Securing Apis With Wso2 Api Manager And Okta Wso2 Webinar

Securing Apis With Wso2 Api Manager And Okta Wso2 By attending this webinar, you will gain hands on experience on how wso2 api manager can be leveraged to use okta as a third party key management platform by following a simple setup procedure. 0:00 introduction05:26 apis and api security12:38 importance of api security15:13 wso2 api manager api security16:47 wso2 api manager external key.
Wso2 Api Manager Okta Sso Stackcheats By attending this webinar, you will gain hands on experience on how wso2 api microgateway can be leveraged to use 3rd party key management services to secure your microservices. It is possible to integrate the wso2 api manager with an external identity and access management server (iam) using the okta oauth authorization server to manage the oauth clients and tokens that are required by wso2 api manager. One of the most important aspects of security is ensuring that apis are not publicly accessible. as developers, we cannot afford the risks of unauthorized access, misuse, or data leakage. By attending this webinar, you will gain hands on experience on how wso2 api microgateway can be leveraged to use 3rd party key management services to secure your microservices.
Wso2 Api Manager Okta Sso Stackcheats One of the most important aspects of security is ensuring that apis are not publicly accessible. as developers, we cannot afford the risks of unauthorized access, misuse, or data leakage. By attending this webinar, you will gain hands on experience on how wso2 api microgateway can be leveraged to use 3rd party key management services to secure your microservices. Learn how to secure apis with wso2 api manager. explore features, access control, encryption, and best practices for scalable, compliant api management. In this guide, we explain how to integrate the wso2 api manager with an external identity and access management server (iam) using the okta oauth authorization server to manage the oauth clients and tokens required by wso2 api manager. After the successful creation of our demo application, let’s direct to production keys tab to generate consumer secrets and access tokens using okta third party key manager. These entities allow diverse software programs to interact and distribute data, thus becoming pivotal components of web and mobile apps we use today. the proliferation of api usage necessitates stringent security measures, leading us to explore the solutions provided by wso2.
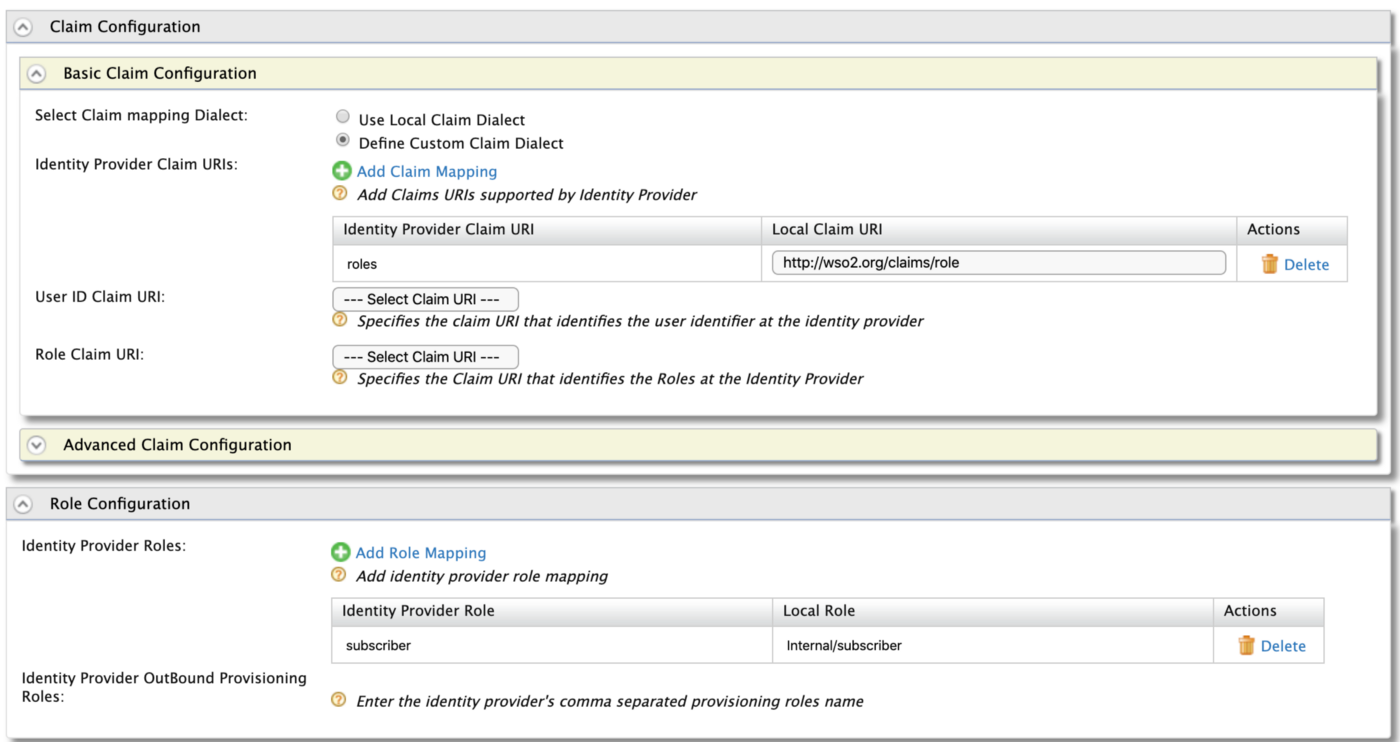
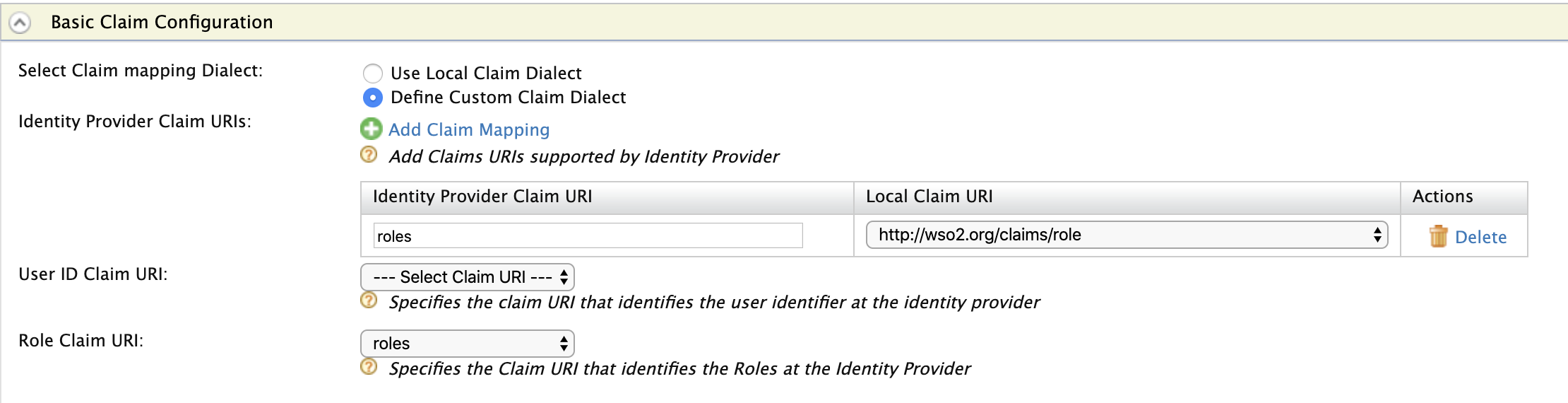
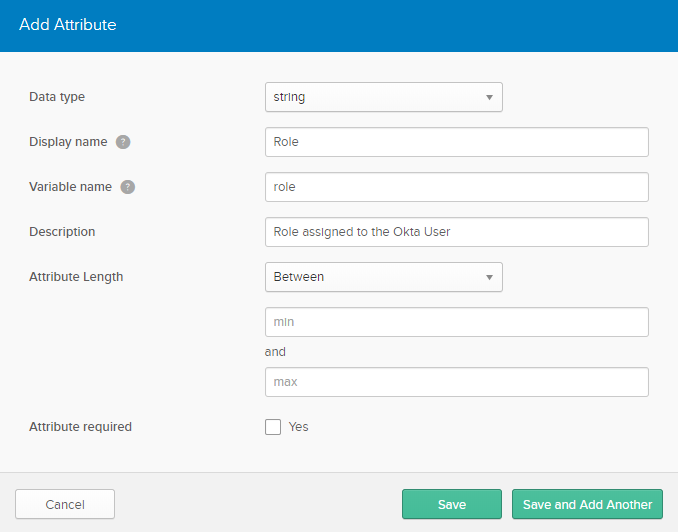
Wso2 Api Manager Okta Saml2 Sso Stackcheats Learn how to secure apis with wso2 api manager. explore features, access control, encryption, and best practices for scalable, compliant api management. In this guide, we explain how to integrate the wso2 api manager with an external identity and access management server (iam) using the okta oauth authorization server to manage the oauth clients and tokens required by wso2 api manager. After the successful creation of our demo application, let’s direct to production keys tab to generate consumer secrets and access tokens using okta third party key manager. These entities allow diverse software programs to interact and distribute data, thus becoming pivotal components of web and mobile apps we use today. the proliferation of api usage necessitates stringent security measures, leading us to explore the solutions provided by wso2.
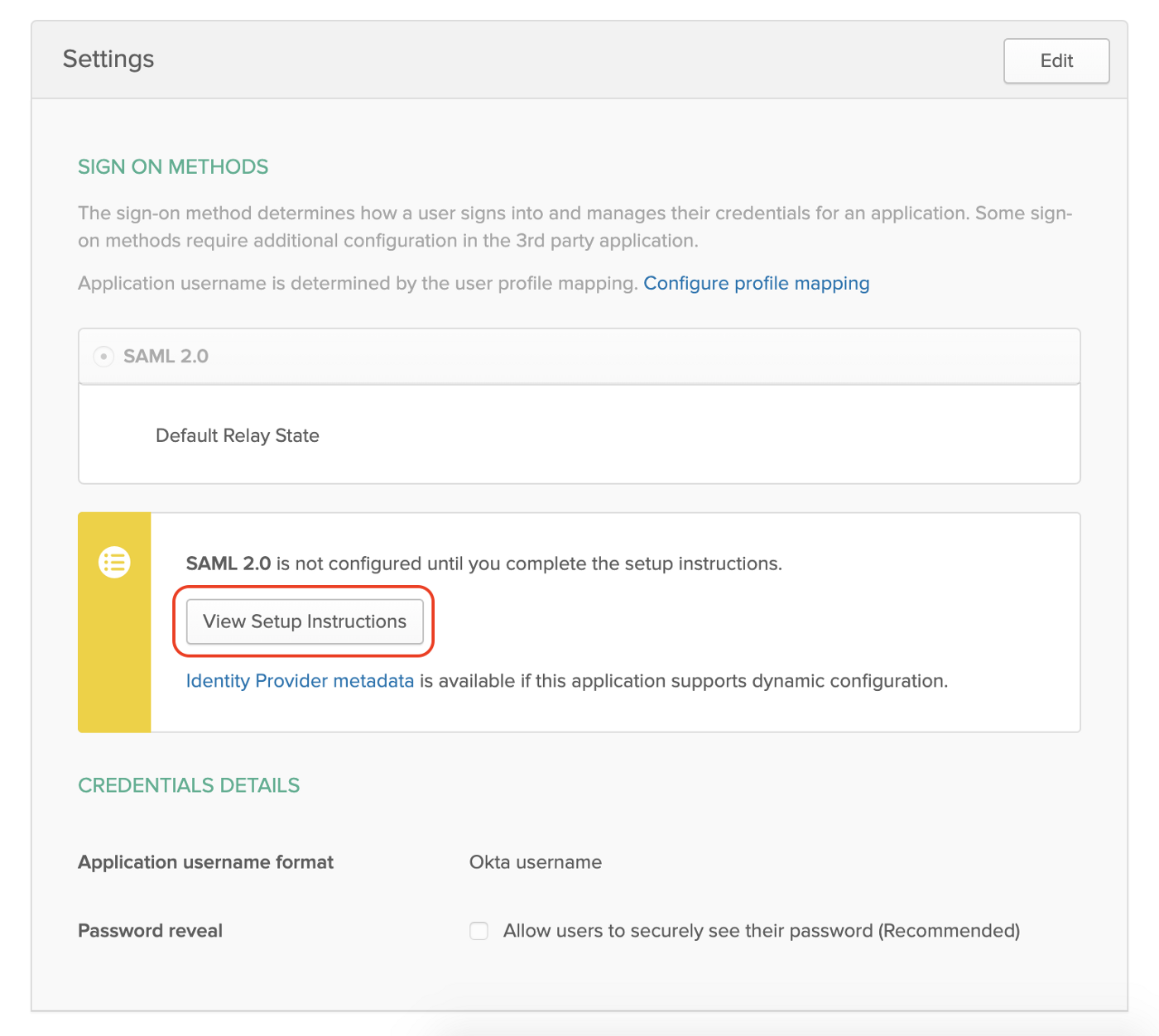
Wso2 Api Manager Okta Saml2 Sso Stackcheats After the successful creation of our demo application, let’s direct to production keys tab to generate consumer secrets and access tokens using okta third party key manager. These entities allow diverse software programs to interact and distribute data, thus becoming pivotal components of web and mobile apps we use today. the proliferation of api usage necessitates stringent security measures, leading us to explore the solutions provided by wso2.
Comments are closed.