Secure Shell Ssh Cyberhoot

318 Secure Shell Ssh Images Stock Photos 3d Objects Vectors Secure shell (ssh) is a cryptographic network communications protocol for operating network services securely over an unsecured network. typical applications include remote command line, login, and remote command execution, but any network service can be secured with ssh. The ssh protocol (also referred to as secure shell) is a method for secure remote login from one computer to another. it provides several alternative options for strong authentication, and it protects communications security and integrity with strong encryption.

Secure Shell Ssh Explained Encryption Ports Connecting Ssh (secure shell or secure socket shell) is a network protocol that gives users particularly systems administrators a secure way to access a computer over an unsecured network. ssh also refers to the suite of utilities that implement the ssh protocol. Ssh is a cryptographic network protocol that gives users, particularly system administrators, a secure way to access a computer over an unsecured network. ssh provides strong authentication and encrypted data communications between two computers connecting over an open network such as the internet. Ssh stands for secure shell, and it’s a protocol that allows you to connect to a remote computer securely over an unsecured network. ssh provides a secure channel between two computers, ensuring that data transferred between them is encrypted and protected from attackers. Ssh revolutionized secure remote computing when created in 1995 as an encrypted successor to notoriously insecure protocols like telnet and rlogin. rigorously hardened ssh setups prevent unauthorized access via encryption keys, restrictive access policies and intrusion detection.

Intro To Ssh Secure Shell Part 1 What Is Ssh And Why Do I Want To Ssh stands for secure shell, and it’s a protocol that allows you to connect to a remote computer securely over an unsecured network. ssh provides a secure channel between two computers, ensuring that data transferred between them is encrypted and protected from attackers. Ssh revolutionized secure remote computing when created in 1995 as an encrypted successor to notoriously insecure protocols like telnet and rlogin. rigorously hardened ssh setups prevent unauthorized access via encryption keys, restrictive access policies and intrusion detection. Learn what is ssh, how to set up, secure, and configure ssh for remote access with our detailed guide. includes tips on key based authentication, port forwarding, and setting up 2fa and more. Ssh is short for secure shell or secure socket shell. according to , the secure shell protocol is a cryptographic network protocol for operating network services securely over an unsecured network. sshd is short for secure shell daemon. This guide covers both the fundamentals and the practical details required to work effectively with ssh. in addition to basic connection methods, it explains how ssh authentication works, how trust is established using keys, and how to configure ssh securely on both the server and client side. Ssh, or secure shell protocol, is like a secure key to a computer that’s physically located at a distance to you. it uses encryption as the main way to ensure that your data is protected when sent over potentially insecure networks.
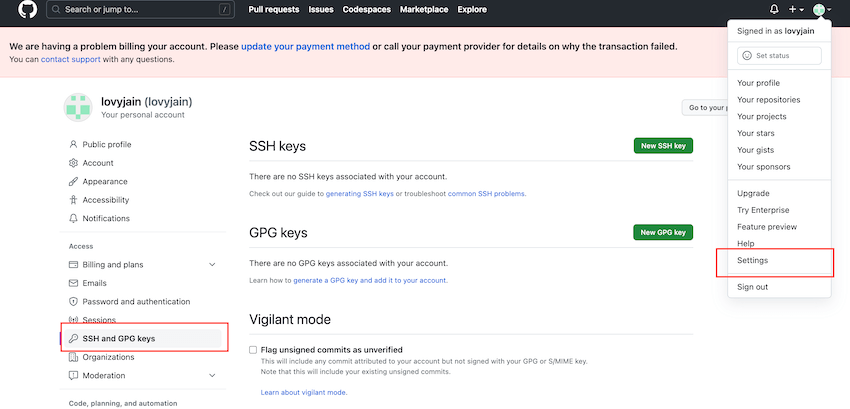
Secure Shell Ssh A Comprehensive Guide To Secure Login Learn what is ssh, how to set up, secure, and configure ssh for remote access with our detailed guide. includes tips on key based authentication, port forwarding, and setting up 2fa and more. Ssh is short for secure shell or secure socket shell. according to , the secure shell protocol is a cryptographic network protocol for operating network services securely over an unsecured network. sshd is short for secure shell daemon. This guide covers both the fundamentals and the practical details required to work effectively with ssh. in addition to basic connection methods, it explains how ssh authentication works, how trust is established using keys, and how to configure ssh securely on both the server and client side. Ssh, or secure shell protocol, is like a secure key to a computer that’s physically located at a distance to you. it uses encryption as the main way to ensure that your data is protected when sent over potentially insecure networks.

Secure Shell Or Ssh This guide covers both the fundamentals and the practical details required to work effectively with ssh. in addition to basic connection methods, it explains how ssh authentication works, how trust is established using keys, and how to configure ssh securely on both the server and client side. Ssh, or secure shell protocol, is like a secure key to a computer that’s physically located at a distance to you. it uses encryption as the main way to ensure that your data is protected when sent over potentially insecure networks.
Intro To Ssh Secure Shell 101 Exercise Unosquare
Comments are closed.