Secure Devops Three Keys For Success
5 Keys To A Secure Devops Workflow How can companies measure the success of their devops security initiatives? success can be measured by tracking incident resolution time, vulnerability trends, compliance kpis such as audit pass rates, and using security scorecards and dashboards for visibility. They must provide holistic relief to overworked teams trying to secure apps at the feature request, commit, pull request, and ci cd stages. keeping these three factors in mind, companies may use devsecops to its full potential as a game changer.

Getting Started With Secure Devops Devops 3 key success factors. the value you will receive from integrating security testing into devops depends on how vastly it is adopted by your development teams and how many vulnerabilities. By keeping these three elements in mind, organizations can fulfill devsecops’ potential as a true game changer. as devsecops continues to cross the chasm to more universal adoption, organizations can look to earlier adopters for guidance on how to do devsecops right. Imperatives to think about as you develop your secure devops strategy. developers want to work within a fully automated pipeline, where they can write elegant, game changing code. The need for security often stems from three key areas of risk: 1. compliance: implement the latest government regulations. first and foremost, your organization needs to be compliant with the latest federal and sec regulations, standards, and policies.
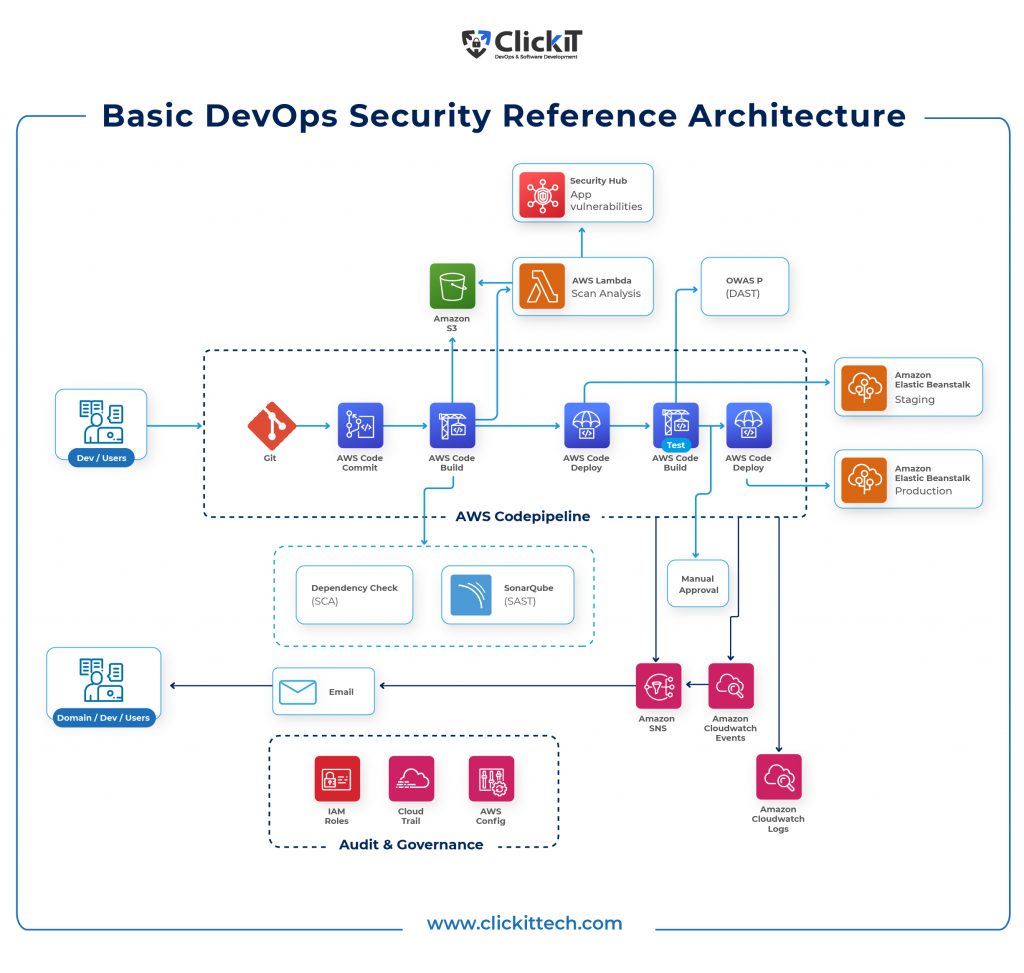
Devops Security Best Practices Tools And Frameworks Imperatives to think about as you develop your secure devops strategy. developers want to work within a fully automated pipeline, where they can write elegant, game changing code. The need for security often stems from three key areas of risk: 1. compliance: implement the latest government regulations. first and foremost, your organization needs to be compliant with the latest federal and sec regulations, standards, and policies. In conclusion, there is potential for organizations to create a secure software delivery pipeline that promotes teamwork, simplifies workflows, and reduces security vulnerabilities by following the devsecops best practices. Unlike traditional security approaches that treat security as a final gate, devops security embeds security controls, automated testing, and continuous monitoring into every stage of the development pipeline. Securing account credentials, api tokens, and keys is vital to keeping the it infrastructure safe. without proper secret management, these sensitive details could end up in the wrong hands and cause serious issues. Enterprises must invest significant time and effort in changing their culture, tools and staff skill set to adapt and get the best results from devops while remaining secure. information security professionals must realize that, more than any tool or technology, their mind set must evolve to survive and remain relevant in a devops world. endnotes.

5 Tips For Creating A Secure Devops Culture Fastly In conclusion, there is potential for organizations to create a secure software delivery pipeline that promotes teamwork, simplifies workflows, and reduces security vulnerabilities by following the devsecops best practices. Unlike traditional security approaches that treat security as a final gate, devops security embeds security controls, automated testing, and continuous monitoring into every stage of the development pipeline. Securing account credentials, api tokens, and keys is vital to keeping the it infrastructure safe. without proper secret management, these sensitive details could end up in the wrong hands and cause serious issues. Enterprises must invest significant time and effort in changing their culture, tools and staff skill set to adapt and get the best results from devops while remaining secure. information security professionals must realize that, more than any tool or technology, their mind set must evolve to survive and remain relevant in a devops world. endnotes.
Comments are closed.