Secure Your Openstack Infrastructure

Infrastructure Deployment Demo Rackspace Openstack Documentation This book provides best practices and conceptual information about securing an openstack cloud. this guide was last updated during the train release, documenting the openstack train, stein, and rocky releases. it may not apply to eol releases (for example newton). This document provides advice and good practice information for hardening the security of your red hat openstack platform deployment, with a focus on director based deployments.
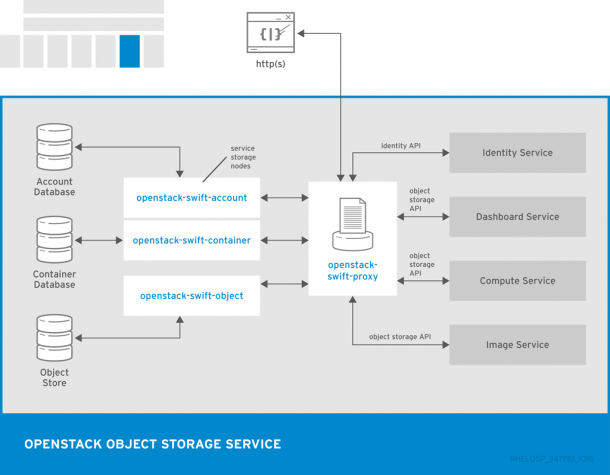
Openstack Infrastructure Diagram By taking a proactive and comprehensive approach to openstack security, organizations can help ensure the safety and reliability of their cloud infrastructure. in conclusion, securing your openstack environment is crucial for upholding the integrity and dependability of your cloud infrastructure. In this blog post, we’ll explore actionable steps to safeguard your openstack deployment — and show how atmosphere openstack makes applying these practices more seamless. There are various strategies for ensuring your openstack environment is secure. following the security best practices outlined in this article can keep your infrastructure safe and secure. Private cloud environments, especially openstack based ones, face unique security challenges. this guide outlines the eight main security controls you need to focus on for data protection, compliance, and operational efficiency. here’s a quick summary of what we’ll go over:.
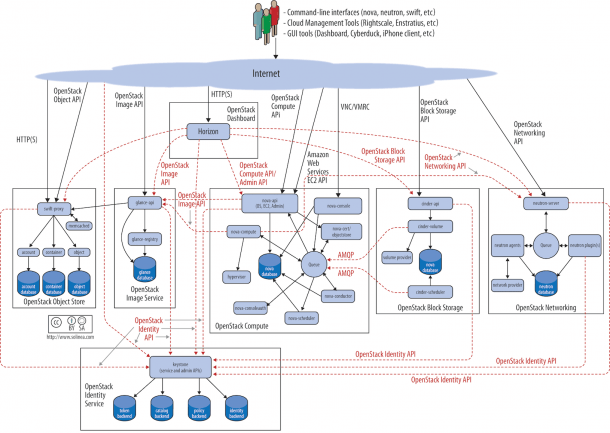
Openstack Infrastructure Diagram There are various strategies for ensuring your openstack environment is secure. following the security best practices outlined in this article can keep your infrastructure safe and secure. Private cloud environments, especially openstack based ones, face unique security challenges. this guide outlines the eight main security controls you need to focus on for data protection, compliance, and operational efficiency. here’s a quick summary of what we’ll go over:. Securing your openstack api is essential for protecting your cloud infrastructure. implement authentication methods such as tokens or certificates and restrict api access to specific ip addresses. The purpose of this document is to provide the best practice guidelines for deploying a secure openstack cloud. The biggest danger is a new “zero day” vulnerability that could exist in your openstack deployment right now, unbeknownst to you or openstack contributors. this requires a proactive approach to securing applications in the openstack toolset, as i discuss in the following section. The guide covers topics including compute and storage hardening, rate limiting, compliance, and cryptography; it is the starting point for anyone looking to securely deploy openstack.
Securing Your Infrastructure Best Practices Engineerhow It Securing your openstack api is essential for protecting your cloud infrastructure. implement authentication methods such as tokens or certificates and restrict api access to specific ip addresses. The purpose of this document is to provide the best practice guidelines for deploying a secure openstack cloud. The biggest danger is a new “zero day” vulnerability that could exist in your openstack deployment right now, unbeknownst to you or openstack contributors. this requires a proactive approach to securing applications in the openstack toolset, as i discuss in the following section. The guide covers topics including compute and storage hardening, rate limiting, compliance, and cryptography; it is the starting point for anyone looking to securely deploy openstack.
Comments are closed.