Secure Software Development Life Cycle Download Scientific Diagram

Secure Software Development Life Cycle Pdf Software Development Developers need to be aware of potential security concerns at every stage of the sdlc to ensure the security of the software product. In this section, some of the key security concerns that must be addressed in each phase of the devsecops life cycle are identified. figure 1 illustrates these phases, integrating the development (dev), security (sec), and operations (ops) aspects into a unified model.

1 Secure Software Development Life Cycle Pdf Computer Security The process of using hypothetical scenarios, system diagrams, and testing to help secure systems and data. by identifying vulnerabilities, helping with risk assessment, and suggesting corrective action, threat modelling helps improve cybersecurity and trust in key business systems. Incorporating security at any level of the software development life cycle (sdlc) has become an urgent requirement. several methodologies, strategies, and models have been proposed and. When trying to incorporate security into a program, software developers face either too much theoretical information that they can't apply or exhaustive and discouraging recommendation lists . Download scientific diagram | diagram showing various phases of secure software development life cycle from publication: constraints that hinders secure software.

5 Phases Of Secure Software Development Life Cycle Pdf When trying to incorporate security into a program, software developers face either too much theoretical information that they can't apply or exhaustive and discouraging recommendation lists . Download scientific diagram | diagram showing various phases of secure software development life cycle from publication: constraints that hinders secure software. In this study, a secured database monitoring method was proposed to improve data backup and recovery operations in cloud computing. Download scientific diagram | the secure software development life cycle from publication: a review of threat modelling and its hybrid approaches to software security testing | as. The four main phases of the secure development life cycle have been considered: identification of requirements, design, implementation, and verification and validation. Even though some security experts can be hired for software development, the entire development process has to be still conducted by professionals who are not much exposed to security related design and development in their career.
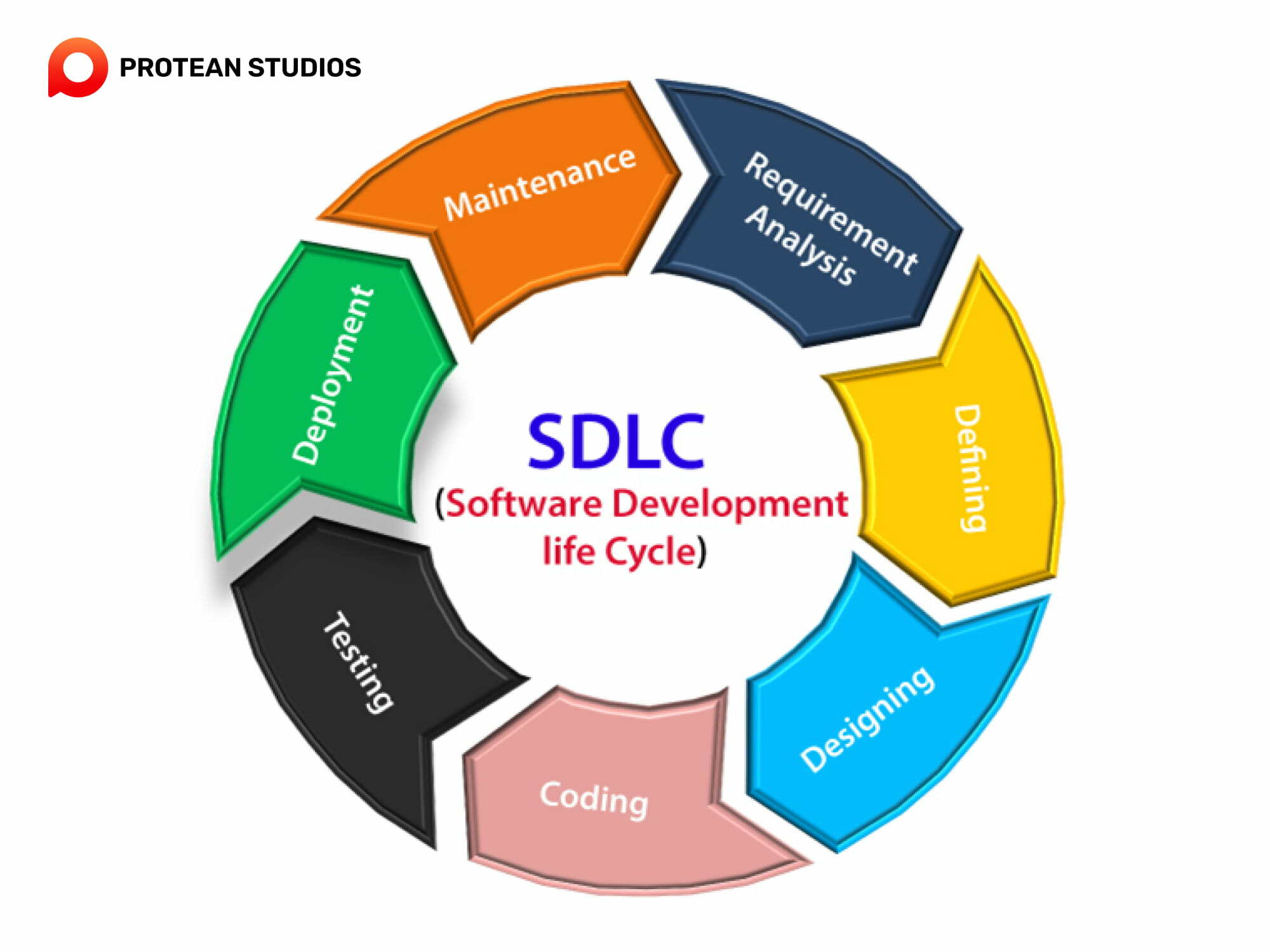
Software Development Life Cycle Diagram Software Development Life In this study, a secured database monitoring method was proposed to improve data backup and recovery operations in cloud computing. Download scientific diagram | the secure software development life cycle from publication: a review of threat modelling and its hybrid approaches to software security testing | as. The four main phases of the secure development life cycle have been considered: identification of requirements, design, implementation, and verification and validation. Even though some security experts can be hired for software development, the entire development process has to be still conducted by professionals who are not much exposed to security related design and development in their career.
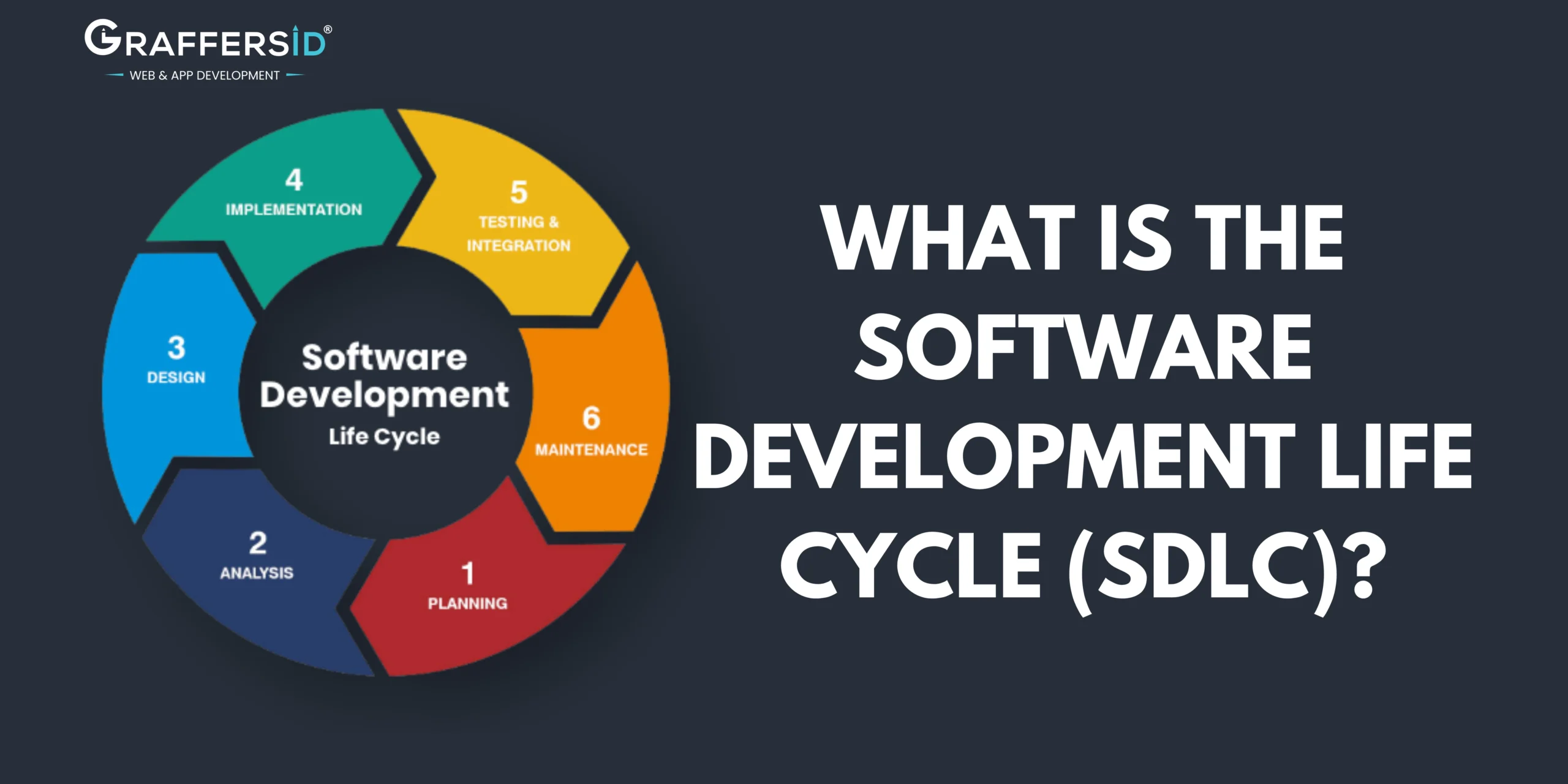
Software Development Life Cycle Diagram Software Development Life The four main phases of the secure development life cycle have been considered: identification of requirements, design, implementation, and verification and validation. Even though some security experts can be hired for software development, the entire development process has to be still conducted by professionals who are not much exposed to security related design and development in their career.
Comments are closed.