enterprise cryptography and key management, covering algorithm selection, hsms, pki, secrets management, and post quantum cryptography transition. Centralised key management: a unified platform simplifies the management of encryption keys across environments, eliminating silos and enabling consistent policies. This guide has been developed to help organisational personnel in understanding the threat environment and the value of implementing secure keys and secrets management to make better informed decisions. The best enterprise key management strategies secure cryptographic keys through the full key lifecycle (key generation, use, storage, update, archiving, and destruction) as well as control key access to authorized users and machines.
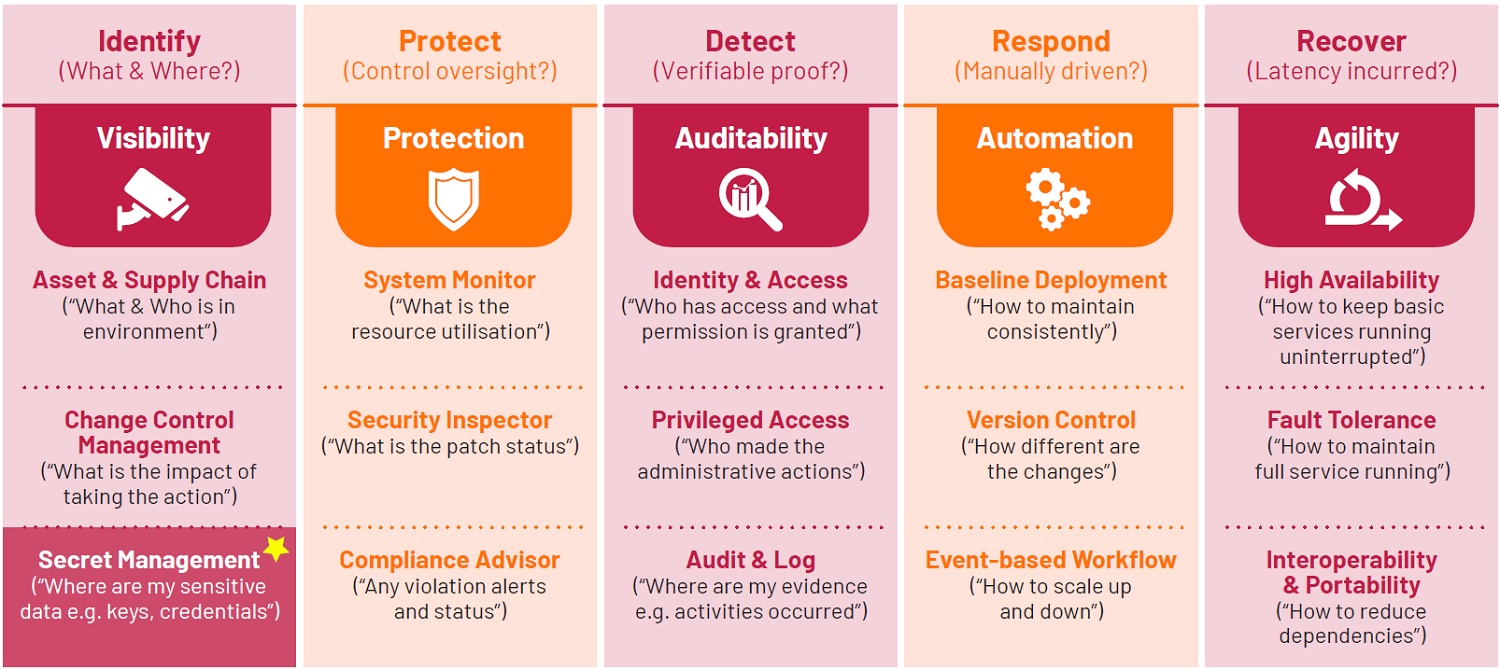
Technologies In Cloud To Protect Cryptographic Keys Singapore A practical guide to implementing enterprise cryptography and key management, covering algorithm selection, hsms, pki, secrets management, and post quantum cryptography transition. Centralised key management: a unified platform simplifies the management of encryption keys across environments, eliminating silos and enabling consistent policies. This guide has been developed to help organisational personnel in understanding the threat environment and the value of implementing secure keys and secrets management to make better informed decisions. The best enterprise key management strategies secure cryptographic keys through the full key lifecycle (key generation, use, storage, update, archiving, and destruction) as well as control key access to authorized users and machines.
Comments are closed.