Secure Your Software Supply Chain Detect Third Party Risks
Communications Authority Of Kenya Cautions On Supply Chain Risks In Identify hidden risks in third party and open source software. cycognito helps secure your full software supply chain. Master software supply chain security with 12 proven best practices, latest threat vectors, and mistakes to avoid.

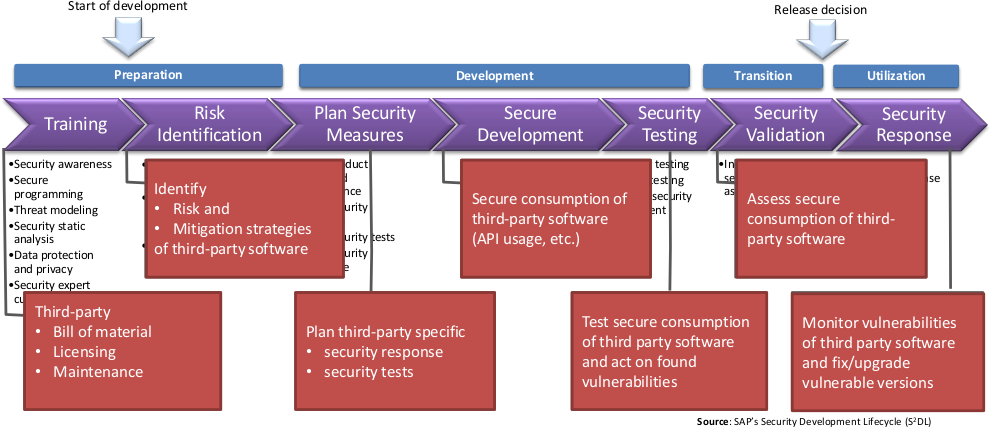
What Is Software Supply Chain Security And Why Does It Matter Explore modern software supply chain security. learn to mitigate third party risks with sboms, nist frameworks, and runtime protection. Modern organizations depend on third party vendors and supply chains, making their security critical. learn best practices for managing third party and ecosystem risks. By understanding the risks inherent in third party code and implementing proven best practices, you can protect your organization and build software that is secure from the start. Learn how to assess third party software risks with our comprehensive 7 step guide. protect your business from supply chain attacks and vulnerabilities.

Supply Chain Security Managing Risks From Third Party Vendors It By understanding the risks inherent in third party code and implementing proven best practices, you can protect your organization and build software that is secure from the start. Learn how to assess third party software risks with our comprehensive 7 step guide. protect your business from supply chain attacks and vulnerabilities. Learn how software supply chain security protects your infrastructure throughout the software lifecycle, plus common threats and best practices for your cloud. Sboms (software bills of materials) provide a single source of truth about what is in your software, helping teams track components, vulnerabilities, and changes over time. binary analysis is essential for securing third party, legacy, or closed source components where source code is unavailable, reducing blind spots in the supply chain. This ultimate guide tells everything you need to know to successfully identify, analyze & mitigate the most common software supply chain security risks. Learn how to secure your software supply chain with real world examples, key risks, and actionable strategies to protect your code, tools, and dependencies.
Comments are closed.