Secure Coding Input Validation

Input Validation Client Side Server Side Cybersecurity Deterrent Learn how to perform input validation to prevent malformed data from entering your applications and triggering attacks. this cheat sheet covers syntactic and semantic validation, allow list and block list, unicode text, file upload, and more. These are two complementary security controls that work together to prevent injection attacks: input validation acts as the first line of defense by rejecting malformed data at entry points, while output encoding provides context aware protection when displaying or using that data.
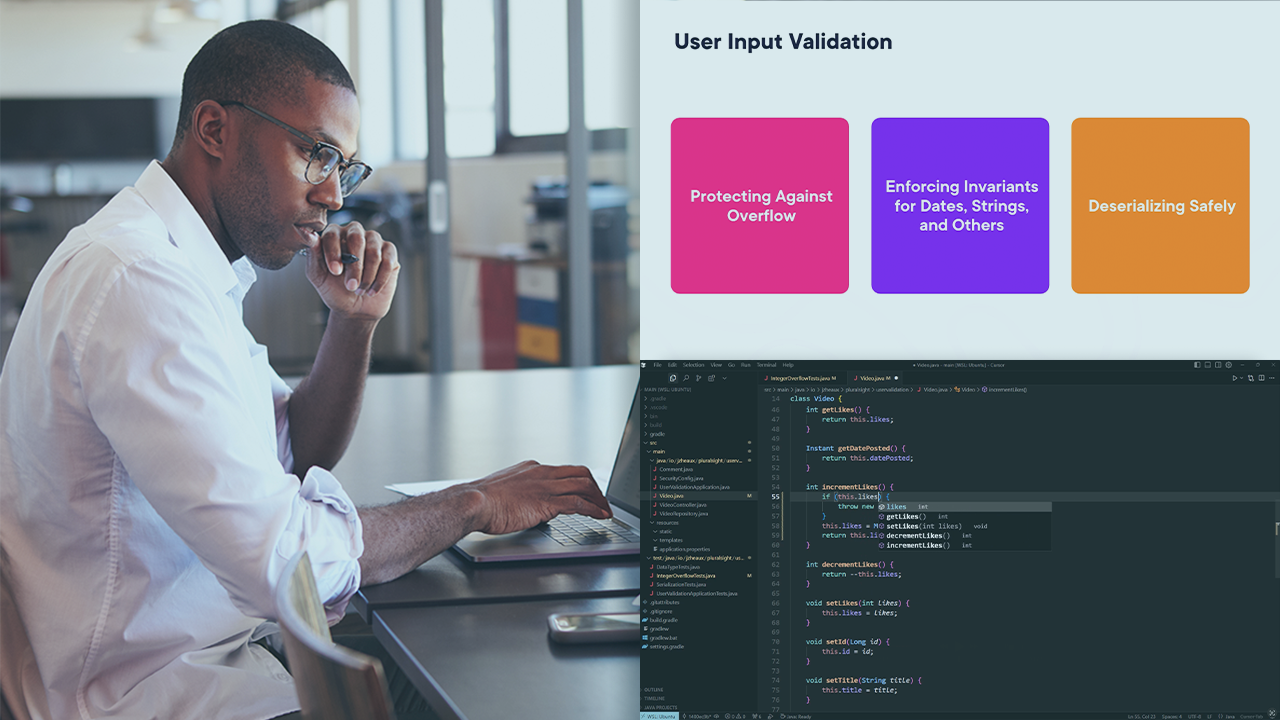
User Input Validation For Java Applications Learn why input validation and sanitization are critical for application security. discover best practices to prevent xss, sql injection, and other common attacks. Secure coding practices contribute to application level defenses (e.g., input validation, output encoding, access control), which should complement network level security (firewalls), platform hardening, and operational security measures. Effective input validation for secure coding involves using multiple methods to ensure that incoming data is accurate, safe, and structured correctly. these techniques help maintain data integrity and prevent data corruption caused by invalid or malicious inputs. Learn how to validate user input securely: allowlists vs denylists, validation strategies, and preventing injection attacks.

Understanding Input Validation And Secure Coding Practices Stellastra Effective input validation for secure coding involves using multiple methods to ensure that incoming data is accurate, safe, and structured correctly. these techniques help maintain data integrity and prevent data corruption caused by invalid or malicious inputs. Learn how to validate user input securely: allowlists vs denylists, validation strategies, and preventing injection attacks. Reuse shared validation functions across your codebase for consistency. following this checklist helps block injection attacks, reduce bugs, and keep your app secure by design. This article explores the fundamentals of input validation, examines secure coding practices, and highlights the techniques required to build reliable, secure applications. Learn why secure input validation is critical for blocking attacks like sqli and xss, and explore strategies to strengthen your application security. Use the server or framework’s session management controls. the application should recognize only these session identifiers as valid. use a single site wide component to check access authorization. this includes libraries that call external authorization services.

Secure Coding Practices 1 User Input Validation Vaadin Reuse shared validation functions across your codebase for consistency. following this checklist helps block injection attacks, reduce bugs, and keep your app secure by design. This article explores the fundamentals of input validation, examines secure coding practices, and highlights the techniques required to build reliable, secure applications. Learn why secure input validation is critical for blocking attacks like sqli and xss, and explore strategies to strengthen your application security. Use the server or framework’s session management controls. the application should recognize only these session identifiers as valid. use a single site wide component to check access authorization. this includes libraries that call external authorization services.

Why Input Validation Matters In Secure Coding Stop Sqli Xss More Learn why secure input validation is critical for blocking attacks like sqli and xss, and explore strategies to strengthen your application security. Use the server or framework’s session management controls. the application should recognize only these session identifiers as valid. use a single site wide component to check access authorization. this includes libraries that call external authorization services.

Input Validation For Secure Coding Essential Guide In 2026
Comments are closed.