Secure Your Api Gateway With Amazon Cognito User Pools Step By Step Aws Tutorial

Secure Api Access With Amazon Cognito Federated Identities Amazon In this section, we describe how to create a user pool, how to integrate an api gateway api with the user pool, and how to invoke an api that's integrated with the user pool. Whether you’re new to aws or an experienced developer, this step by step walkthrough will give you a practical foundation for implementing secure, authenticated api access using aws services.
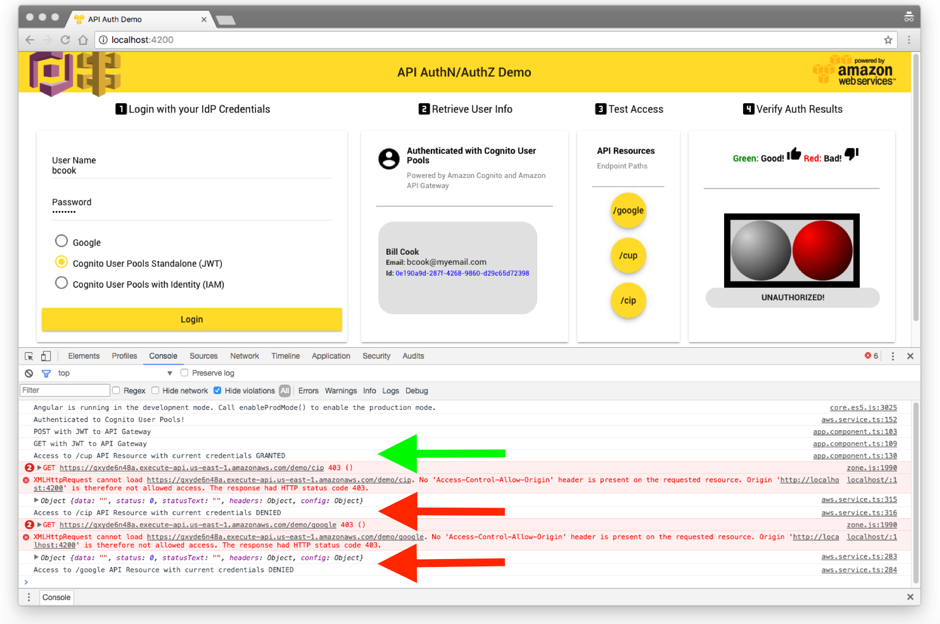
Secure Api Access With Amazon Cognito Federated Identities Amazon Learn how to secure aws api gateway with cognito. this guide covers setting up a user pool and configuring the api authorizer for enhanced security. Use custom scopes with amazon cognito and api gateway to provide differentiated levels of access to your api resources. configure a resource server and oauth 2.0 custom scopes in a user pool. In this article, i will walk through a practical and production ready approach to secure an aws api gateway endpoint using amazon cognito and the native jwt authorizer, without lambda authorizers or custom authentication logic. The website content provides a comprehensive guide on securing apis using amazon cognito as an authorizer for aws api gateway, including steps for configuring cognito user pools, setting up oauth 2.0 in postman, and testing secure api access.

Secure Api Access With Amazon Cognito Federated Identities Amazon In this article, i will walk through a practical and production ready approach to secure an aws api gateway endpoint using amazon cognito and the native jwt authorizer, without lambda authorizers or custom authentication logic. The website content provides a comprehensive guide on securing apis using amazon cognito as an authorizer for aws api gateway, including steps for configuring cognito user pools, setting up oauth 2.0 in postman, and testing secure api access. In this blog, we will build a secure serverless api using amazon api gateway, aws lambda, and amazon cognito, along with python lambda code, terraform infrastructure setup, and jwt token validation. Securing your api gateway endpoints using aws cognito is simple and straightforward. the process we went through was creating an api with api gateway, then creating a user pool in cognito, and creating and attaching a jwt authorizer to our endpoints. We’ll cover steps like configuring a cognito user pool for api gateway, setting up oauth 2.0 authorization in postman to obtain tokens, and accessing protected api endpoints. by. Guide to securing rest apis with amazon cognito, including user pool creation, enabling endpoint access, and configuring jwt token authorizers.
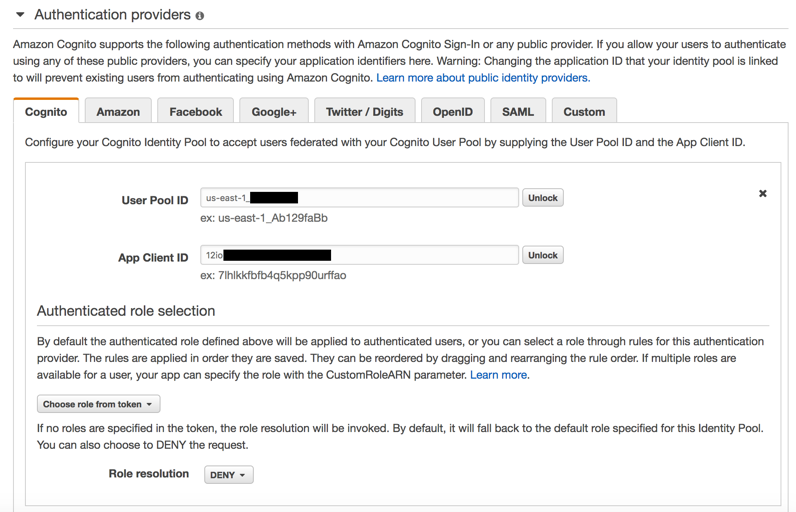
Secure Api Access With Amazon Cognito Federated Identities Amazon In this blog, we will build a secure serverless api using amazon api gateway, aws lambda, and amazon cognito, along with python lambda code, terraform infrastructure setup, and jwt token validation. Securing your api gateway endpoints using aws cognito is simple and straightforward. the process we went through was creating an api with api gateway, then creating a user pool in cognito, and creating and attaching a jwt authorizer to our endpoints. We’ll cover steps like configuring a cognito user pool for api gateway, setting up oauth 2.0 authorization in postman to obtain tokens, and accessing protected api endpoints. by. Guide to securing rest apis with amazon cognito, including user pool creation, enabling endpoint access, and configuring jwt token authorizers.
Comments are closed.