Secure Coding Practices Essentials Of Secure Development Code Reviews Penetration Testing

Secure Coding Practices Pdf Password Http Cookie This guide provides coding practices that can be translated into coding requirements without the need for the developer to have an in depth understanding of security vulnerabilities and exploits. It defines specific security practices and requirements for each phase of development, emphasizing training, threat modeling, secure coding standards, security testing, and incident response.
Secure Coding Best Practices Pdf Learn how to run secure code reviews that catch vulnerabilities early. explore process steps, tools, owasp tips, and real world coding practices. We’ll examine eight design principles that govern secure coding and how to apply them to your own work. we’ll discuss how poor design choices drive implementation in coding. Best practices for secure coding include input validation, output encoding, least privilege access, secure authentication, code reviews, and threat modeling. Two powerful tools in our security arsenal are secure code reviews and penetration testing (pen testing). while often viewed as separate processes, when used in tandem, they provide a comprehensive view of your application’s security deficiencies.

Secure Coding Practices Testing In Penetration Testing Vertex Cyber Best practices for secure coding include input validation, output encoding, least privilege access, secure authentication, code reviews, and threat modeling. Two powerful tools in our security arsenal are secure code reviews and penetration testing (pen testing). while often viewed as separate processes, when used in tandem, they provide a comprehensive view of your application’s security deficiencies. Discover how proper secure coding practices can prevent costly data breaches and vulnerabilities. this comprehensive guide covers essential security principles, owasp top 10 mitigations, and language specific techniques that every developer needs to implement in their sdlc. This blog will explore the importance of secure coding practices testing within penetration testing, offering insights into how it enhances software security and mitigates risks. By following owasp secure coding practices and adopting a mix of manual review, automated tools, and hands on learning, you’ll reduce the most common risks and build software your users can trust. Secure coding is the practice of developing software resistant to vulnerabilities by applying security practices, techniques, and tools early in development.
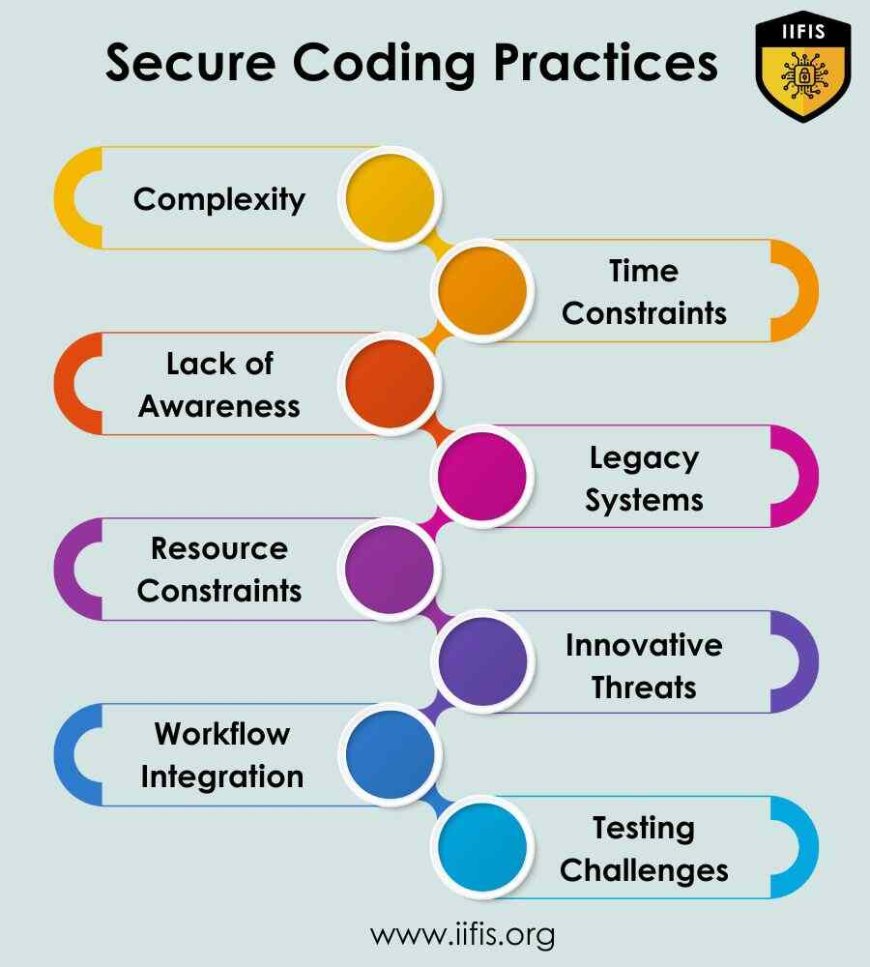
Secure Coding Practices And Development Lifecycle Iifis Discover how proper secure coding practices can prevent costly data breaches and vulnerabilities. this comprehensive guide covers essential security principles, owasp top 10 mitigations, and language specific techniques that every developer needs to implement in their sdlc. This blog will explore the importance of secure coding practices testing within penetration testing, offering insights into how it enhances software security and mitigates risks. By following owasp secure coding practices and adopting a mix of manual review, automated tools, and hands on learning, you’ll reduce the most common risks and build software your users can trust. Secure coding is the practice of developing software resistant to vulnerabilities by applying security practices, techniques, and tools early in development.
Comments are closed.