Securely Passing Secrets Between Github Action Jobs A Simple Guide
How To Protect Secrets When Using Github Actions Securely passing secrets between github action jobs: a simple guide recently, i was working on a project that required passing a github app authentication token between two jobs. A detailed walkthrough of securely moving sensitive outputs across jobs in github actions.

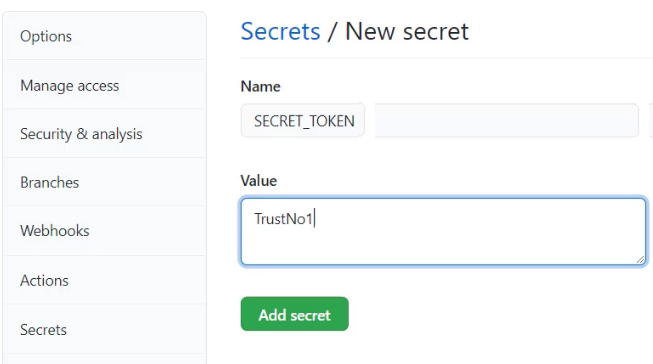
8 Github Actions Secrets Management Best Practices To Follow Stepsecurity According to github actions documentation the recommended way is to use a secret store: set up a secret store to store the secret that you will generate during your workflow. When trying to pass a secret or masked variable between jobs in github actions using outputs, it will say "warning: skip output '' since it may contain secrets". this tutorial aims to provide a reasonable solution for this. Learn how to create secrets at the repository, environment, and organization levels for github actions workflows. Passing information between jobs in github actions can really clean up and streamline your ci cd workflows. whether you are passing api keys, dynamic values, or build artifacts, job outputs give you flexible and secure ways to handle data across jobs.

How To Use Github Actions Secrets To Hide Sensitive Data Learn how to create secrets at the repository, environment, and organization levels for github actions workflows. Passing information between jobs in github actions can really clean up and streamline your ci cd workflows. whether you are passing api keys, dynamic values, or build artifacts, job outputs give you flexible and secure ways to handle data across jobs. In this scenario the job output will probably return something like this. this occurs because the secret that contains the ssh private key was not passed from the caller workflow to the reusable workflow. the fix is easy. we simply just need to add secrets: inherit to the caller workflow. When working with github actions, your workflows often require api keys, tokens, or credentials for deployments and integrations. storing these securely is crucial — leaking secrets can compromise your entire system. this guide explains how to manage secrets in github actions and the best practices for keeping workflows safe. If you have a job linked to an environment you should act as if all actions in that job could have access to all the environment secrets. so do not mix actions with different levels of access to your secrets. Github actions allows you to securely reference secrets in workflows to manage sensitive data like api keys, tokens, and other confidential information. below are examples and guidelines on how to use secrets effectively.
How To Use Github Actions Secrets To Hide Sensitive Data In this scenario the job output will probably return something like this. this occurs because the secret that contains the ssh private key was not passed from the caller workflow to the reusable workflow. the fix is easy. we simply just need to add secrets: inherit to the caller workflow. When working with github actions, your workflows often require api keys, tokens, or credentials for deployments and integrations. storing these securely is crucial — leaking secrets can compromise your entire system. this guide explains how to manage secrets in github actions and the best practices for keeping workflows safe. If you have a job linked to an environment you should act as if all actions in that job could have access to all the environment secrets. so do not mix actions with different levels of access to your secrets. Github actions allows you to securely reference secrets in workflows to manage sensitive data like api keys, tokens, and other confidential information. below are examples and guidelines on how to use secrets effectively.

How To Use Github Actions Secrets To Hide Sensitive Data If you have a job linked to an environment you should act as if all actions in that job could have access to all the environment secrets. so do not mix actions with different levels of access to your secrets. Github actions allows you to securely reference secrets in workflows to manage sensitive data like api keys, tokens, and other confidential information. below are examples and guidelines on how to use secrets effectively.
Comments are closed.